What is Spam?
Spam has become a common word in modern life. And not only because of the tasty spiced ham brand - hackers who try to earn money illegally also contributed to this. Why is that so popular and profitable? Let’s figure it out together.
The exact meaning of this word refers to the period after WWII. Working for Uncle Sam, the American food industry was producing goods that could be kept for a long time without the risk of spoiling. One such good was spiced ham cans, branded as SPAM. Factories produced so much of it that they tried to sell it after the war - the best-before date was not infinite. Huge inventories of these cans pushed the massive advertising campaign - Americans were spectating the SPAM ads literally wherever. Therefore, this name just became a common noun for any obtrusive advertising - just as a virus for any malware.

Spam in the modern variant appeared long before the Internet era. People have always suffered from advertisements, but in the 60-80s, these ads were in their physical mailboxes. Tons of promotions of fraudulent auctions, Ponzi schemes, some lovely offers - they always were there. However, the development of the Internet gave a big punch not only to globalization but also to malicious spam.
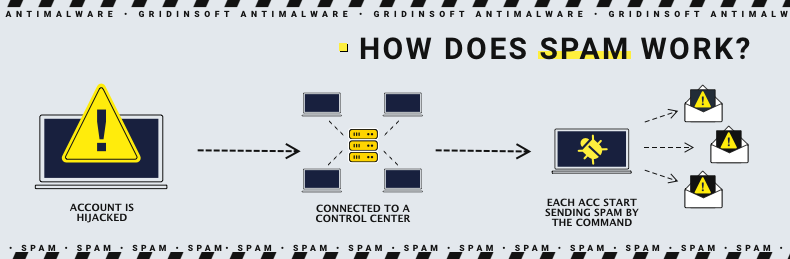
How does Spam work?
Spamming campaigns rarely stop on emails nowadays. Fraudsters try to reach the maximum audience possible so that you may see their messages on your Viber, WhatsApp, Facebook, et cetera. Last year, they also tried to do the same thing in Discord - but it required more ingenuity. For these cases, they usually do an individual campaign - one crook, or their affiliate, tries to win users' trust in the channel. Then, when people are at least sure he is not just a spam bot, this agent sends a spam link under the guise of something valuable.
Email spam is much easier. Hackers create numerous email accounts or hijack them and then send the messages to all users in their databases. The exact email is more complicated than just a link (as it was in Discord) but easier to introduce. Usually, all spam messages try to mimic some legitimate messages. Let’s have a look at the most widespread forms of email spam.
Read also: List of Scammer Phone Numbers 2025
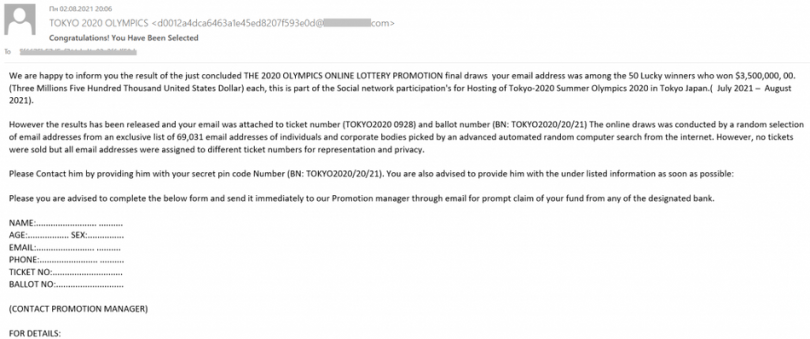
Event-relates Spam
Reached the peak of spreading after the beginning of the COVID-19 pandemic but initially appeared sometime before. Eurovision, World Football Cups, concerts of famous groups - all these stuff was a fuel for spamming campaigns. The contents look like a text stating the most recent results of the event and a link at the button. The exact link was leading you to a fraudulent website, or even to a phishing page.
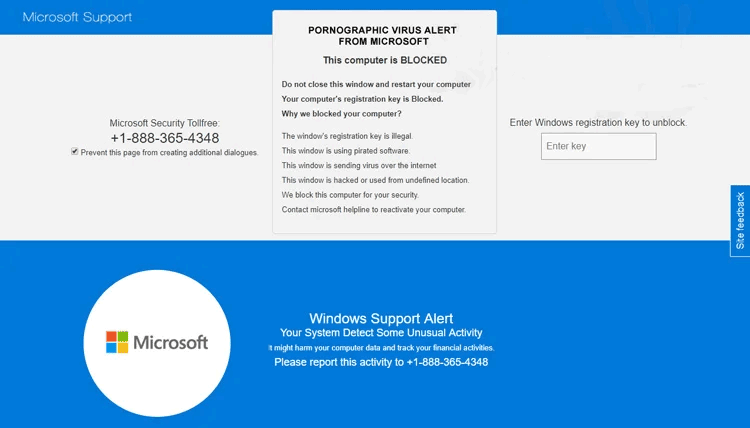
Tech Support Spam
More new things appeared during the pandemic. Microsoft Pornographic Virus alert is an odious example, that had a massive spreading in 2020-2026. It looks like a banner on the Web that claims that you have a problem on your PC, and to solve it, you must call tech support. The specified number - usually the one that belongs to the U.S. code zone - is, in fact, a redirection number. The endpoint of the call is somewhere in India - based on the speakers' accents and data from some calls.
In this “support”, you would receive a recommendation to download and install the third-party application to fix the issue. Occasionally, crooks ask you to grant them remote access to your computer. This or another way, you will receive some unwanted programs, or even full-fledged malware, on your PC.
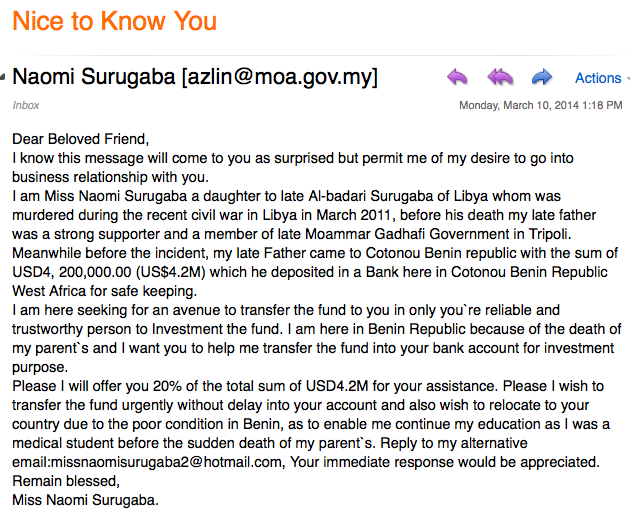
“Nigerian Prince's letters”
One of the firstlings of the email spamming, Nigerian letters still appear sometimes. In those messages, you see the request to help the Nigerian (or from any other African country) prince to transfer money of his royal family. You will receive a generous commission because there is no way to get this money saved from rebellions. All you have to do is send a small sum to the prince (to commit the further fund transfer). Is it worth thinking of $2000-$3000 when you would receive several million dollars instead? Naive guys think the same and don’t even think there is no money on the other side and no Nigerian prince. Hence, it is just a sophisticated money-laundering scheme.
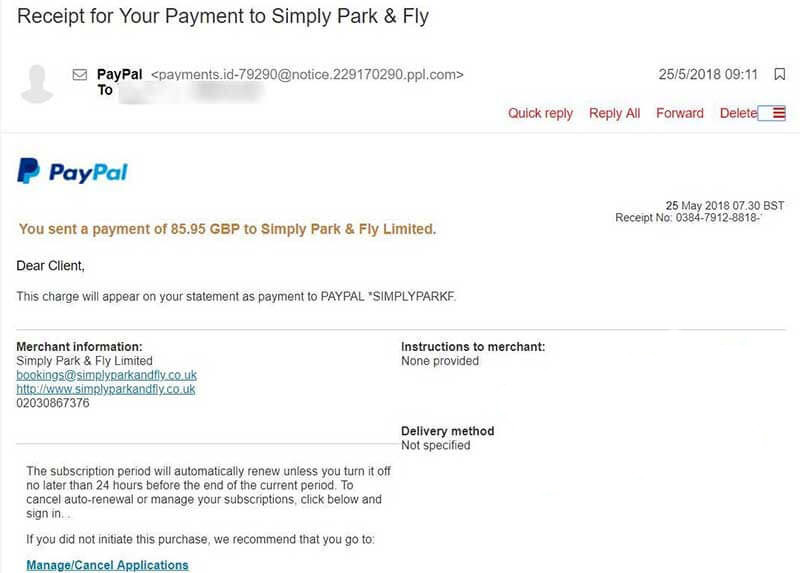
Email Spoofing
We have a deal with tens of different bills each day. PayPal payments, invoices from online retailers, subscription renewals - all these things drop on our emails twice per hour. Fraudsters know that and try to exploit your decreased attention. That's why such spam type is also called bait emails. You will likely pay less to no attention to another invoice from the delivery service and pay the bill. However, there is no problem with faking the message and embedding the link to the payment page the fraudsters want. You think you made the payment you must - but you have just been caught on this bait. In some cases, crooks attach a link to the fake payment system page. That leads you to lose your banking card credentials.
Phishing and Malicious Spam
This tactic is similar to email spoofing but with other attack vectors. Crooks who aim at phishing are not interested in your single-time payment. Their target is your credentials. Under the guise of notifications about changed service terms, or some internal messages on your account, they try to lure you into clicking on the link. On this link, you will likely see a poorly-made copy of the login page of a supposed sender. Usually, these fraudsters mimic banks, social networks, or online services with paid subscriptions.
Phone Call Spam
Spam calls were depicted in the Wolf of Wall St film. The whole offices of sales managers were spamming folks with obtrusive offers to purchase the penny stocks or even pink shares. Nowadays, people would not get on such a lure - especially after the overwhelming success of the motion picture. Modern spam calls may advertise the weight loss procedure, a new treatment for bedsores, and only God knows what else. They may even offer the same things as email spammers, but it is less effective. Still, to have any serious effect, must get the victim sitting at their PC or laptop and doing what crooks want.
SMS Spam (Smishing)
Spam SMS is more effective and relevant, although they were squeezed out by “free” email messages. SMS spam remains a convenient way of fraud because of the potentially better disguise. While email spam may be uncovered by checking the sender’s address, the latter in SMS (exactly, the phone number) may be changed with the one the crooks want. Most cellular carriers offer such an ability, which is handy for companies that often commit to mailing.
Read also: How to Stop Spam Texts?
What is Spam Risk?
Spamming is always done with the only final target - making money. The exact way of earning money may be different - getting the commission for each click, for each view - or even for each installation. Spam messages that contain malware may bring more money but usually require more research about the victim. The complexity of the latter usually forces the malware developers to perform the malspam by themselves.
So, what are the risks for the potential victim? Besides being exploited (morally unpleasant), you risk getting scammed or infected with various malware. A scam involving giving your bank card information to participating in the giveaway or sharing your personal information is unpleasant. Malspam, which supposes the infected file attached to the message, is also bad, but it is much harder to avoid. If such spam is pinpointed to you, with the contents you may expect from a legit sender, the chance of bad outcomes is very high. Drinking at the spam and never interacting with it will not create any problems. But sometimes, it is too hard to distinguish spam from regular emails or phone calls.
Technical Base For Spam Attaks
There is no way to perform massive spamming using a single account. Mailing services these days are pretty clever and will surely send spam all messages from the suspicious sender. And 1000+ messages from a single mailbox look suspicious. Hence, fraudsters decided to diversify the risks - and thus use botnets for that purpose. It is safer for ban prevention but also more effective - when people see an email address that looks legit, they will more likely eat the lure and do what you say.
If the hijacked accounts are on Facebook, Twitter, or any other extensive social network, crooks do a very sly trick. They started spamming the people who were in contact with the account owner. And the chance that such messaging will bring success to the crooks is very high. People trust their close friends and relatives and will follow a particular link without even a thought that something can be wrong.
The exact instruments to control the network of infected accounts may vary depending on the attack's wideness and depth. When crooks want to use only hijacked emails, they can use simple remote-access tools and numerous virtual machines. But when they need something more massive, they apply backdoors or other complicated malware. Backdoors are usually used in other cyberattacks - DDoS - but they are also good.
Read also: How to Get Rid of Spam Emails?
Victim Databases
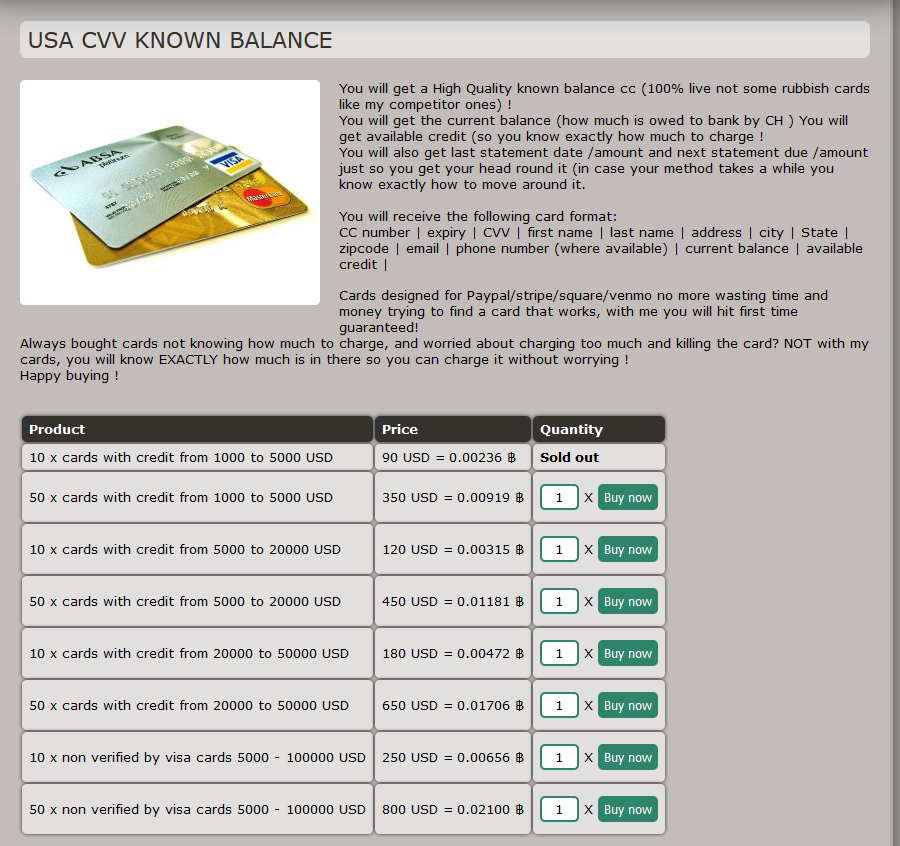
How do spammers know who to text? It is pretty ineffective to perform spamming campaigns “blindly”. Fortunately for them, there are plenty of databases of certain categories of users for sale on the Darknet. With a price of ~$100 for 10k contacts, it is quite cheap to start massive spamming. And when this spam is targeted - for example, bank account phishing is stylized for a certain bank and sent to the customers of this bank - the possible rewards grow significantly.
If your contact has once got into one of these databases, my condolences. The only chance to stop tons of spam (i.e., remove your email from the databases) is to stop using this mailbox. When the spam goes to your cell phone number, the only way to stop it is to change it. Unpleasant, but you likely have no choice when it has happened. All you can do to make the situation easier is to prevent it.
Related News:
- Calendar Virus on iPhone
- List of Scammer Phone Numbers 2025
- How to Stop Spam Texts?
- How to Get Rid of Spam Emails?
- Scam Likely Calls: How to block them?
- Skype & Microsoft Teams Spam Spreads DarkGate Loader
- Back to School Scams Expand As August Begins
- Emotet Has Resumed Activity after a Three-Month Break
How To Stop Spam?
You can see a lot of advice on it on the Web, but many of them are truisms or just useless. Advising to report the accounts used in spam has no reason - crooks will find new ones for tomorrow. But keeping the pessimism on is a bad habit. So let’s figure out what is needed to prevent such a nasty thing from appearing in your email.
First of all, think twice before typing your personal information anywhere. You visit strange sites for the first and probably the last time, torrent trackers, some online or offline squeezes - all these are the main data sources for the databases above. Keeping away from them, or using a different email/phone number for such events, is vital. Even if it looks legit and you are interested in keeping in touch with it, that does not guarantee that your contacts will not be sold then.
To avoid being used in spamming other people, keep your privacy well. Apply the 2FA on all accounts that are important to you. Keep an eye on what you click online, and scan your devices with anti-malware programs. That will help you prevent account hijacking - email and all your accounts on social networks. Password management utilities can offer you not only keeping the credentials in a single place but also suggest strong passwords.
How To Stop Spam Calls?
Spam calls may be stopped in several ways, but they all have disadvantages. The easiest one - blocking the unknown dialers - is available for almost every user. If you have a smartphone, even not the newest one, you may turn on this function in settings. This will automatically decline all calls from the numbers not listed in your contact book. But the disadvantage is right there - that stranger may be someone you are waiting for the call from. The other method is using the apps that manage your incoming calls, declining only the ones from the numbers added to a list. Those lists are filled by program developers and volunteer users, who report the spam numbers. That way, you may decrease the number of false alarms by orders of magnitude. However, it is still not ideal - not all apps work perfectly (in terms of efficiency of spam filtering), and some are classified as rogue software - one that has malicious or questionable functions.How To Stop Spam Messages?
Spam messages are harder to stop since only the carrier can completely prevent their arrival. However, just like in the case of spam calls, you can use apps that control incoming messages. They are often combined with ones that are made for call monitoring. Such programs will delete the messages from the senders from the blacklist before you can even read them. In that case, besides the disadvantages of the anti-call spam apps, you may also suffer from information manipulation. No one can say if the app will not delete the messages depending on their contents or sender. But that’s only the user's choice .When it is happened?
Sometimes spammers send their disgusting stuff to random people. Therefore, you must not panic when seeing single messages in your email. However, knowing how to react to this email is still important. As I have already said, that's no reason to report the sender’s mailbox. Your main reaction is just adding the message to spam. But it is also important to understand that you see the spam, not the legit message.
Spammers sometimes do a great job mimicking the actual companies. Counterfeiting invoices from payment systems, delivery notices, or bank emails is difficult; when done correctly, you will not distinguish them by the message body. However, the sender’s address is a thing they cannot hide. All official notifications are done through the official email addresses. Hence, seeing some weird stuff like [email protected] or [email protected] clearly says that someone is trying to scam you.
If you missed that or just struggled to remember what is the original email address and thus clicked the message - pay attention to the URL of the page you’ve opened. Phishing pages are getting banned quickly, so crooks usually use free hostings with ugly domain names. Moreover, the website design may look like a cheap parody by a schoolboy. Banks or payment systems have something well-designed HTTPS certificates. You can check the latter by clicking the lock icon on the left side of the URL bar.
Read also: Scam Likely Calls: How to block them?
Frequently Asked Questions
Another question in spamming is “who to spam?”. You may send your letters to random people, but it has almost 0 efficiencies. Purchasing the personal info databases costs pretty much. Hence the campaign will get its payback target. The most expensive datasets - ones that contain info ready to be used in spear-phishing - are even more costly. There’s no need to name the exact numbers - you may find them all on the Darknet.