
What is Phishing?
Phishing is one of the most widespread credential-stealing methods cybercriminals use worldwide. It is effortless to disguise. Its efficiency is extremely high, and - it is hard to blame the phishing organization for any cybercrime. The victim brings them the credentials himself, without any forcing from the crooks, so it can barely be classified as extortion or malware spreading.
The ways of phishing are numerous, and it is likely impossible to mention them all don’t miss one. However, several phishing methods are the most widespread nowadays. They always were the most widely used because of their simplicity and the high chance that the victim would be trapped. Meet the “heroes”!
Website counterfeiting
This method may be done in two ways - graceful and clumsy. The agile method is rarely used since it needs the infected network router, which the victim uses to connect to the Internet, or a specific malware on a victim’s device. An infected router is needed to intercept the packages the victim sends to the server (if the connection is unsecure) or to re-route the request on the counterfeited site.
Malware on the victim’s device is needed to change the networking settings to forcibly open the phishing page in an attempt to open a legit source. Malware targets the HOSTS file in Windows that contains DNS information for sites that must be connected through not standard DNS addresses. Fraudsters add a specific DNS for Twitter or Facebook to force the PC to show you the phishing site. Once changed, the DNS address will cause each of the browsers to send requests from the specified DNS, which is controlled by crooks.
Clumsy methods have some details in common with graceful ones but do not require interruption into the victim's computer. These phishing methods look like a simple redirect from a certain website on a page with “fasebook.com” or “tvvitter.com”. Such a link may be placed on the forum or be in a spam email message as well. It is straightforward to detect the counterfeit when you are not hurrying and have enough time to check the address bar, but you may surely miss this detail when shocking statements accompany the redirection link.
Modern shape of a well-known fraud
In 2020-2026, the cybersecurity world witnessed a massive email spamming campaign, which was a part of a phishing scheme. The victim received a scary message that mimicked, for example, the notification from the bank. In this message, the person was told that the conditions for serving his credit card (or debit, whatever) are changed, so they must approve these alterations. Otherwise, as the email promises, the account(s) will be blocked.
To approve the “changes”, you are instructed to follow the link at the message’s bottom. This link led to a poor copy of the bank site, exactly to the login page. After the attempt to log in, you will see only an error message. The fake page is tough to confuse with the original one, but when you are scared or visit a real online banking site, quite rare, it is easy to think that you are on the original one. After such a mistake, your money will be a big hazard - fraudsters have full access to your online banking.
Phone phishing
Have you ever got a call from your bank's safety service? If not, no one likely tried to fool you in that way. That method disappeared several times but then got back into view repeatedly. As you may already understand, you receive a phone call from a person who grants himself an employee of the security service of your bank. They claim that your account and your bank card are blocked due to unauthorized login attempts. To unblock the account, you must only say the security code you get on the phone number related to the mentioned bank account.
In fact, this security code is a code that approves the password reset. Fraudsters (and a person from “bank security service”) are just attempting to log into your online banking account, and the digits you report are a key to all money you have in your bank account.
Phishing forms to get your personal information
Sometimes, you may see the offers to fill out a simple form and get a reward of some sort - a pack of badges, a certificate for courses in origami, or an invitation to the exhibition. In that form, you need to answer some easy, sometimes absurd, questions and write your name, email, and phone number; sometimes, they also ask about your address. Under the guise of a legitimate “quiz”, crooks receive the full pack of your personal information.
After collecting information from a certain number of people, these tricksters are free to manage. They can sell it on different platforms (even in Darknet), also can use it to spam you - with email messages or even actual paper letters. Sometimes, they can come to your door with an offer to purchase some useless items for a tripled price. Of course, at that moment, they will try to assure you that these things are irreplaceable for your home and office, and you must buy them for your good.
Read also: "Someone Entered Correct Password For Your Account" Email Scam
Read also: Bank Details Email Scam
How to identify a phishing attack
The first and the most obvious sign of a possible phishing attack is a letter that requires some action from you, but you don't remember waiting for such a call. It can be an email or a direct message on social media. If it is anything but plain text, this should alert you. If there is any suggestion that you should download anything or follow a link - think twice before complying.
Phishing messages often have many errors. These can be typos, grammar mistakes, or spelling mistakes. Pay special attention to the mismatch of spelling of company or geographical names throughout the text of the letter. For some reason, phishing campaigns lack proofreading in general.
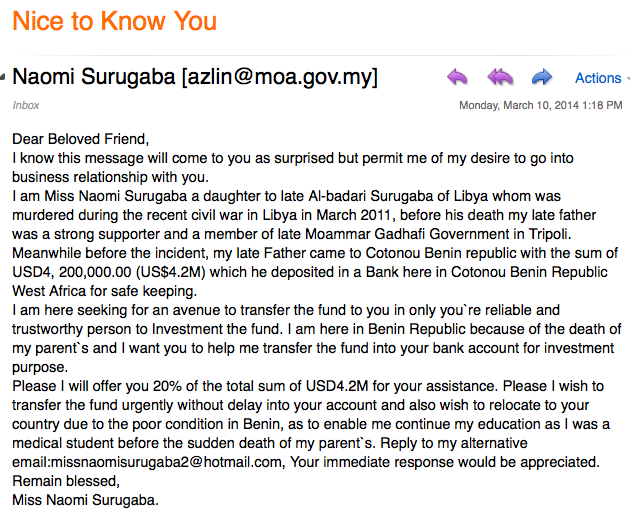
Regard the Internet as a digital image of the real world. If someone in the street approaches you and says you are a great-grandson of some blue-blooded duke of Austria-Hungary and, therefore, immense heritage awaits you, you will not believe that, will you? The difference between such a claim and a typical phishing bait is that the latter is much easier to dress as official and credible. Don't trust too-good-to-be-true notifications.
You can easily detect spoofed websites, links, and email addresses. Remember that fake websites often lack SSL certificates. You can easily see that without a closed padlock icon and HTTPS in the website's address bar. As for addresses, they can differ from trustworthy websites' addresses by one character so that they look alike, and you suspect nothing. The domain name of a fake website looking just like the one it pretends to be might not match the domain name of the original resource. There might be a subdomain you didn't know about, like support.website.com, but hardly a different domain, like website-support.com.
Phishers take inexperienced users off guard with approaches that, at some point, contradict common sense and rules of business. For example, no company will ask for a password via email. Likewise, no service would ask you to download files to deliver information about your order, pending payments, or postal delivery. They would display such data right in the body of the letter (there might be a file in addition with the same info, though.)
Considering phishing campaigns are often spear attacks, which means they target you in particular, may any letter or short message that looks somewhat strange alert you. If you are getting a letter from your friend where they ask you for financial help, for example, but call you with the rarely used nickname, better contact them via another channel for confirmation.
Read also: Urgent Reminder Tax Scam
How to protect yourself from phishing?

Most phishing cases are conducted mostly thanks to the victim’s inattentiveness. Hence, you may suppose an easy solution - being attentive at each questionable moment. Opening the link you found in the group chat on WhatsApp? Check precisely the address bar because it easily can be something like “tvvitter.com”. You can find a lot of things spoofed, and with the special tools that are available nowadays, this form of fraud is very easy to perform.
To avoid the phishing methods done with malware that modifies your system, check precisely the certificate of the website you are attempting to open. Fraudulent copies which are posted on the bogus DNS address are not able to get an HTTPS certificate. Click the lock icon at the left end of the address bar in your browser - it will show you the information about the certificate's presence. This is, exactly, one of the easiest cybersecurity tricks that still has high efficiency against phishing and spoofing.
Use two-factor authentication. That won't let anyone except the one who has your mobile phone (hopefully, yourself) log into your account. However, your phone might have yet another authentication procedure to unblock it, which would make the authentication to your account multi-factor, which is even better for tackling the consequences of a successful phishing attack.
Should you fall victim to a phishing attack, better have all your valuable data backed up on a hard drive or cloud storage. Phishing attacks may have various consequences, but data protection is the most maintainable countermeasure.
Do not spread your personal information. The quizzes above can look like something peaceful, and you may be interested in their prizes. However, think twice before sharing the information which will be used to make money - they are just exploiting you.
Use a spam filter. This feature of your mailbox will spare lots of your nerve cells. And you need it enabled if you clean up the rubble in your inbox daily. Yes, sometimes an expected letter ends up in the spam folder, but it happens extremely rarely compared to when dangerous and annoying messages miss your inbox.
Ultimate counteraction method for any form of phishing on the computer is anti-malware software. Of course, it is important to note that not each security tool will fit you - programs with an online protection function guarantee the best protection. That feature enables the website filter, which forbids the loading of malevolent counterfeits of popular pages. GridinSoft Anti-Malware may offer you such a function. Moreover, it is also able to get rid of the virus that helps the fraudsters to fool you.
Read also: Internet Fraudsters Arrested Email Scam
Frequently Asked Questions
- Urgent calls to action or threats;
- Unknown sender;
- Misspelling and poor grammar;
- Mismatched email domains,
- Strange links or attachments.
