Remote Access Trojan is software that allows unauthorized access to a victim’s computer or covert surveillance. Remote Access Trojan are often disguised as legitimate programs and give the attacker unhindered access. Their capabilities include tracking user behavior, copying files, and using bandwidth for criminal activity.
What is a Remote Access Trojan (RAT)?
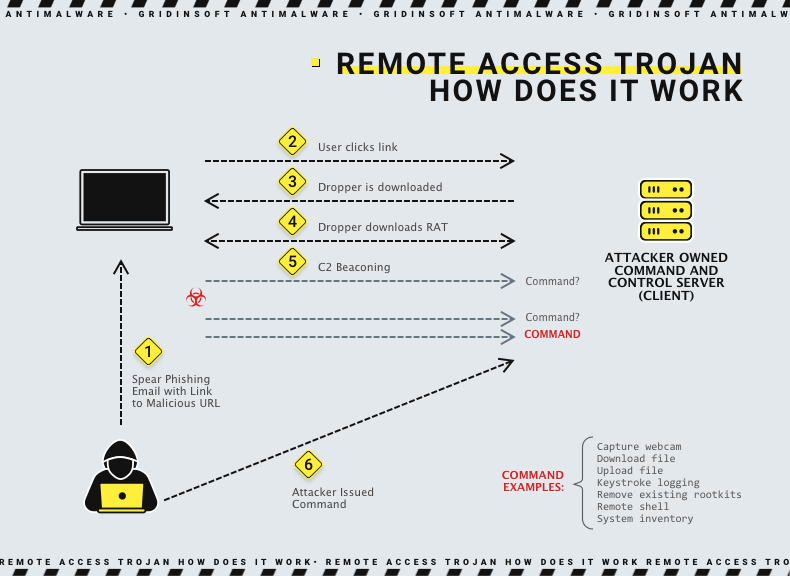
A Remote Access Trojan (RAT) is a malicious program that opens a backdoor, allowing an attacker to control the victim’s device completely. Users often download RATs with a legitimate program, i.e., inside of hacked games from torrents or within an email attachment. Once an attacker compromises the host system, it can use it to spread RATs to additional vulnerable computers, thus creating a botnet. In addition, RAT can be deployed as a payload using exploit kits. Once successfully deployed, RAT directly connects to the command-and-control (C&C) server the attackers control. They achieve this by using a predefined open TCP port on the compromised device. Because the RAT provides administrator-level access, an attacker can do almost anything on a victim’s computer, such as:
- Use spyware and keyloggers to track the victim’s behavior
- Gain access to sensitive data, including social security numbers and credit card information
- View and record video from a webcam and microphone
- Take screenshots
- Format disks
- Download, change or delete files
- Distribute malware and viruses
How does a Remote Access Trojan work?
Like any other type of malware, a RAT can be attached to an email or posted on a malicious website. Cybercriminals can also exploit a vulnerability in a system or program. RAT is similar to Remote Desktop Protocol (RDP) or Anydesk but differs in its stealth. RAT establishes a command and control (C2) channel with the attacker’s server. This way, attackers can send commands to RAT, and it can return the data. RATs also have a set of built-in controls and methods for hiding their C2 traffic from detection.
RATs can be combined with additional modules, providing other capabilities. For example, suppose an attacker may gain a foothold using a RAT. Then, after examining the infected system with the RAT, he decides he needs to install a keylogger. Depending on his needs, RAT may have a built-in keylogging feature or the ability to download and add a keylogger module. It can also load and run an independent keylogger.
Why Remote Access Trojan is Dangerous?
A 2015 incident in Ukraine illustrates the nefarious nature of RAT programs. At the time, attackers used remote-control malware to cut power to 80,000 people. As a result, they gained remote access to a computer authenticated in the SCADA (supervisory control and data collection) machines that controlled the country’s utility infrastructure. In addition, Remote Access Trojan allowed attackers to access sensitive resources by bypassing the elevated privileges of the authenticated user on the network. Thus, an attack using RATs can take on a threatening scale, up to the threat to national security.
Unfortunately, cybersecurity teams often have difficulty detecting RATs. This is because malware typically carries many concealing features, allowing it to avoid any detection. In addition, RATs manage resource utilization levels so that there is no performance degradation, making it difficult to detect the threat.
Ways of using Remote Access Trojan
The following are ways in which a RAT attack can compromise individual users, organizations, or even entire populations:
- Spying and blackmail: An attacker who has deployed a RAT on a user’s device gains access to the user’s cameras and microphones. Consequently, he can take pictures of the user and his surroundings and then use this to launch more sophisticated attacks or blackmail.
- Launch Distributed Denial of Service (DDoS) Attacks: Attackers install RATs on many user devices, then use those devices to flood the target server with spoofed traffic. Even though the attack can cause network performance degradation, users are often unaware that hackers use their devices for DDoS attacks.
- Cryptomining: In some cases, attackers can use RATs to mine cryptocurrency on the victim’s computer. By scaling this action to many devices, they can make huge profits.
- Industrial Systems Compromise: As described above, attackers can use RATs to gain control over large industrial systems. These could be utilities such as electricity and water supplies. As a result, an attacker can cause significant damage to the industrial equipment by sabotaging these systems and disrupting critical services in entire areas.
Remote file storage: Sometimes attackers can use RATs to store illegal content on unsuspecting victims’ machines. That way, authorities can’t shut down the attacker’s account or storage server because he keeps information on devices belonging to legitimate users.
Remote Access Trojan Examples
njRAT
NjRAT is probably the most known and the oldest among remote-access trojans. Appeared in 2012, it keeps getting updates, which adjust its functionality to the modern “standards”, which makes up for its longevity. The reason for this is probably the attention from state-sponsored threat actors – APT36 and APT41 – who use it in cyberattacks almost since its very inception.

Key functionality of njRAT is typical for pretty much any remote-access trojan – it is about providing remote access. The latter is topped up with uploading and downloading files by command, log keystrokes and capture microphone and camera inputs. Some of its variants are also capable of grabbing credentials from browsers and cryptocurrency apps.
One interesting feature of this remote access trojan is its naming. Threat analysts use its original name interchangeably with Bladabindi. The latter is a detection name that Microsoft assigned to this trojan back in its early days. Usually, Redmond changes the naming as the malware gains volume and power, but this did not happen here.
Sakula
Sakula is seemingly harmless software with a legitimate digital signature. However, the malware first appeared in 2012 and is used against high-level targets. It allows attackers to take full advantage of remote administration on the device and uses simple unencrypted HTTP requests to communicate with the C&C server. Additionally, it uses a Mimikatz password stealer to authenticate using a hash transfer method that reuses operating system authentication hashes to hijack existing sessions.
KjW0rm
KjW0rm is a worm written in VBS in 2014 that uses obfuscation, making it difficult to detect on Windows computers. It has many variations; the older parent version is called “Njw0rm”. The malware and all other variants belong to the same family, with many features and similarities in its workflow. It deploys stealthily and then opens a backdoor that allows attackers to gain complete control of the machine and send data back to the C&C server.
Havex
Havex is a Remote Access Trojan discovered in 2013 as part of a large-scale spying campaign targeting production control systems (ICS) used in many industries. Its author is a hacker group known as Dragonfly and Energetic Bear. It gives attackers complete control over industrial equipment. Havex uses several mutations to avoid detection and has a minimal footprint on the victim’s device. It communicates with the C&C server via HTTP and HTTPS protocols.
Agent.BTZ/ComRat
Agent.BTZ/ComRat (also called Uroburos) is a Remote Access Trojan that became infamous after hackers used it to break into the U.S. military in 2008. The first version of this malware was probably released in 2007 and had worm-like properties, spreading via removable media. From 2007 to 2012, developers released two significant versions of RAT. Most likely, this is a development of the Russian government. It can be deployed via phishing attacks and uses encryption, anti-analysis, and forensic techniques to avoid detection. In addition, it provides complete administrative control over the infected machine and can transmit data back to its C&C server.
Dark Comet
Backdoor.DarkComet is a Remote Access Trojan application that runs in the background and stealthily collects information about the system, connected users, and network activity. This Remote Access Trojan was first identified in 2011 and is still actively used today. It provides complete administrative control over infected devices. For example, it can disable task manager, firewall, or user access control (UAC) on Windows machines. In addition, Dark Comet uses encryption, thereby avoiding detection by antivirus.
AlienSpy
AlienSpy is a RAT that supports multiple platforms. This allows payload creation for Windows, Linux, Mac OS X, and Android operating systems. It can collect information about the target system, activate the webcam, and securely connect to the C&C server, providing complete control over the device. In addition, AlienSpy uses anti-analysis techniques to detect the presence of virtual machines. According to the researcher who analyzed the threat, the operator behind the author of the service is a native Spanish speaker, probably Mexican.
Heseber BOT
The Heseber BOT is based on the traditional VNC remote access tool. It uses VNC to remotely control the target device and transfer data to the C&C server. However, it does not provide administrative access to the machine unless the user has such permissions. Since VNC is a legitimate tool, Haseber antivirus tools do not identify it as a threat.
Sub7
Sub7 is a Remote Access Trojan that runs on a client-server model. The backdoor was first discovered in May 1999 and ran on Windows 9x and the Windows NT family of operating systems up to Windows 8.1. The server is a component deployed on the victim machine, and the client is the attacker’s GUI to control the remote system. The server tries to install itself into a Windows directory and, once deployed, provides webcam capture, port redirection, chat, and an easy-to-use registry editor.
Back Orifice
Back Orifice is a Remote Access Trojan for Windows introduced in 1998. It supports most versions beginning with Windows 95 and is deployed as a server on the target device. It takes up little space, has a GUI client, and allows an attacker to gain complete control over the system. RAT can also use image processing techniques to control multiple computers simultaneously. The server communicates with its client via TCP or UDP, usually using port 31337.
How To Protect Against Remote Access Trojan?
As stated above, Remote Access Trojans rely on their stealthiness. Once it has appeared, you will likely struggle to detect it, even if the exact malware sample is not new. That’s why the best way to protect against Remote Access Trojan is to not even give it a chance to run. The following methods represent proactive actions that severely decrease the chance of malware introduction and the possibility of getting in trouble.
Security training
Unfortunately, the weakest link in any defense is the human element, which is the root cause of most security incidents, and RATs are no exception. Therefore, it’s strategy for defending against RATs depends on organization-wide security training. In addition, victims usually launch this malware through infected attachments and links in phishing campaigns. Therefore, employees must be vigilant not to contaminate the company network and jeopardize the entire organization accidentally.
Using multi-factor authentication (MFA)
Since RATs typically try to steal passwords and usernames for online accounts, using MFA can minimize the consequences if a person’s credentials are compromised. The main advantage of MFA is that it provides additional layers of security and reduces the likelihood that a consumer’s identity will be compromised. For example, suppose one factor, such as the user’s password, is stolen or compromised. In that case, the other factors provide an additional layer of security.
Strict access control procedures
Attackers can use RATs to compromise administrator credentials and gain access to valuable data on the organization’s network. However, with strict access controls, you can limit the consequences of compromised credentials. More stringent rules include:
- More strict firewall settings
- Safelisting IP addresses for authorized users
- Using more advanced antivirus solutions
Solutions for secure remote access
Every new endpoint connected to your network is a potential RAT compromise opportunity for attackers. Therefore, to minimize the attack surface, it’s important to only allow remote access through secure connections established through VPNs or security gateways. You can also use a clientless solution for remote access. It does not require additional plug-ins or software on end-user devices, as these devices are also targets for attackers.
Zero-trust security technologies
Recently, zero-trust security models have grown in popularity because they adhere to the “never trust, always verify” principle. Consequently, the zero-trust security approach offers precise control over lateral movements instead of full network access. It is critical to suppressing RAT attacks, as attackers use lateral moves to infect other systems and access sensitive data.
Focus on infection vectors
Like other malware, Remote Access Trojan is a threat only if installed and implemented on the target computer. Using secure browsing, anti-phishing solutions, and constantly patching systems can minimize the likelihood of RAT. Overall, these actions are a good tone for improving security for any case, not only against Remote Access Trojans.
Pay attention to abnormal behavior
RATs are Trojans that may present themselves as legitimate applications but contain malicious features associated with the actual application. Tracking the application and system for abnormal behavior can help identify signs that might indicate a Remote Access Trojan.
Monitoring network traffic
An attacker uses RATs to remotely control an infected computer over the network. Consequently, a RAT deployed on a local device communicates with a remote C&C server. Therefore, you should pay attention to unusual network traffic associated with such messages. In addition, it would be best to use tools such as web application firewalls to monitor and block C&C messages.
Implement least privilege
The concept of least privilege implies that applications, users, systems, etc., should be restricted to the permissions and access they need to do their jobs. Therefore, using the least privilege can help limit an attacker’s actions with RAT.
Are Remote Access Trojans illegal?
Well, yes, but actually, no. It all depends on how and what you use it for. It is not the program itself that makes such tasks illegal. It’s the implementation. You can test and execute if you’ve written a Remote Access Trojan and have a home lab. You can use it if you have written permission from the other party. However, if you use the RAT maliciously, you may face some legal problems. So, to distinguish, professionals use the term “remote access tools” for legitimate access and control and “remote access trojan” for illegitimate access and control.