What is a Rootkit?
Rootkit functions
Rootkit, as you can understand from its name, is a program that grants you low-level control of the infected system. And “low-level” means not surface access but possible access from the deepest levels. While most computer viruses are launched just like the applications, some malware types require access on the driver level or even deeper.
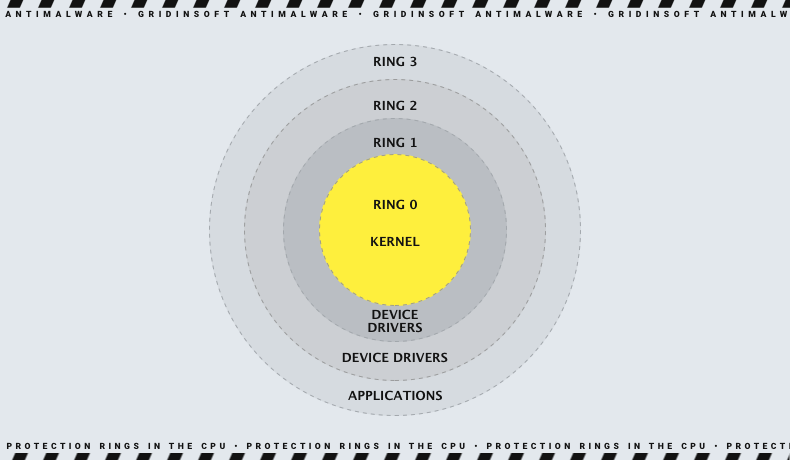
It is important to mention how your PC executes the applications you launch. There are four hierarchical levels, called protection rings, that define the rights that programs have when executed by your CPU. Ones placed on the higher ring cannot inflate the apps on the lower rings. Ring 0 is given to the operating system's kernel, Ring 1 - to the hardware drivers, and Ring 2 - to the programs with low-level access permissions. Ring 3 is used by most third-party applications since they don’t need any deep permissions. Implementing malware to the Ring 2 means you have control over all user applications; on Ring 1 - almost all things happen on the computer.
A rootkit is a program or a pack of tools that allow the person who controls it remotely to access the infected system and control it as it wants. It will still be dangerous in solitary but can barely be used to earn money for the victims, as all other viruses do. You can vandalize the infected system, make it malfunction, or even not work, but that will not bring you a penny. Until you manage to inject the other profitable malware.
Rootkit in combination with other viruses
Rootkit malware is extremely useful when you need to give the other viruses the ability to integrate as deep as possible. Such permissions offer cybercriminals access to all disks and the whole network. Sure, such a rough tool is rarely used for attacks on individuals. Attacking single users with rootkit+other malware is like hunting rabbits in a tank. However, against corporations or other things that use computer networks and data centers, it is just what is needed.
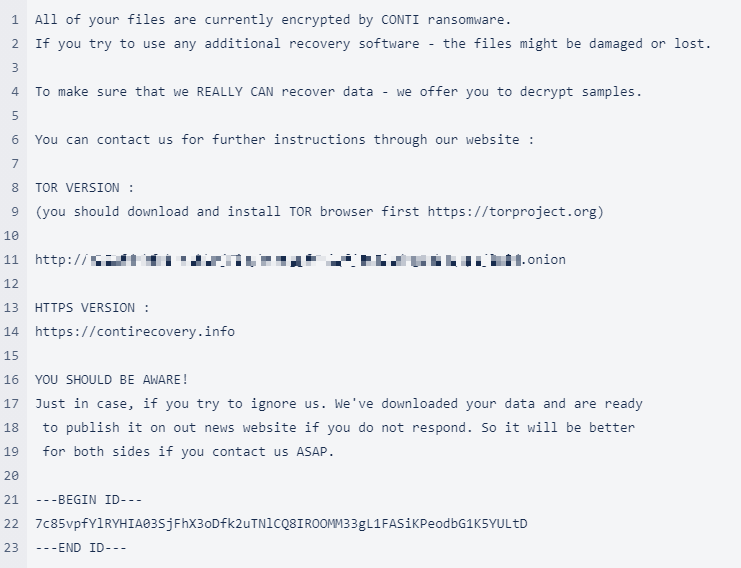
Attacks on corporations are usually backed by spyware, ransomware, or both simultaneously. Rootkit acts as an aperitive for the main course of encrypted files and stolen data. Both may cost corporations millions of dollars, and in case of a confidential information leak, you may also expect reputational losses. And all this spree is provided by one little thing that sits deeply in your system and holds the gates open. But how does rootkit work?
How does that work?
All operating systems, among contemporary ones, are not 100% invulnerable to malware attacks. Even the latest Windows and macOS have certain security flaws - they’re just not uncovered yet. Nonetheless, many companies do not keep an eye on the regular system and software updates. Some ask their employees to update their PCs manually, but they would rather make more memes about Windows updates than update them. Exactly, those breaches are used by rootkits to escalate privileges.
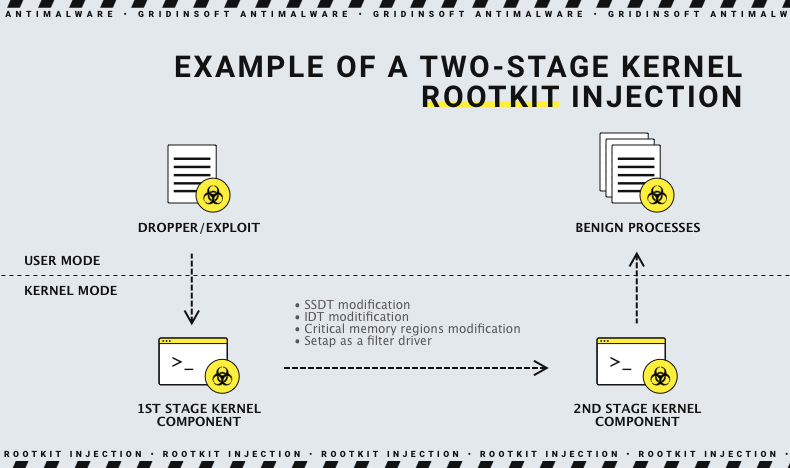
But breaches in operating systems are not so massive and easy to exploit. Most of the vulnerabilities the hackers use are located in third-party applications. MS Azure, Office, and Outlook, almost all Adobe products and apps from different other vendors are full of security flaws that allow the cybercriminals to perform their attacks. Rootkits they use are often created specifically for exploiting the vulnerabilities in certain apps used by the target company. These programs lists, their versions, and all other information that can be useful during the attack are collected during the OSINT operations.
Security breaches are usually the result of a poor or shortsighted software design. These flaws usually allow the user to execute the code with higher privileges or launch certain functions without showing any visible signs. Cyberburglars use such an ability to execute malicious code with maximum efficiency. When you launch the MS Office macro or open the malicious link in the Adobe document, crooks get this ability and launch the viruses. You can find the list of all detected vulnerabilities on the CVE Mitre website.
Rootkit attack step-by-step
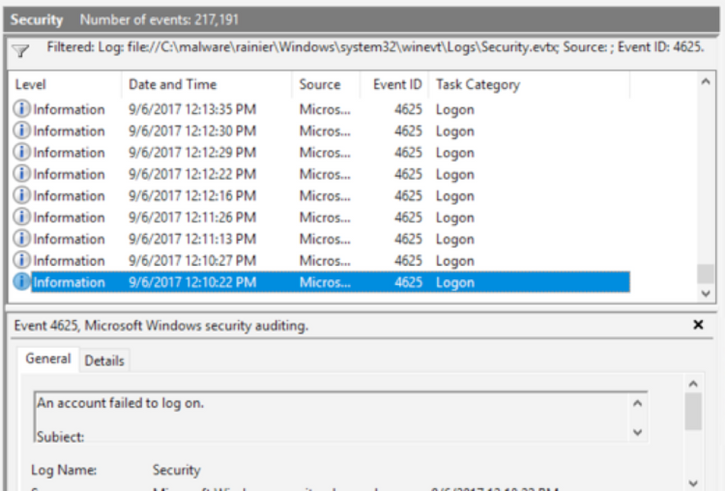
When the rootkit is delivered to a computer in the corporate network, it attempts to use one of the flaws to allow itself the execution on the deepest available level. Such rights then allow crooks to infect all other computers in the network and - more importantly - to brute force the domain controller. Access to the DC means controlling computers in the network and the server. In the companies where the network is not clustered that may mean paralyzing the whole office. For small companies, that usually means days of idle, offices of large companies may stop for weeks.
Cybercriminals do not create any new things. RDP attacks and bait emails are the alpha and omega of all modern malware spreading campaigns, but even in further actions, there is nothing new. After the successful launch of the rootkit, crooks then start brute-forcing the domain controller and other computers. Simultaneously, additional malware is downloaded and launched with escalated privileges. Computers in the network become infected, and when the DC falls, crooks launch the spyware and start downloading the data from servers.
The stolen data is the source of additional money for crooks. Personal information of the clients, data about the company's financial stats or production plans - all these things are highly-priced on the Darknet. Unknown doers are even more generous in their bids if there is information about the customers of a particular clinic, insurance company, or cybersecurity firm. However, some companies pay the additional ransom the crooks ask to avoid publishing this info. Sometimes, this "second" ransom reaches the sum of the initial one - for file decryption.
How are rootkits distributed?
As it was mentioned, they are spread through the classic ways of initial payload for the cyberattack. RDP technology is great but was used too rarely to catch and fix all flaws before the pandemic. But even though all attempts of Microsoft to block these breaches, companies do not hurry to update their software. And hackers only say “thank you” for such a gift. Even more thanks they will give you for the employees who open all attachments to the email messages and allow the macros in Office docs.
When it comes to attacking the individuals (i.e., joking or vandalizing), rootkits are distributed as fix tools for a specific problem, system optimizers, or driver updaters, i.e., pseudo-effective software. Sometimes sly users add them to the repacked Windows version and spread them on torrent trackers or elsewhere. Then, they are free to do whatever they want to users who install it on their PCs.
Read also: SYMBIOTE Backdoor and Rootkit Dropper Revealed
How to stop the rootkit?
It is pretty easy to counteract the thing when you know how that acts, and it is not something unstoppable and out-of-ordinary. Rootkits exploit old and well-known things, as was shown earlier, so it is quite easy to make your system, or even the whole network, invulnerable to malware injection. I will give you multiple pieces of advice, from preventive to defensive.
Do not let it in
Your workers must be aware of email spamming and other forms of baiting/social engineering. Someone may listen to the information but pay zero attention to it and keep doing dangerous things. But the question there is “why is he/she still not fired?”, not “how to make he/she follow the security rules?”. It is the same as smoking in the room with oxygen containers or rolling mercury balls on the office floor.
Set up a simple user account for employees
Since Windows Vista, this operating system can ask for the administrator’s password to run the program that asks for the admin’s privileges. People keep using admin’s accounts by inertia, but there is no need. Even though rootkit can still find a way to escalate privileges, it will need not just to escalate the rights of the application it exploits but also the rights of the user’s account. More steps → , more time → , more chances to be stopped.
Use anti-malware software
The ideal case for companies is to have a corporate solution for network protection. It will prevent the malware from spreading through the network and stop its attempts to exploit security breaches. When you cannot afford it or don’t want to have such a massive thing running in the network, you can create proper malware protection using anti-malware software. GridinSoft Anti-Malware will fit perfectly for that purpose - without any excessive functions and with proactive protection.
Update the software regularly
Rootkits will be useless when the system does not have any of the known vulnerabilities. Sure, there is still a possibility that crooks will use a 0-day exposure. But it is better to have only this risk than to have all flaws available for exploitation + zero-day breaches. Fortunately, nowadays, software vendors offer security patches almost every week. Just keep an eye on it and launch the installation of the update regularly.
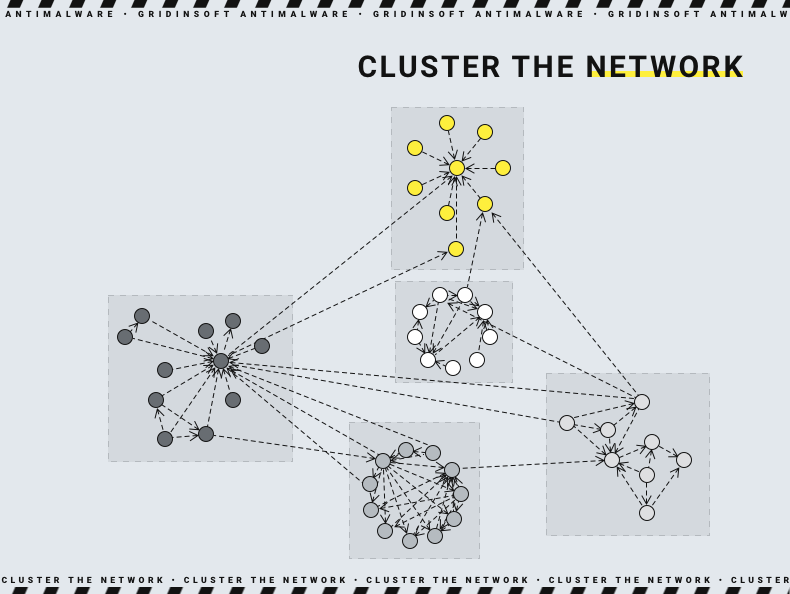
Cluster the network
Having your whole network connected to a single Domain Controller is a perfect situation for hackers. Sure, such a network is much easier to administer, but the whole network gets damaged when it comes to cyberattacks. If malware - usually ransomware or spyware - finishes its activity, you cannot use any of the computers in the network. All files are ciphered, credentials are stolen, and ransom notes are everywhere. Your office will be out of the working process, resulting in significant losses. Meanwhile, when you cluster the network, only a part of it gets out of service in case of an attack.
Isolate the servers
Sure, it is much more comfortable to manage the servers sitting at your workplace than to have a glorious walk through the server room, from one stand to another. But the latter is much safer in the case of cyberattacks. It is important to keep the balance - some prophylactics and new releases deployment may be done remotely. But most of the time, the server access must be restricted or enabled only after entering the password.
How are rootkits detected and removed?
Detection and removal of the rootkits is a thing that requires the use of anti-malware programs. It is impossible to see any signs of its presence before it is too late, and it has many facilities to make itself more sustainable in the attacked system. Their detection, however, also requires a fast reaction. Such a reaction time can be provided with a proactive protection function, allowing the program to check the running processes in the background. That’s why I will recommend you GridinSoft Anti-Malware once again. It has a function - based on the heuristic engine and neural network. This security tool can effectively counteract the rootkits in the earliest stages of malware infiltration.
Read also: How to Prevent a Rootkit Attack?