ZeuS Banking Trojan
Zeus Trojan, often stylised as ZeuS, is a banking trojan that appeared in 2007. Being a pretty old malware, it obviously passed through several metamorphosis. In 2010, it became worldwide-known after the FBI report upon the extensive botnet under the rule of Zeus malware, that was managed by a cybercrime group from Eastern Europe. It is also known under the name of ZBot Trojan, or its common detection name – Trojan-Spy.Win32.Zbot. Shortly after the aforementioned report, his creator decided to shut down, and released the source to the public in 2011.
Such a situation could be disastrous for other malware – but that is not the case of ZeuS Trojan. After the code leak, various hackers adopted it, modified it, and started using it under different names. Thus, Zeus is not active itself these days, but numerous offshoots that contain its code remain active. Among the most notorious ones are ZeuS GameOver, Citadel, Terdot, Atmos and Cthonic.
Zeus Trojan overview
Zeus is a classic banking trojan example. Despite the original code of this malware being pretty old, it was ahead of its time. Nonetheless, lack of cybersecurity knowledge at the time of its main activity made things way less complicated. It does not have sophisticated anti-detection mechanisms that could have allowed it to run these days as successfully as it did when it was active. No cunning unpacking, no complicated encryption or obfuscation – in 2007, that was just not needed.
Throughout its lifespan as a stand-alone malware, it saw usage in two key roles – banking trojan and botnet unfolding tool. In fact, stealing banking information was not its sole purpose, as it was rather a full-fledged infostealer rather than a highly-specialised tool. We will have a look at both of these functions.
Delivery methods
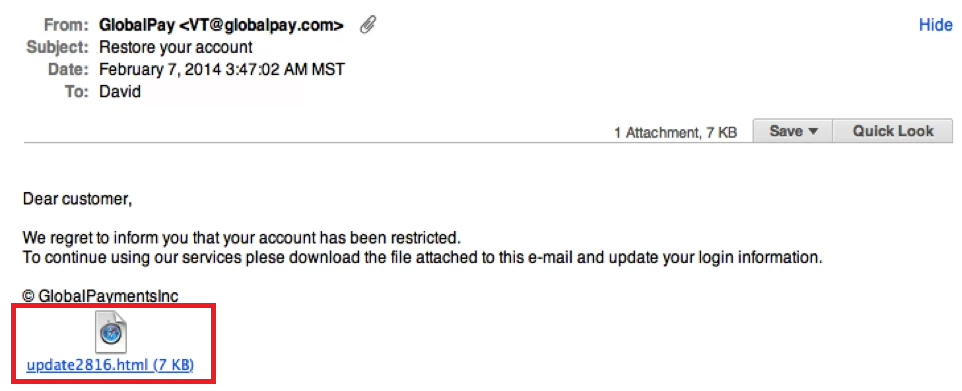
To have a more complete view upon any malware, it is important to trace it from the beginning of its attack. Typical methods for ZeuS Trojan distribution are so-called drive-by downloads and phishing in different forms. The former was commonly implemented in the form of compromised website exploitation. Crooks were luring their victim to such a page, and then forced it to interact with the site – for example, pressing the button or following the other link. That action proceeded with malware installation. These days such action remains possible, but the chances to compromise the website drastically decreased, making that tactic less comfortable to use.
Phishing, on the other hand, remains active even these days, and has only an increase in usage. Email spam became one of the main malware spreading approaches over the last couple of years. Spam campaigns in social media or messengers, on the other hand, are more rare, yet may be more effective. Key target of these actions is convincing the victims to download a certain file and run it. That file may be propagated as a report you were searching for, grocery list, delivery information, useful tool for your PC, and so forth. The file, however, contains a script that forces the connection to the command server and downloads the payload. In the case of Zeus malware, however, the infected file contained the exact payload.
After the initial infection, Zeus was using infected machines to spread malspam to other users. Malware was using either social media accounts and email messages, which contained pretty much the same things as were used to infect the first machine in the chain. That tactic allowed this trojan virus to spread exponentially.
Zeus infection flow
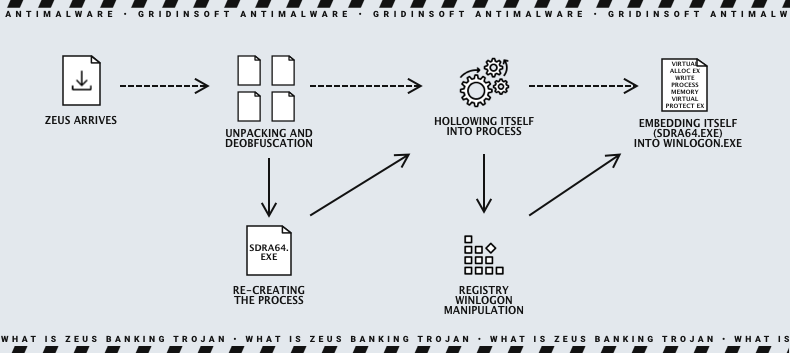
We mentioned that Zeus Trojan was using accounts of its victims to spam other people. Let’s have a look at the way it works in the attacked computer before starting such a self-spreading. Arriving to the system, it generally had its code ciphered and obfuscated. However, it is not about warping the code as hard as it may be done these days. After deobfuscation, it decrypts part of its code that contain the WinAPI elements it needs for running. Then, it is ready for further unfolding.
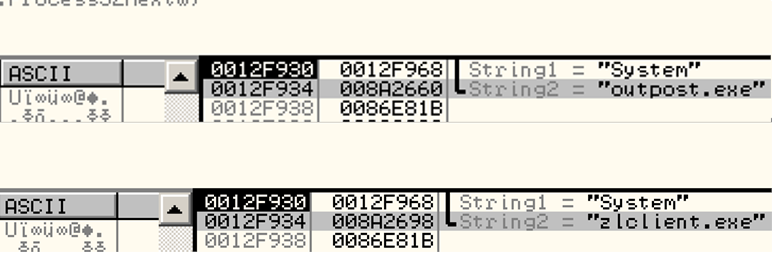
First of all, malware tries to enumerate the processes running in the system. It is needed to find out if the system contains 2 certain firewall apps. If true, malware performs self-destruction. Those are ZoneAlarm (named ZoneLabs at that time) and Agnitum Outpost.
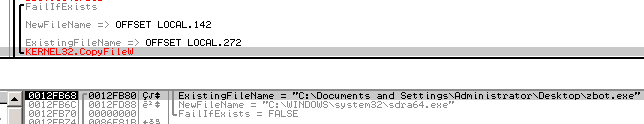
The following actions include the creation of a mutex that prevents from running several malware copies in the system, and spoofing the system file named sdra64.exe. The latter is located in System32 folder; malware removes the original and adds its own copy, hollowing its code into the file. After that, it changes the file properties – sets the attributes to hidden and system values.
To prevent visual identification of the file, malware also changes the file viewing properties in order to conceal the files with aforementioned attributes. Zeus also spoofs the time of sdra64.exe file creation – in order to confuse anti-malware tools. For the same puprose, it adds random section to that file – that changes the file signature, preventing the detection.
Next action is registry editing, which is needed to gain persistence. It adds the path to sdra64.exe to the HKLM\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\Winlogon\ registry hive, exactly, to the Userinit key. This makes it possible to run malware together with the system launch. To inject itself into winlogon.exe process, Zeus allocates memory in this process and writes there data from the bot’s address space. During the latter, it use VirtualAllocEx, WriteProcessMemory and VirtualProtectEx calls.
C&C Communication
After succeeding with unfolding and providing sustainability, it connects to the C&C server. It happens literally in a second following the start-up. Through this connection, the command server provides malware with configuration file in the form of a tiny binary file. The latter is marked with a Content-Type of application/octet-stream data type.
Here comes the first problem that makes Zeus counteraction harder. The URL of the command server is not stable – it is changed in a random manner for almost each sample. Same happens to HTTP GET request headers. Such randomness sharply extends the list of indicators of compromise, making both collecting the indicators and covering all of them way more difficult.
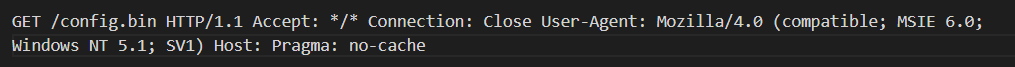
Same does HTTP POST, that follows the previous operations after completing the first communication with C&C. Aside from the randomness of the URL, the exact content that is transferred under this request is encrypted. However, the data returned for this POST request has a specific feature that makes it possible to distinguish and detect. It has an alternative form instead of arriving as HTML data, as the Content-Type parameter stands. Therefore, it is possible to distinguish between genuine packets and ones related to ZeuS.
The initial connection to C&C we described above is followed with numerous operations related to stealing the users’ data. Zeus malware thoroughly scans web browsers, searching first and foremost for banking information. For that purpose, it may additionally grab the cookies and password files from the browser root directory. After this static analysis, it switches to a dynamic approach – tracking web browser activity in order to catch the moment when a victim will open the online banking website. Mainly, this malware was aiming at Internet Explorer and Firefox; the ability to attack the latter was sold as an add-on. Once that happened, malware was starting its action. It was capable of breaking into IE forms, collecting the input that contained login credentials. That practice is even more effective than searching for credentials in browser files, as logging input data that comes directly from the keyboard allows crooks to ignore any encryption.
ZeuS Trojan Botnet Capabilities
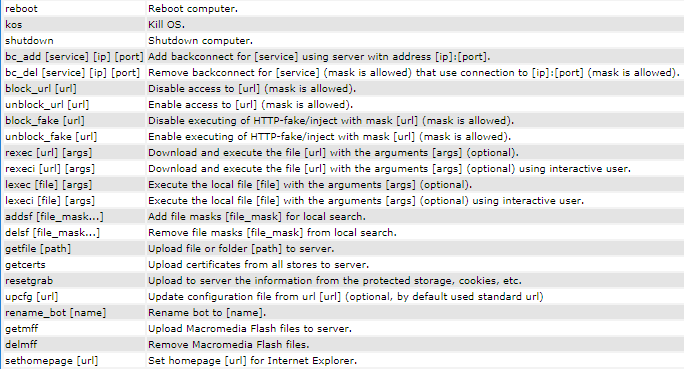
Banking trojan functionality is not the only thing ZeuS is known and loved by cybercriminals. It intendedly features a lot of functionality that allows the crooks to unite the computers infected by Zeus into large networks. Then, these subordinates are used to fulfil the needs of a scoundrel, from a DDoS-attack to creating a fake activity in certain places. Early versions of malware supposed a classic hierarchy structure, when a single C&C rules on hundreds, or even thousands of bots. Later variants included the ability to switch between different architectures, as well as dynamically change the command server domains.
Administrative panel of ZeuS allows quick sorting of the computers present in the botnet. The criterias are OS versions, infection date, NAT and connection statuses. It also offers to find the bots from the needed country, or find the defined bot by its IP address. Thus, you can choose which part of your botnet to use for a certain purpose.
The exact purpose of ZBot botnets generally depends on the wish of their master. However, the ones established by original Zeus variants were used primarily in gaining money for pay-per-visit advertisements. Most often such advertising campaigns touched porn sites, doorway pages and similar semi-legal affairs. Having an extensive botnet is also the ability to earn money by selling or renting it to a third party. Alternatively, hackers may offer to install malware to the computers which already have a residing trojan. Still, that was not the case of Zeus, as only its offspring were modified to carry the downloader functionality.
Zeus Trojan virus pricing
In late ‘00s, organised cybercrime was rather a gimmick than a widespread phenomenon. But Zeus developers took this seriously, and offered a pretty extensive list of tariffs for their malware, that included different variations of functions that can be applied along with the original malware.
- Zeus itself cost from $3,000 to $4,000. This applies to version 1.3.4 – the last version available to purchase before the release of a source code. Contrary to previous versions, this one was spread exclusively by the malware developer.
- Form grabber for Firefox – $2,000. In previous paragraphs, we mentioned that Zeus trojan can grab information from the login forms in Internet Explorer. To do the same trick with Firefox, you should have paid more than half of its initial cost. For that point of time – year of 2007 – Firefox was quickly gaining its popularity, so such an investment was reasonable. Chrome, by the way, never reached even 10% of market share before Zeus shutdown.
- Windows Vista/7 support – $2000. Another feature that costs around a half of the cost of exact malware. Its name says for itself – malware that was initially targeted on Windows XP could receive the ability to run on Windows Vista and 7. The difference between the codebases of XP and more modern versions of that time rendered most old-fashioned malware useless.
- Partial backdoor functionality would have cost $1,500. This application allowed the victim’s PC to be used as a doorway for the transactions, made with the banking cards of this victim. After the first massive outbreaks of carding, banks began tracking the geolocation of the user who attempted to perform a transaction. If there’s no match with the user’s often locations, the transaction (and often the card itself) gets blocked. Through the backdoor, hackers could do all purchases through the computer of this victim, minimising the chance of being detected.
- Live push notifications to Jabber for $500. Once malware found something on the attacked device, it will be visible not only through the admin panel, but also via message in Jabber client. Such a fast reaction time could seriously increase the chances of getting an additional profit. If Zeus had managed to grab session tokens, it was possible to use them to log in and disguise as an attacked user – a very powerful ability if those tokens belong to an online banking site, for example.
- VNC (Virtual Network Computing) capabilities cost an immense $10,000. Such a price was unlocking the ability to use the victim’s computer as it was yours – at any time, for any purpose. That function was pretty useful for operations that required a disguise of a victim. Any authentication available to the victim could easily be used by the hacker, as well as any other application or hardware component. Such a price, for sure, serves as a restriction to prevent using this feature here and there. Only ones who know what for do they need such power will use it properly, without the risk of being trapped.
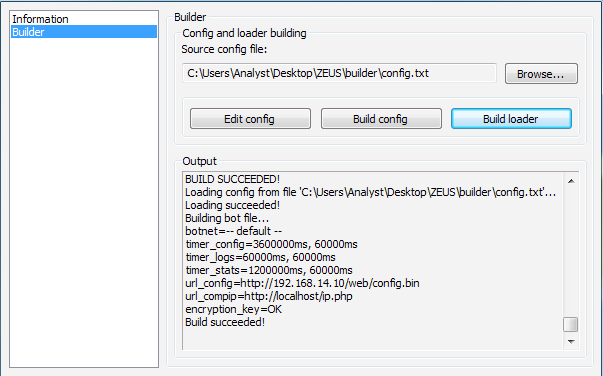
Malware builder
Besides all we mentioned above, Zeus included a malware builder that allowed you to modify malware for your own needs. When compared to modern builders, it lacks code repacking, obfuscation and new sample generation for each new user. All the hackers who purchased malware can access it right away, i.e. it is supplied in a basic kit. Using it, crooks can alter the URL of the configuration file, set up a random delay for execution, modify the config file encryption and specify its decryption key.
If needed, the builder may generate a separate configuration file and initial payload, making it possible to update one element at a time, without changing the other. It features a slight obfuscation of the malware with the use of code encryption, which, however, is decrypted with a single-step operation. Malware master may also adjust the list of banks and their sites malware should look for.
ZeuS 2010 botnet
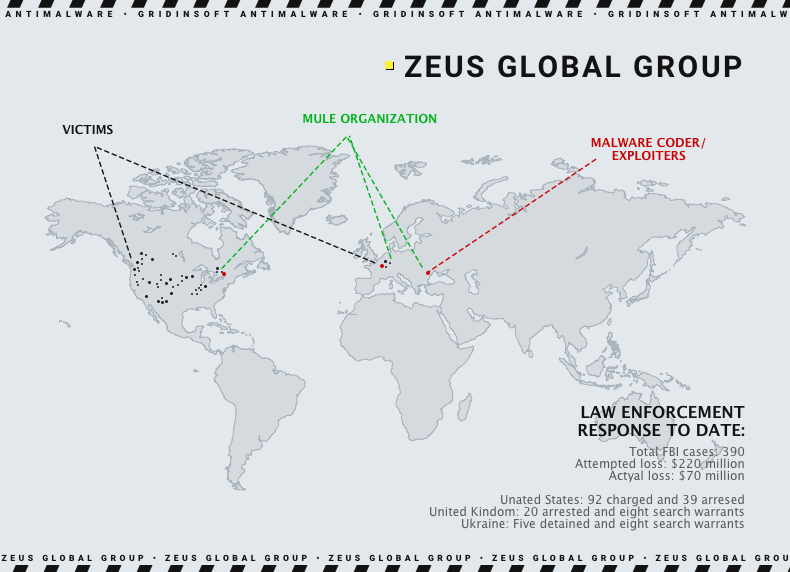
At the beginning of this article, we mentioned that Zeus gained most of its fame in 2010, when FBI released report on a huge cybercrime group, that managed the botnet under the rule of Zeus Trojan. It was accused in stealing over $70 million from bank accounts. Overall, over 100 people generally from Eastern Europe and Russia were evicted. However, threat actors were arrested in New York as well as in Portugal. The group included both malware distributors, some of the developers and so-called money mules – persons who are employed in money laundering. The most notorious thing regarding this botnet was the fact of its integration in U.S, Department of Transformation.
Offsprings
After the release of its source code in 2011, ZeuS malware stopped its own distribution and development. However, that did not mean it has completely disappeared from the radar. Some of the samples of original malware appeared up to 2013, but more and more often crooks get their hands on the source code. Afterwards that code ended up in numerous offshoots, some of which even overwhelmed their predecessor.
ZeuS GameOver Botnet
Initially, Zeus was capable of creating botnets. Yet the functionality was normal for 2007, when it was created, and became seriously obsolete by 2015. GameOver was bearing on the peer-to-peer architecture, a new addition to the malware created by Evgeniy Mikhalovich Bogachev, a Russian hacker. Thanks to this modification, malware became way harder to detect and disarm, as there was no straightforward connection to C&C. Most of the victims reportedly were in the US, United Arab Emirates, India, UK and Italy. The scale of the GameOver botnet forced the U.S. DoJ to announce Operation Tovar, a joint action of enforcement that was called to stop the botnet and capture Bogachev. Half a year later, the FBI announced a reward of $3 billion for information about the hacker – the biggest one at that moment. It was overwhelmed only in 2019 with a reward for another Russian hacker, Maksim Yakubets, chief of the REvil ransomware gang.
Citadel Stealer
Russia is a place of origin to numerous malware, and Citadel is yet another one. Based on Zeus' leaked source code, it appeared soon after its release and managed to keep alive for 6 years - to the year of 2017. Instead of targeting the banking sites, this malware hunted for password management applications. Hacking into one app meant getting hands on all the passwords the victim stored in there. Overall, Citadel malware infected over 10 million devices, leading to >$500 million losses.
Terdot Stealer
Terdot is a direct offspring of Zeus, which inhabited its capabilities of password stealing. However, its range is significantly extended – it aims not only for banking credentials but all it can reach. For that reason it has the stealing module reworked. Another update compared to Zeus is anti-detection measures: Terdot code arrives in a heavily obfuscated form, with the encryption of key elements. Code unpacking takes several steps and requires the libraries kept within the initial payload. Appeared in 2016, it struck people in Canada, Australia, US, UK and Germany. Key spreading ways for this malware is email spamming.
How to protect your computer from banking trojans?
Banking trojans are probably the most unpleasant kind of intruder, if we are not mentioning ransomware. Contrary to more classic spyware, it aims precisely upon online banking accounts, and crooks generally try to withdraw your costs as soon as possible, contrary to carding. In order to avoid giving the crooks even a chance, it is recommended to apply preventive measures.
Stay on the alarm with emails you open. Are you sure the message from Amazon you’ve received the day before is legit? Why did it have such a strange attachment? And why did they ask such details at all? You should ask yourself these questions each time you face something strange in your inbox. Fortunately, email spam is often pretty clumsy, so detecting it is not a problem. Once you see something suspicious about the email – better move it to spam, or delete, and avoid further interaction with its contents.
Be sceptical about the messages in social media. Your favourite messengers and social networks may look like the world of friendship – but impostors wait for you to relax and ignore the security rules. Executable files, archives or documents, wherever they’re posted, should not be trusted. First and foremost, check-up this item with antivirus software or services like VirusTotal. Haste or sense of urgency is what plays for crooks and against you. Only after such an analysis, you may launch the file.
Use a well-made anti-malware tool. Malignant items may slip into your system through different channels, and you may be incapable of tracking them all manually. Thus, antimalware software is a solution to solve this problem. A proper tool, like GridinSoft Anti-Malware, is capable of proactive detection and removal of any malware – thanks to the advanced detection system.