What is Computer Virus?
Computer Viruses: The History
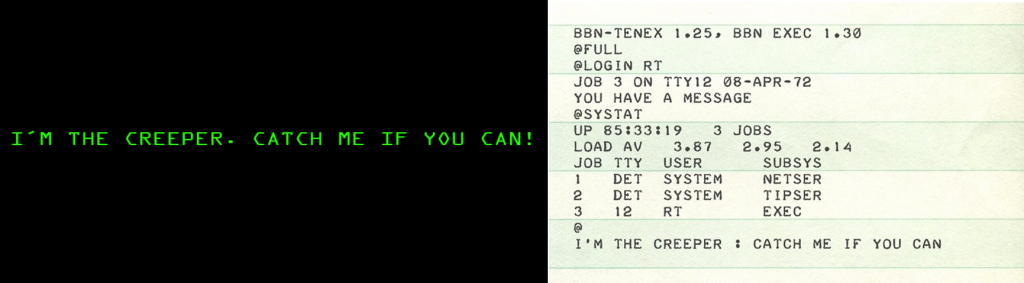
Computer viruses have been around since the early days of computing. The first computer virus was created in 1971 by a programmer named Bob Thomas. It was called "Creeper" and was designed to infect the ARPANET, a precursor to the modern internet. Creeper was a simple virus that displayed a message on infected machines, but it was the first of many viruses to come.
In the 1980s, computer viruses started to become more common. The first "real" virus, called the Elk Cloner, was created in 1982 by a high school student named Rich Skrenta. The virus was designed to infect Apple II computers and spread through floppy disks. It was harmless, but it was the first virus to spread outside of a single computer system.
Throughout the 1990s and early 2000s, computer viruses continued to evolve. The rise of the internet and email made it easier for viruses to spread quickly and infect large numbers of machines. The first email virus, called the "Good Times" virus, appeared in 1994 and was designed to spread through email messages. Since then, email viruses have become a major problem, with new strains appearing every year.
Today, computer viruses continue to be a threat to computer users around the world. Hackers use viruses to steal sensitive information, such as credit card numbers and login credentials. They also use viruses to take control of infected machines and use them to carry out attacks on other computers.
Read also: Heuristic Virus Detection: How AI-Powered Security Catches Unknown Threats
Protecting your computer from viruses is more important than ever. Anti-virus software can help to detect and remove viruses before they can do any damage. It's also important to keep your operating system and software up-to-date with the latest security patches to prevent known vulnerabilities from being exploited.
In conclusion, computer viruses have come a long way since the first virus was created in 1971. They have become more sophisticated and more dangerous over time, but with the right precautions, you can protect yourself from their harmful effects.
5 Types of computer viruses
If you're concerned about computer viruses, it's important to understand the different types that can infect your system. In this section, we'll explore the various categories of computer viruses and how they can harm your computer.
- 1. Boot Sector Virus: This type of virus infects the boot sector of your computer's hard drive. When you start your computer, the virus is loaded into memory, allowing it to execute its malicious code.
- 2. File Injector Virus: This virus infects executable files, such as .exe and .com files. Once infected, the virus can spread to other files on your system.
- 3. Macro Virus: This type of virus infects macros in programs such as Microsoft Office. When you open an infected document, the virus can execute its malicious code.
- 4. Worms: Unlike viruses, worms can spread without user intervention. They exploit vulnerabilities in your computer's security to spread to other computers on the network.
- 5. Trojan Viruses: This type of malware disguises itself as a legitimate program. Once installed, it can allow attackers to gain access to your computer or steal sensitive information.
Virus vs. malware - what is the difference?
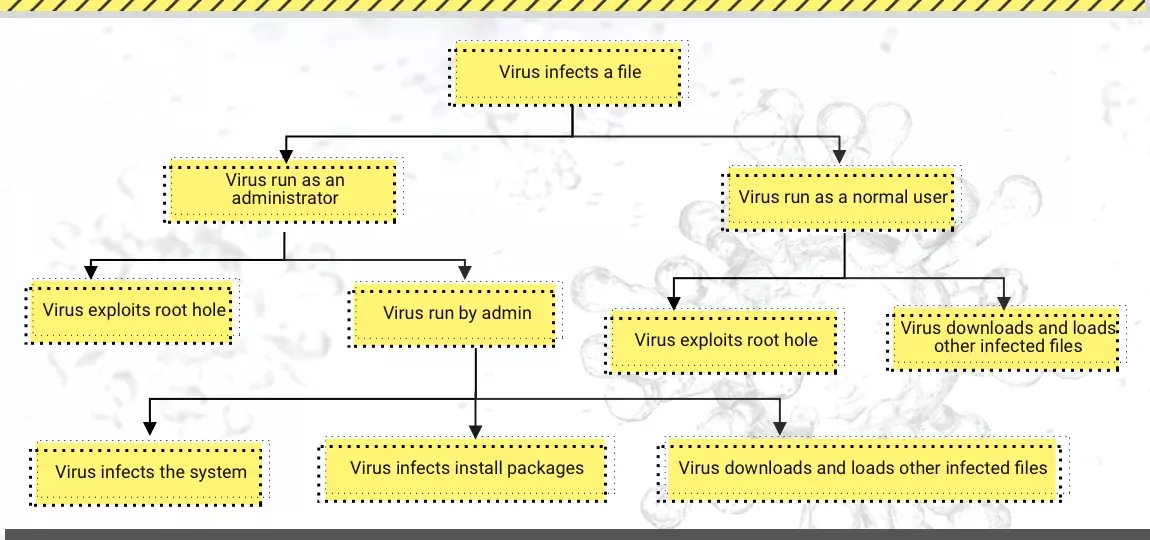
Computer virus, as was mentioned in the paragraph above, is malware that replicates its code into other programs and files. Then, this replicated part replicates itself into other files, so the destruction goes exponentially. At one moment, the program stops working and may even fail to start. Finally, it may turn out that your computer fails to do even a thing without calling the error window. In the saddest cases, when the virus damages critical system files, you will see the BSOD when trying to boot Windows.
What is more interesting - viruses were completely unprofitable during this boom. In the ‘00s, there were a pretty low number of malicious programs that could be monetized in any way, but it is very unusual to hear now, in 2022. In those days, the malware was distributed to amuse someone rather than gain money. And in fact, the end of the computer virus domination era was the start of the malware-for-profit epoch, which lasts till these days.
Why did computer viruses disappear?
It is pretty ironic that computer viruses were the stimulus for anti-malware programs to be created, and exactly anti-malware was the force which made the viruses cease to exist. Malware analysts had endured combat with viruses for a decade but finally found a way to stop them all - even the newest ones. They implemented the rule "if it reads a text as a code - it is a virus" - and that was enough to make all attempts of malware creators useless. And they possibly could be more motivated if their job was profitable, but that was much more reasonable to switch on other malware types or even go to a white job.
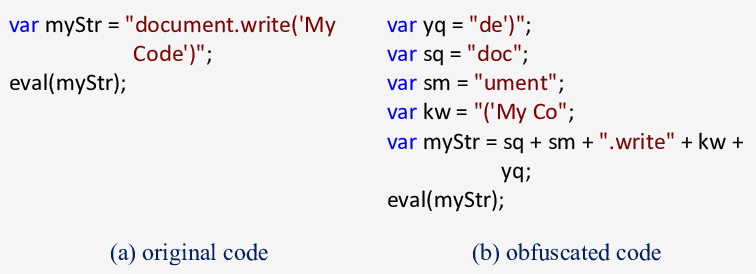
Sure, viruses did not disappear completely. It is possible to bypass the rule mentioned above by some tricks with obfuscation and repacking. However, there is still no way to monetize a stand-alone virus. It makes the programs and system malfunction - and what’s next? Trying to make money on that thing is hard, but crooks still use it sometimes. Viruses are pretty useful when you need to exploit the vulnerability or to make certain apps malfunction. That’s why cybercriminals sometimes apply using specially created viruses to commit cyberattacks on corporations.
Read also: Virus:Win32/Expiro: The Chameleon Backdoor That's Still Causing Havoc in 2025
Computer virus distribution
In old times, viruses were everywhere when computer viruses were on the malicious Olymp. You could click on the banner online and get one, install a pirated game - and the virus will be included. Even visiting certain websites was not safe - viruses could stealthily get on your PC and launch. Most of these spreading ways are impossible in modern times because the software has much more protection. Yes, malware developers may say for sure that earlier was better.
Nowadays, as was already mentioned, viruses are mostly used in cyberattacks. Hence, their usual spreading ways are the same as spreading ways of the initial payload for attacks on companies. Spamming of different sorts, RDP exploitation, social engineering or even all together simultaneously - all these things are typical for computer viruses spreading. After the successful penetration of the network, the virus is launched together with keyloggers or other things.
More interesting thing is how these viruses are designed. Since anti-malware programs have such a powerful countermeasure, it is impossible to use classic computer viruses. That’s why crooks usually order it somewhere and receive a real Frankenstein child. Most of such malware is ordered somewhere in Asia and then used to commit attacks on the whole globe. These viruses are packed in a very unusual way and have an extremely obfuscated code. Such tricks allow fraudsters to avoid malware detection. Nonetheless, it is better to use a backdoor - it is much harder to detect and easier to make stealthy.
Read also: Shortcut Virus
How to prevent computer viruses?
Getting a computer virus these days is like finding a gold nugget in a pig trough. There is a small chance of getting one when browsing some ancient pages on your old computer. But if you are afraid of getting one - forget about opening suspicious pages and starting the programs from untrustworthy sources. It is not about preventing viruses - it can help you prevent malware. So let’s check them out - to stay aware.
Illegal software is one of the most massive malware sources for individual users. Hacked games from torrent trackers or downloaded directly from websites with “free” games, hack tools, and keygens for various software are the best carriers for malicious software. In particular, stuff like KMSPico is considered one of the most common sources of ransomware and spyware at the beginning of 2026. Forget about using it - and you will significantly decrease the chances of getting a virus.
A new trend in virus distribution is email spamming. Fraudsters send emails that bait users into clicking on the link or opening the attachment. Whatever it is, you will receive malware on your PC after the malicious script execution. Avoiding such emails is difficult: crooks try to make them similar to the original messages from legit companies, like Amazon or FedEx. Thus, it would help if you remembered the only difference they cannot hide - the sender’s email address. Just keep in mind that delivery messages from Amazon will not be sent from [email protected] - they have an official and genuinely-looking email address for that case.
The last piece of advice, which acts rather as a final remedy, is to use anti-malware software. The most effective way to protect yourself is to combine the additional security software and your knowledge. Proper security tools like GridinSoft Anti-Malware will protect your system from computer viruses, spyware, ransomware, or other threats.
Read also: Polymorphic vs Metamorphic Virus
Frequently Asked Questions
Viruses can destroy your system and steal all the valuable data that it holds. To say that there is a single most vicious virus will be inappropriate. Unfortunately, such merciless viruses up to 10 or more. It all depends on their type; the harm they do is terrible, but each in its way.
In the group of such scarecrows should be included Cascade, which in the late 80s and early 90s made the characters in DOS sink into the bottom of the screen. In contrast, he made a repetitive process, making useless calculations.
AIDS. This is another DOS malware from the early '90s that captured the user's screen and scared its victims that their system was infected with AIDS. In this case, the system should be rebooted, and then deleted all infected files.
Skulls, a Trojan, attacked Symbian mobile OS. Masquerading under legal application, it replaced the icons on the screen with images of crossed bones and skulls and made the standard app unusable for use.
We also can extend the list of the most dangerous viruses with many more specimens, such as Tequila, Rigel, Gruel, and others.
Polymorphic virus. These viruses hide under the guise of altered forms and carefully avoid detection. They do this because of the large number of constantly changing clones.
Resident virus. This beau aims to damage your RAM, files, and motherboard memory; more than that, it will not let you delete it. Yes, that's right, once you find and try to eliminate it, it can still store it inside your OS.
Boot sector virus. This type of virus extends to your device using a USB drive, CD, and floppy disk to go through your hash sector, which is responsible for your operating system and damages your device.
Direct action virus.This virus differs because it is the easiest to create and can spread quickly. It joins many EXE or COM files, then removes itself.