What is Vidar Stealer?
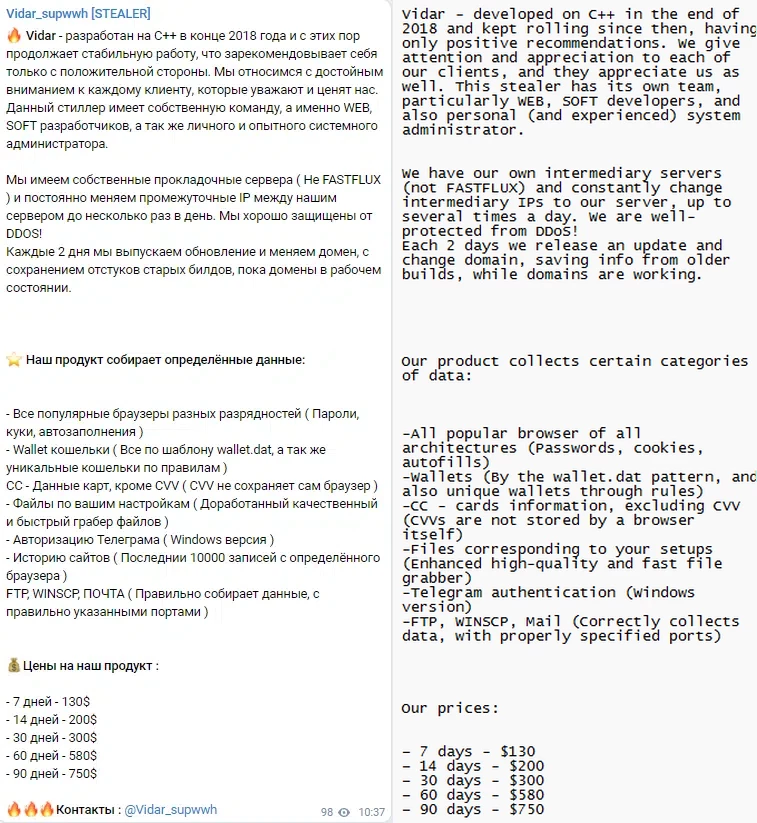
Vidar is a stealer malware that aims at personal information and cryptocurrency wallets data present in the attacked environment. Observed in the wild since 2018, it is likely an offspring or a direct evolution of Arkei trojan, which served for pretty much the same purpose. A lot of factors point at the fact Vidar originates from Russia, despite the absence of any official claims. This malware is sold in the Darknet, by the model “Malware-as-a-service”, from the official developer’s website. Price tag varies from $130 to $750, depending on the term of the “licence”. Key places for advertisements are hacking forums and Telegram groups.
Vidar stealer is noteworthy for its manner of C2 communication – generally through pages in social networks, such as Telegram, Mastodon, or even Steam. Aside from that, stealers by default perform self-destruction after gathering all the information from the system. In combination with following the latest trends in malware spreading, all this makes Vidar a prolific malware example. Let’s have a more detailed look upon its spreading, and the manner it conducts its activity.
Vidar Stealer Spreading
Throughout its entire history, Vidar consistently used only one method of delivery - email spamming. Other approaches were generally present in less than 10% of cases, and included injecting Vidar into cracked software packages, or deployment through dropper malware. Nonetheless, such a behaviour is no good either, since it sharply extends the list of preventive actions against Vidar malware.
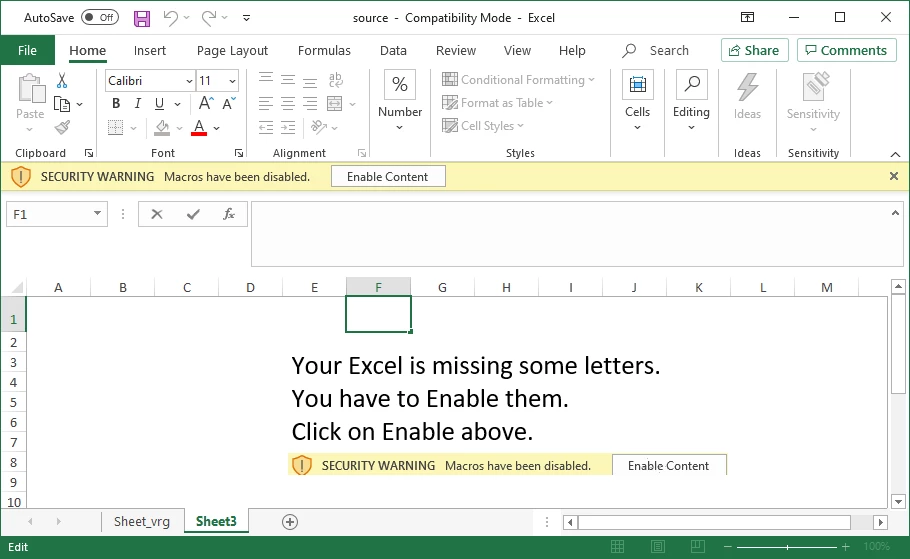
Classic examples of email spam that is used to spread Vidar include a well-done disguise and a malicious attachment. The topic is generally something routine, like invoice for the recent order, delivery notification or a subscription renewal. At the message bottom, there is an attachment which, as the message body says, contains some important details regarding the topic. It is a MS Office document with a macro script inside. Once opened, the document will ask you to enable macros execution, as they are disabled by default. Press “Enable” – and you trigger the script that contacts the malware server and downloads the payload.
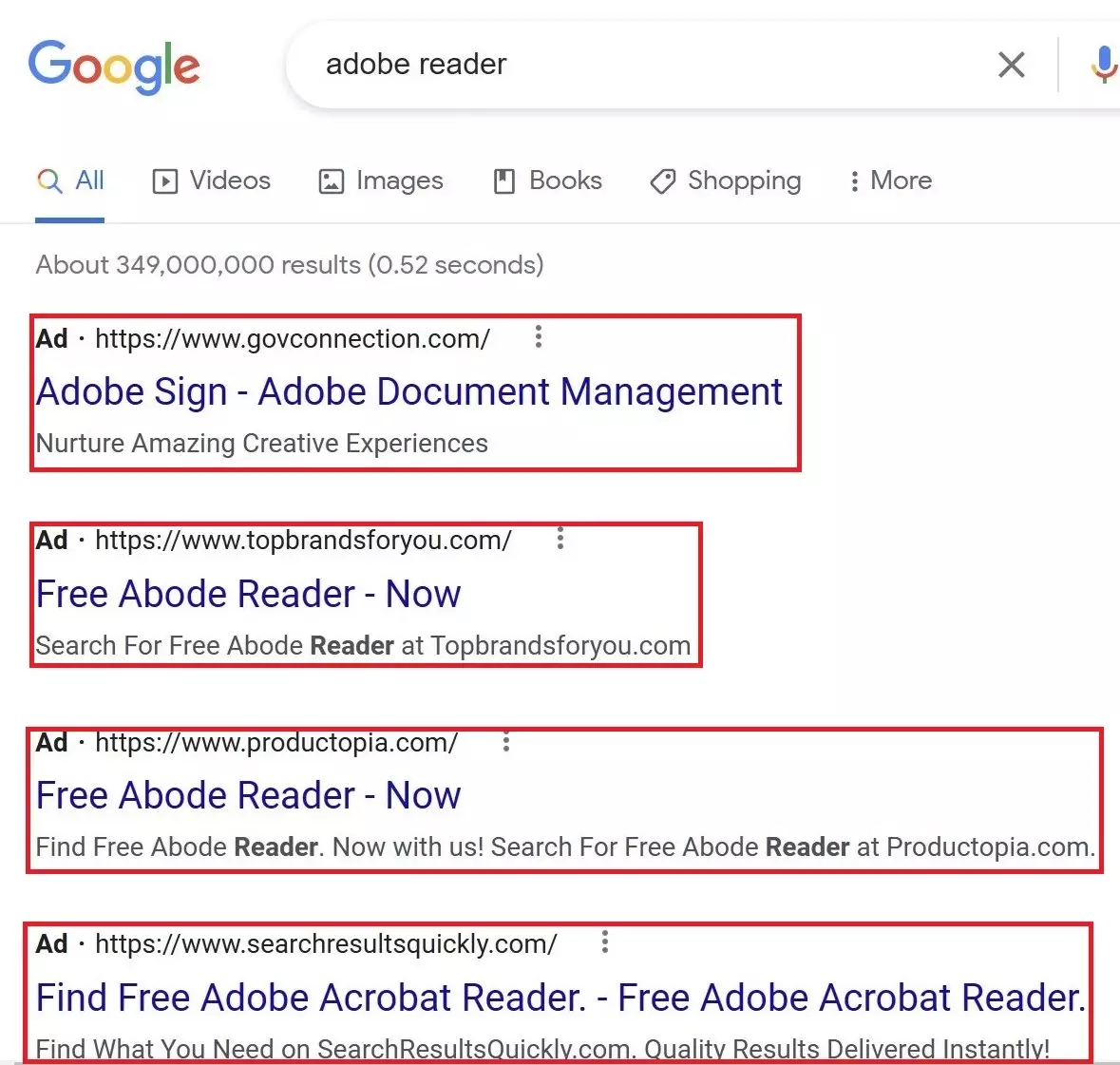
Changes to Microsoft policy on macros execution forced crooks to search for a different way of propagation. Some found a way to circumnavigate the restrictions, while others opted for another method of spreading. Vidar is among them – choosing to spread via malicious Google Search ads. This and numerous other malware opted for this spreading way at the end of January 2023. Alternative way aligns with same email messages, but with archive with malware inside and correspondingly changed topic.
The use of ads in Google Search for malware distribution is not a brand new tactic. We found some records about placing a link to a malicious website in search result ads back in 2013. Such sites copy (or at least try to mimic) the design of a download page for free software. Ad in Google, as you can probably guess, resembles the one that belongs to an original software publisher. A package downloaded from a fake site contains either a downloader script, or a malware itself – both ready to run once you try to launch a thing you tried to download.
Over time, analysts spectate an interesting cooperation between Vidar stealer and STOP/Djvu ransomware. At some point, they started spreading together, also carrying SmokeLoader backdoor. The latter, in turn, tends to bring RedLine stealer and Laplas clipper trojan. As you may suppose, all these things running on a single PC lead to a complete mess. Most likely, Djvu ransomware affiliates try to increase their incomes from a single victim.
Vidar Stealer analysis
First thing that comes into view when you try to analyse Vidar is the tricks it uses to avoid instant detection by both in-system antivirus software and analysis at sites like VirusTotal. Its sample contains a row of null bytes at the beginning of the file in order to bloat its size up to around 700 MB. That exceeds file size limits of anti-malware software, thus they simply skip that file. It is important to mention that such a tactic is applied only in the cases when Vidar arrives within the archive, i.e. via search result malvertising campaign or email with archive attached.
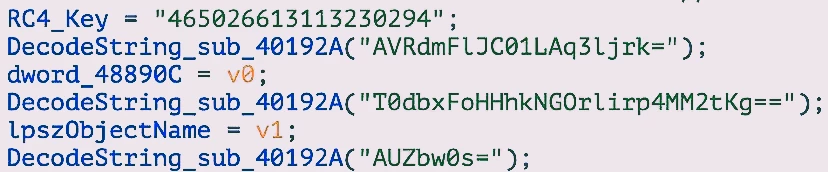
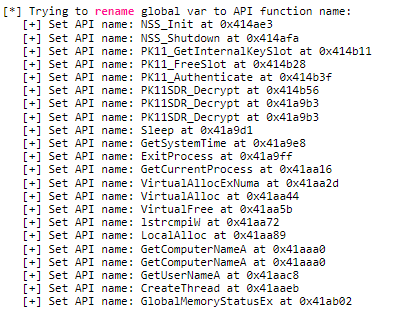
A Vidar sample launched through a macros simply does not require tricking the user into running itself, as macros do everything. The launch, however, is not that simple. Typically for any modern malware sample, it features string encoding (with base64) and encryption, which makes it not that easy analyse. Still, there is nothing extraordinarily strong in these protection measures, and thus it is possible to get clear string samples and analyse malware statically. Another thing to note is that Vidar is commonly packed in a specific way, which is often unique from one sample to another. The loader is, however, the same for all cases – a so-called DerpLoader. It was observed in all samples since early 2021, but before there was no consistency in used loaders.
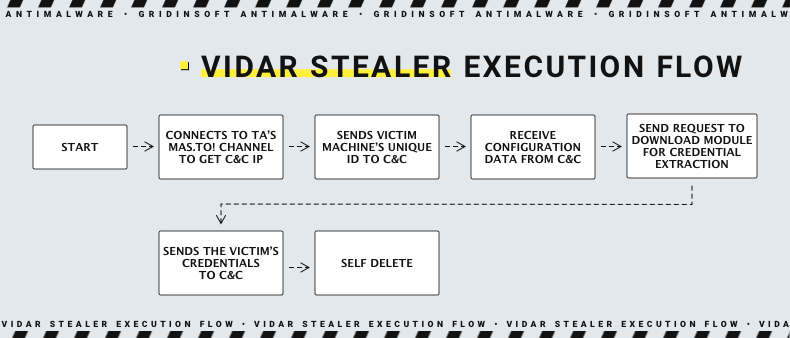
Loader is obviously the first part of Vidar to run. It is in charge of creating a dedicated memory area, preparing the binary and injecting it into that area. The 18-bit decryption key is supplied inside of the loader and is different in each sample. Then, using VirtualAlloc function, the loader creates a memory area and injects there the result of decoding/decryption, simultaneously passing the execution to that area. At that moment, malware is ready to run. First thing it does after the launch is contacting C&C server.
C2 communication
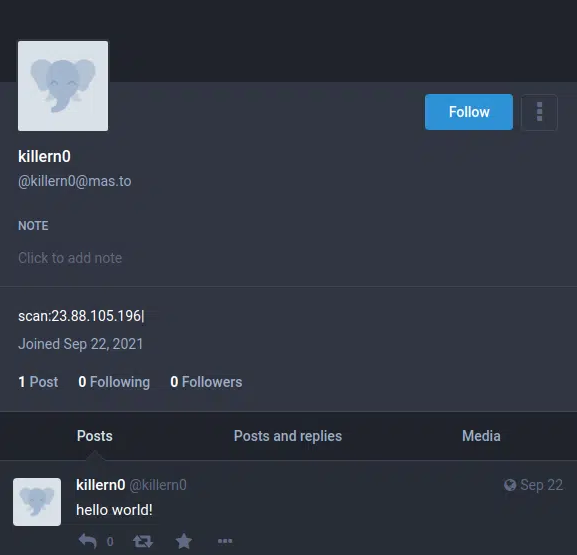
The IP address of command and control server in its classic meaning is not present within the Vidar sample. Instead, malware carries an address of a social network page, which contains the C2 IP in its name or description. Analysts and we personally witnessed such accounts in a number of networks, but most often they appear in the ones which offer the least complicated sign up procedure, and relative anonymity. The most widely used social media are Telegram and Mastodon.
First contact with C2 contains only a bot ID within a pretty regular GET request. Server, in turn, replies with a configuration package that contains guidances upon behaviour, and the DLL malware needs for running. It uses certain native Windows libraries, but most of the required ones arrive only after the C2 communication. It's also worth noting that malware supposes different behaviour patterns, and thus different DLL lineups that suit each case. The list of DLLs that are used the most is like the following:
- vcruntime140.dll
- msvcp140.dll
- freebl3.dll
- sqlite3.dll
- softokn3.dll
- mozglue.dll
- libcurl.dll
- nss3.dll
The body of a C&C response contains a specification that points at the features to be used (the behaviour determinative ones, what we mentioned above) and a list of specific directories and names to look for.
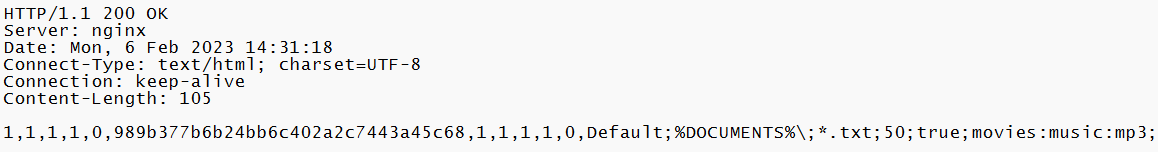
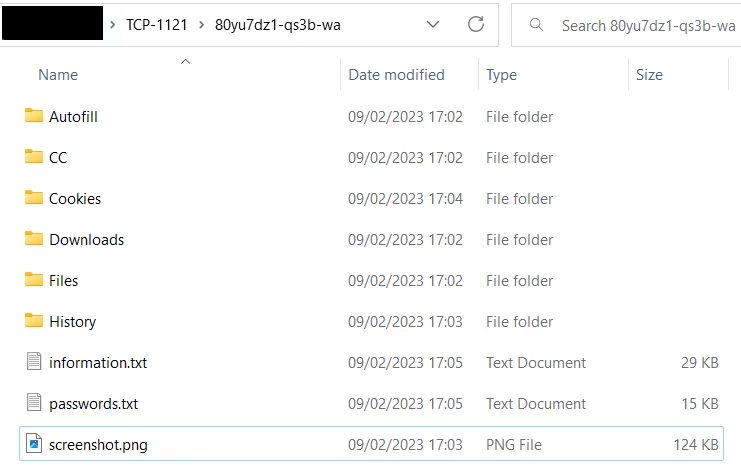
A sequence of 0 and 1 you can see in the last row corresponds to “modules” that are about to be plugged in. We managed to recover some of the relation of their position to actual malware functions. As you may guess, 1 means active feature and 0 – deactivated one. There are ten of them in total.
| Position | Module functionality |
|---|---|
| 2 | Grabbing AutoFill data, cookies and credit card information |
| 3 | Collecting history of web views and downloads |
| 4 | Stealing cryptocurrency wallet address |
| 7 | Hijacking messages history from Telegram |
| 8 | Taking a screenshot |
| 9 | Stealing specific files (most probably of a certain file format) |
Data stealing
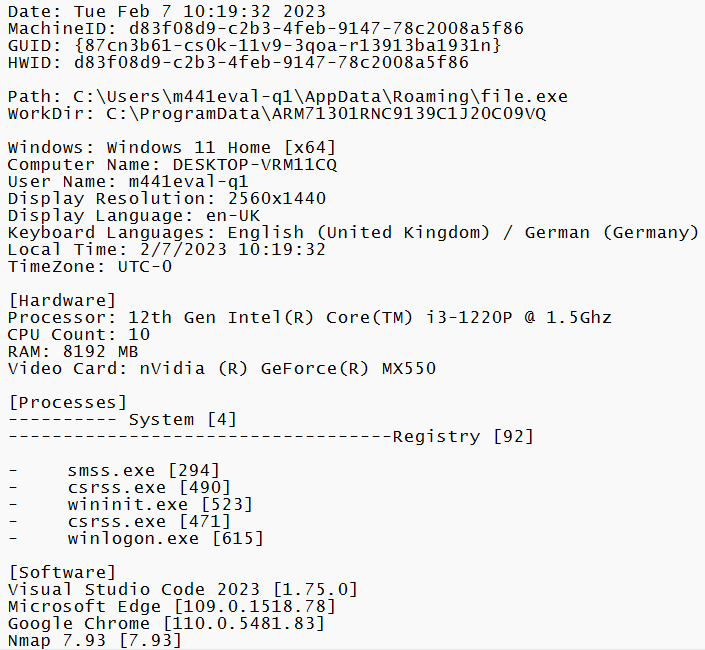
Main course of the Vidar is data stealing, and it happens right after receiving the configuration file from the command server. That being said, regardless of the actual settings, Vidar does not lose its basic stealing capabilities. It by default is capable of collecting a wide range of data that describes the system it is launched in.
When combined with various functional modules, the list of information malware master receives after a successful attack is tremendous. They generally aim at delving into C:\ProgramData directory. Overall, Vidar may collect the following categories of data from the target system:
- List of installed software
- Last downloaded files (in the Downloads folder)
- Cryptocurrency wallets
- Autofill files
- Browser cookies
- Browsing history
- Files of specific formats
It also checks the mentioned directory for files that contain following words in naming:
- Passwords
- Information
- Outlook
- Screenshot
- Cookie
- List
To the web browsers present in the system, malware applies a specific string of actions. The two main groups are Chrome and Chromium-based browsers and Firefox with Quantum-based analogs. In the root directory of Chrome, it extracts account information, exactly passwords and usernames. Considering that people often use their Google account to log into Chrome, this may bring attackers a lot of valuable findings. Direct extraction of login credentials is not possible in late Chrome versions (80.0+), but malware has its own way to circumvent this. It simply creates a query to a database file that keeps this information, and receives what it needs. The query looks as follows:
SELECT action_url, username_value, password_value FROM logins
Firefox and related browsers receive pretty much the same treat – an SQL request that extracts credentials from a database. However, some of the last Firefox versions keep credentials in a logins.json file, in the encrypted form. To deal with that problem, Vidar uses the nss3.dll library we mentioned once above. SQL request for Firefox browser is the following:
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
Browsers developed by Microsoft – Internet Explorer and Edge – are attacked with the use of Vault functionality. This is a third-party identity management system, developed by HashiCorp. Malware brings an embedded solution based on this program, that helps it to extract credentials from these browsers, which use a different way to store login information.
Cookies
Aside from grabbing account credentials, Vidar is also capable of messing with browser cookies. The way it extracts information from cookie files depends on the browser, same as in the case of personal data decryption. IE and Microsoft Edge store cookies in a regular .txt file, thus malware succeeds with stealing them by just scanning these browsers’ directories. Chrome, Firefox and browsers on their basis are a different story.
These two browsers use SQL databases to keep all the cookies in less accessible form. It is also worth noting that they are kept away from a root directory, particularly in the corresponding folder in the AppData/Roaming or /Local directory. An SQL query (unique for each browser type) will extract cookies in a similar fashion it did to login credentials.
| Chrome | SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies |
| Firefox | SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies |
FTP credentials
At the stage of initial system scanning, Vidar checks if there are any FTP clients present in the system. Earlier versions of Vidar were capable only of attacking WinSCP and FileZilla clients, along with Pidgin messenger, but things changed with time. Nowadays, this malware is able to steal credentials from both autofill form and currently active sessions.
Email clients
Among other things, Vidar stealer pays additional attention to 2 email clients – MS Outlook and Mozilla Thunderbird. It tries to steal login credentials from these services, which leads to obviously bad consequences. However, there is nothing new for the manner Thunderbird is hacked, as it shares the credentials handling mechanism with the browser.
Outlook, on the other hand, stores passwords in the \files\outlook.txt file placed in its root directory. This file is encrypted, and deciphering it requires some effort and playing with Windows CryptUnprotectData API call. Before applying this function, malware exports values of 7 registry keys in that directory:
HKCU\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
The use of this function decodes an actual password, thus Vidar is able to read its plain-text instance and save to its folder with stolen files.
Cryptowallets
Vidar carries the ability to steal information about cryptocurrency wallets kept in the system. It specifically goes for a line of most popular wallets, and extracts all the files it finds in a directory dedicated for this. The directory path varies from one wallet to another. Overall, the list of wallets it aims at is the following:
- Exodus
- ElectronCash
- Ethereum
- Electrum/ElectrumLTC
- MultiDoge
- Atomic
- JAXX
File storing manner
To keep the collected information in one place before sending it to the command server, Vidar stealer keeps it in a directory in the ProgramData folder. It is already hidden, thus malware does not worry about the user noticing it during routine browsing. In the directory with a totally random name it creates folders that correspond to the categories of extracted data, as well as unsorted data and screenshots that lay at the directory root.
Self-destruction
After finishing the data collection, Vidar stealer packs it into a ZIP archive, and sends it to a command server. Once done, malware initiates a self-destruct process with the following command:
C:\Windows\System32\cmd.exe” /c taskkill /im Devil.exe /f & timeout /t 6 & del /f /q “C:\Users\MalWorkstation\Desktop\Malware.exe” & del C:\ProgramData\*.dll & exit
Before executing it, malware deletes all the files it managed to collect and bring to its root directory. As it leaves no straightforward evidence, investigating what happened to the system may be pretty challenging.
Detection evasion
Contrary to other stealer malware, Vidar does not feature sophisticated anti-detection and anti-analysis features. It used to arrive as a regular .exe file, which is pretty common for stealers of that grade. Besides the random manner of packing, they end up on string encoding and encryption. That is generally enough to confuse legacy AV engines that try to detect malicious activity based on YARA rules. Meanwhile, next-gen antiviruses and especially corporate security solutions will easily deal with such a trick.
Dynamic anti-detection capabilities are pretty dim and consist of a simple check for specific usernames given by Microsoft Defender sandbox. The particular ones it pays attention to are HAL9TH and JohnDoe. Once there’s a match, Vidar performs a self-destruction procedure.
How to protect from Vidar?
Malware like Vidar generally aims at single users, rather than corporations. It is spectacular through both seeing its infection statistics and anti-detection measures applied in the system. Thus, the way to counteract this malware is not complicated.
Do not neglect using anti-malware software. Modern computer environment is full of cybersecurity threats of different kinds, and we spend hours on the Internet – the main source of malware. Being confident that you’re doing everything right is not enough to protect your system from malware invasion. It sometimes may come from places you’d never expect. To cover these blind spots, you should have a well-done anti-malware program. GridinSoft Anti-Malware will be an excellent choice, offering advanced detection system and constant updates – so no new malware samples will pass the barrier.
Avoid dubious email messages. Marvellously, but the most popular way to spread malware these days can be countered by a simple attentiveness. Spam generally tries to mimic routine messages, but it can barely repeat certain details even in the most sophisticated cases. Email address that contradicts the message topic is one of the best indicators. Yet another one is an overall strange message that you should not receive – either a duplicate, or a thing that tells you about events that did not happen.
Never download or run MS Office documents from untrustworthy sources. Office docs by default are not malicious, but may carry malicious content which can mess up your PC. Key points of this maliciousness are macros we mentioned above. Tiny blobs of VBA code are executed as a part of a running Office, and thus considered legitimate and ignored by legacy antiviruses. That problem may be solved by solutions that use zero-trust policy – but the safest space is where no crimes happen at all.
Stop using cracked software. Another popular source of Vidar, and various other malware (including ransomware) is pirated software. It is generally distributed by handymen who managed to skip the licence check; such guys often seek the way to monetise their efforts. Requests for donations are not pretty efficient, therefore an obvious solution is to go illegal, especially considering that hacking is already outlawed. Darknet, in turn, is full of offers that promise way bigger returns than any donations may guarantee.
Check the URLs of the links you open. Recent campaign with malicious ads in Google Search had a common feature – comically misspelt website address. Seeing nvibia-driverss.top or downloadd-anydesk.safe instead of legitimate download pages may instantly uncover that fraud to aware users. However, people are prone to click on the first thing they see in Google, trusting it blindly – and receive nasty stuff like stealers or ransomware. A simple check-up of the URL will be enough to prevent the attack.
Vidar Stealer IOC
| Spy.Win32.Vidar.tr | 1b47b08057aed1949adb36520638e1578569fcc360011fd6406809903b0a512c |
| Spy.Win64.Vidar.tr | 95d63301e807ee2f38661b7f2f5dcbbff5dbb5289bb8d82efb6a5e6124951200 |
| Spy.U.Vidar.tr | fdf597770b2418fb489f43f92b356cd5d30b0af04323582419538d062acf8567 |
| Spy.Win32.Vidar.tr | fcb41b6beaad2db4ac83aec31f4382cf885d3e00ce49bd5e38e3b4b03909545c |
| Spy.U.Vidar.tr | f95a609843bd8b29953986a663dcf62ee88351a8ce308f22db87ad480397cb36 |
| Spy.Win64.Vidar.tr | 3c67ddeb2426bfd91144dd8ca4ec06ee20578105514ad629c830e194bfd65893 |
| Spy.U.Vidar.tr | 0bbdda44330f983208041c1422e52759e87de6c4438b152d6dc36e17f07f9765 |
| Spy.U.Vidar.tr | 3bae8ea58db5926584007d715d1f47fc60cc8e219b564ef5dddc5c7dbc70f9be |
| Spy.U.Vidar.tr | 1ccfce02fe1c6407fdcbbd93f8d234ef7ec7d4fbdf8a09e594302a7757d6b463 |
| Spy.U.Vidar.tr | 141625c898ccd820bfde15265079fff595417ab13f95e139a376642e956c3727 |
Social Media Addresses
- hxxp://www.tiktok[.]com/@user6068972597711
- hxxps://t.me/mantarlars
- mas[.]to/@zara99
- ioc[.]exchange/@zebra54
- nerdculture[.]de/@yoxhyp
- hxxp://www.ultimate-guitar.com/u/smbfupkuhrgc1
- mas[.]to/@kyriazhs1975
- mastodon[.]online/@olegf9844g
- steamcommunity[.]com/profiles/76561199436777531
- ioc[.]exchange/@xiteb15011
- hxxps://t.me/larsenup
- c[.]im/@xinibin420
- nerdculture[.]de/@yixehi33
- mas[.]to/@ofadex
- t[.]me/asifrazatg
- steamcommunity[.]com/profiles/76561199441933804
- c[.]im/@xiteb15011
- nerdculture[.]de/@tiaga00
- steamcommunity[.]com/profiles/76561199439929669
IP addresses
| 162.241.225.237 | 5.79.66.145 | 104.21.45.70 |
| 193.29.187.162 | 104.18.5.149 | 45.151.144.128 |
| 18.205.93.2 | 141.8.194.149 | 95.217.16.127 |
| 157.90.148.112 | 116.203.6.107 | 37.140.192.11 |
MITRE ATT&CK
| Technique ID | Description | Technique ID | Description |
|---|---|---|---|
| T1204 | User Execution | T1156 | Phishing |
| T1555 | Credentials from Password Stores | T1552 | Unsecured Credentials |
| T1539 | Steal Web Session Cookie | T1113 | Screenshot Capture |
| T1614 | System Location Discovery | T1057 | Process Discovery |
| T1518 | Software Discovery | T1087 | Account Discovery |
| T1007 | System Service Discovery | T1041 | Exfiltration over C&C Channel |
| T1095 | Non-Application Layer Protocol |