Keystroke Logging
Keylogger Definition
Keylogger is a type of unwanted or malicious program that aims at one thing – logging all the keystrokes that happen in the system. Either from the keyboard, or from the mouse, such malware will detect any of them when designed properly. While looking less demanded and even obsolete, such functionality still poses a significant threat, even for the most secure systems and environments.
There may be several ways of how this malware functions, that differ depending on the device they are used on and even the form of keylogger. Most typically though, we are talking about a malware that has max privileges, and thus able to control even the deepest system processes. Regardless of the operating system, there will always be one responsible for handling keyboard interruptions, and that is where the keylogger virus tries to put its fingers in.
History of Keyloggers
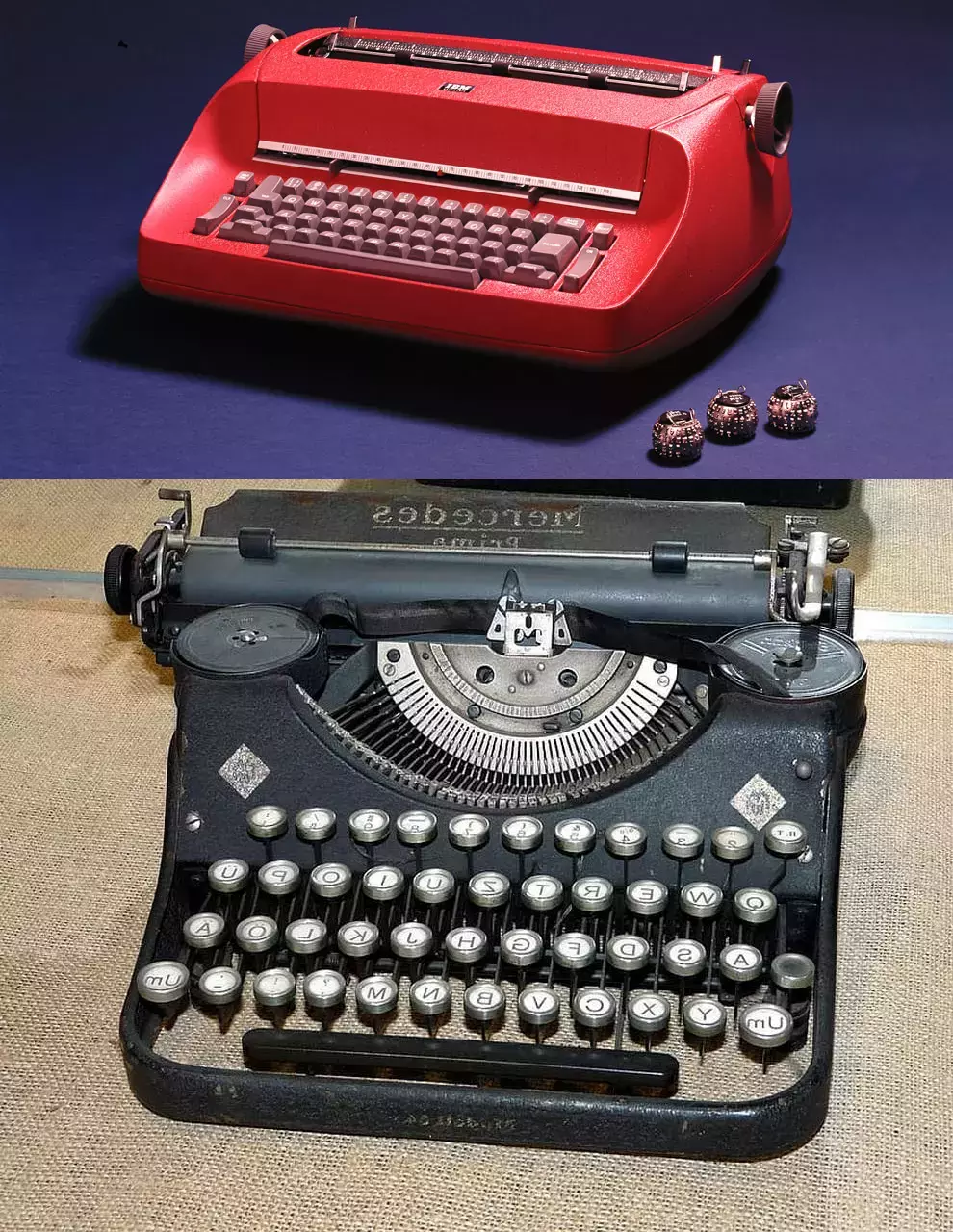
First keylogger or at least the mechanism that was working for the same purpose appeared in the Soviet Union. The US Embassy used an electric typewriter - IBM Selectric - to type all the documents, including the classified ones. In the mid-70s, Soviet spies managed to install the hardware chip that could register the keystrokes and transfer them to the KGB. This technology was not new - but was still useless against soviet embassies, which used only mechanical typewriters.
Forms of Keylogger Malware
Forms that keylogger malware can obtain are different. At the very beginning of the commercial malware era, keyloggers were often met as stand-alone programs. You could probably get one from a friend, too, when one tried to boast of his hacking madskillz. Nowadays though the vast majority of keystroke logging is done by more complex malware, typically backdoors, spyware or infostealers. That happened simply because it is way easier to inject a single, fully functional malware, rather than a pack of smaller ones. And after all, keystroke logging is not too much of a function to give it a separate program.
There is also a whole separate category of hardware keylogggers – devices that are built into either the PCB of the keyboard, a connector cable, or another element of the connection. Obviously, this device is almost always installed manually, as barely any manufacturer will even agree on adding the spying tool into a default packaging. It should be added manually, either while assembling the device or later on, during the usage.
In rare cases, keyloggers may be legitimate and mostly safe. A great part of them is used by large corporations in order to ensure workers’ presence at the workplace. The practice expectedly peaked during 2020-2022 pandemic restrictions, when companies were forced to switch employees to work from home, with no ability for any visual control. These legit keyloggers typically aim at only logging the fact of a keystroke, a mouse click, or its movement, without records on which exact key was pressed.
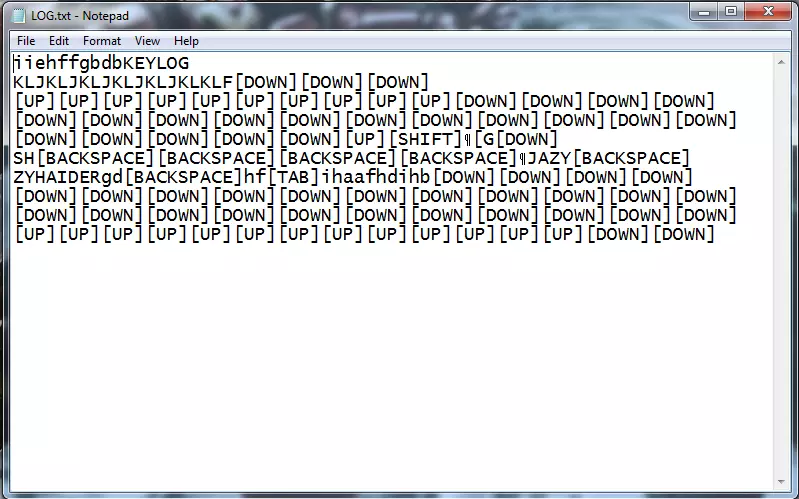
Aside from those “remote job” keyloggers, there is also a whole lineup of educational keyloggers, used in universities to show how things work. This may be an excellent example of how to intercept low-level system calls and interruptions, the action required for a lot of industrial software. Such samples, however, often lack any networking capabilities, and output the collected data to a specified text file.
Are Keyloggers A Virus?
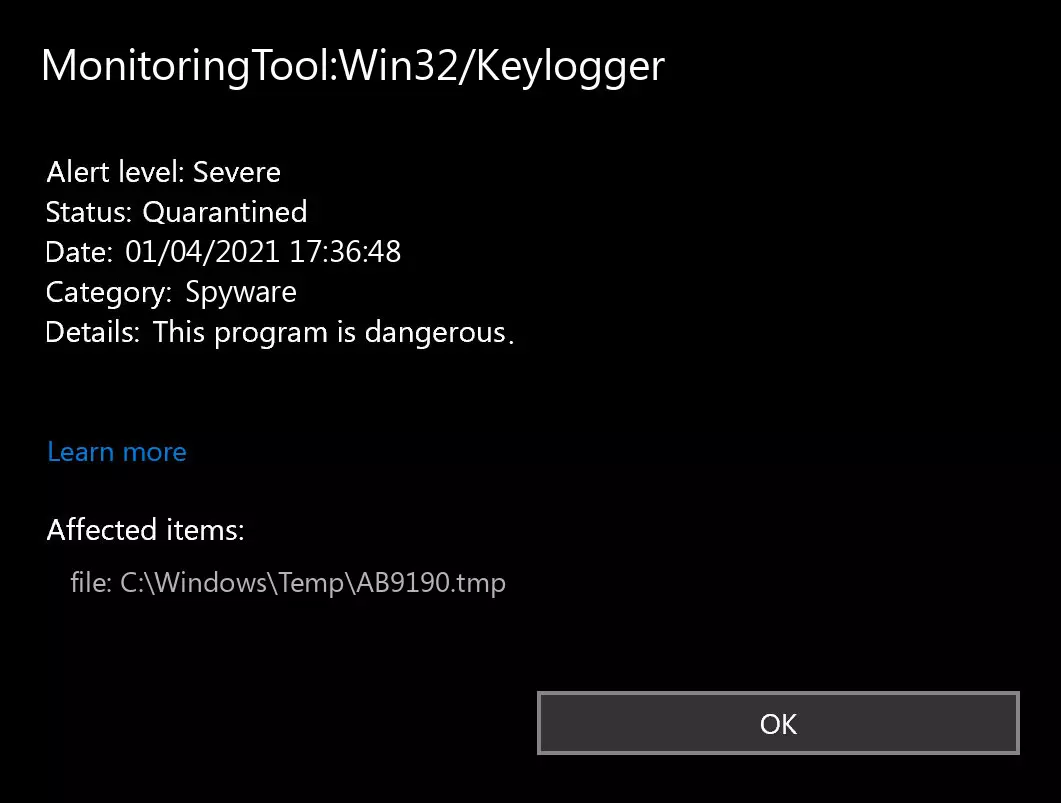
Depends on how you get it. If you have downloaded it manually, understanding what you are downloading and installing is legit. There are a lot of keystroke logging tools available on the Internet, so you will easily find one if needed. Again, cybersecurity and software engineering studies even offer the samples of ones for educational purposes, and a lot of students' jobs are available on the Internet. But it is a whole different story when you discover having a keylogger without any intent to have it. Regardless of how you found it, it has likely done its nasty job and transferred your data to a third party.
Overall, discussions about keylogger being malware or normal programs is are still ongoing. This type of programs run on the edge of legality, whatever use case or source you apply to them. But as we said above, it is always a terrible finding when you never expected one.
How dangerous are keyloggers?
There is a common thought on keyloggers or keylogging functionality being mostly useless and non-threatening these days, except for certain quite specific attack cases. And there is a rather good explanation behind it: before targeted infostealers appeared, keyloggers were the malware of choice for stealing credentials. Nowadays, when the infostealer market is one of the biggest ones of the malware world, this functionality is hardly needed.
But nonetheless, there are several cases when keyloggers, or keylogging capable malware can do much more harm than a “regular” one. Those are situations where user passwords are not present in the places malware typically grabs them from. In such cases, keylogging capabilities, enabled at the very moment of the user typing the password on a website, can supply hackers with the passwords no matter how advanced are the security systems. This ability to outflank even the most advanced protection measures are the reason for this malware staying afloat.
Read also: Trojan:Win32/Leonem - Information Stealer Analysis & Removal Guide
Keylogger Spreading
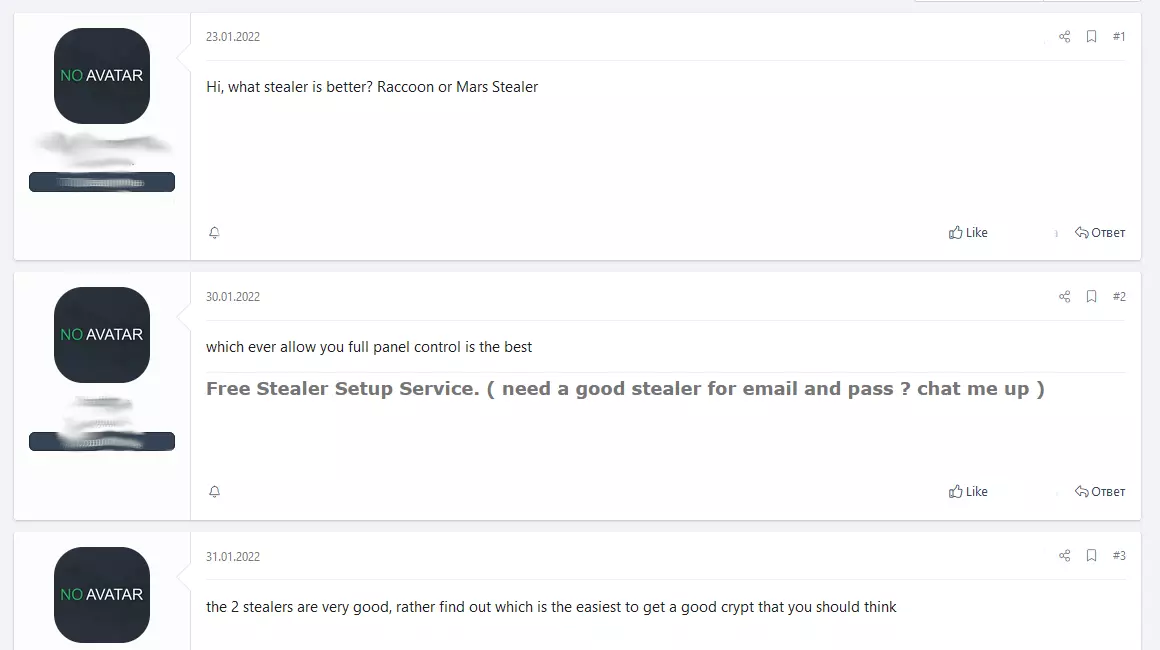
As mentioned at the beginning, keyloggers nowadays are usually spread officially or as a part of the malware, primarily - spyware. “Official” distribution does not mean the main website or affiliated sites - rather several themes on well-known online forums, sites with dubious tools (like KMS Activator) or P2P networks. Some high-end keyloggers - more stealthy and with more functionality for exactly spying - are sold on the Darknet.
For spreading to user systems, this malware gets injected through email spamming or as a part of “useful tools” you can get online Email spam is likely an alpha and omega of malware spreading since early 2000. People trust emails for some reason, so they open the attachments without any doubt. There are also newer approaches - with copies downloading pages for free software promoted on Google, or fake CAPTCHA sites that ask the visitors to run malicious code.
Keyloggers Activity:
⇢ Trojan:Win32/Leonem - Information Stealer Analysis & Removal Guide
⇢ MaksStealer (MaxCoffe): The Minecraft Mod That's Actually Stealing Your Passwords
⇢ Top 5 Infostealer Malware of 2025: The Silent Data Snatchers
⇢ SpyLoan Virus Found in Loan Apps on Google Play Store
⇢ Fake Copyright Emails Spread Lumma, Rhadamantys Stealers
⇢ Operation Magnus Disrupts Infrasturcture of RedLine, META Stealers
How To Detect And Remove Keylogger?
Regardless if you try to detect it on a mobile device or the computer, several strict signs define the keylogger presence. These signs are also the sign of low-quality keyloggers: ones used in spyware usually do not give the user such a chance. Nonetheless, you will likely see several of the following symptoms:
- Interfaces where the key pressing is required will react with a significant lag;
- All web pages, especially ones that contain a lot of graphic elements, will load extremely slow;
- The typed information in all possible places is displayed with a lag;
- General system slowdown (especially on weak systems);
- Lag of response when trying to open the folder/start the program;
- Laptops/mobile phones are discharged much faster than usual;
For sure, that list is not full. Some symptoms may be common with other viruses or issues with your hardware or software. That’s why I’d recommend you scan your device with anti-malware software. It will help you deal with the malware on your PC and protect it from further attacks. For instance, keyloggers are very easy to detect and remove with GridinSoft Anti-Malware - thanks to its Proactive Protection function. The heuristic engine which backs this security module allows it to detect even the newest keyloggers - just by their behavior.
Read also: SpyLoan Virus Found in Loan Apps on Google Play Store