Password Spraying – quite careless, a rough form of attack. After several attempts to log in, the site begins to block the entrance. But attackers bypass this block; after the first failed attempt, they start to hack other accounts and so on. Password spraying is a kind of cyber attack.
The attacker wants to hack accounts. He selects the most common passwords and their combinations, for example, 1111, password, qwerty, and other unreliable passwords. These password combinations are sprayed into the account database, and those accounts whose users have not made reliable protection on their accounts fall under this attack. In general, it can be called a rand. Because the attacker does not know exactly who has an unreliable password, he tries to attack, and in one such attack, will hack some part of accounts.

How Does Password Spraying Attack Work?
The password spraying attack can be divided into three stages, see below:
- Cybercriminals find or purchase a list of usernames online:
They either look for them or buy them on the Dark Web. Sometimes intruders hack users’ names or emails due to templates found on companies’ websites or through some other templates. - They try different credential combinations until they are successful:
At this stage, attackers often work through an automatic system that selects different combinations of passwords. It is not easy to do this manually. But they are still trying to find the right combination to avoid locking. - They gain access to user accounts:
Well, at this stage, the attacker gets access to the user account, and already there, they are doing what they need: identity theft, selling them, and others.
Password Spraying VS Credential Stuffing
These two attack methods are similar in that both try to affect accounts somehow and capture them. In the first case – this is the spraying of passwords. In the second case – it is the throwing of credentials.
Credential stuffing is a kind of barbaric attack that is based on automated tools. These tools check the usernames and passwords of most of the accounts that are stolen until some account works. In the case of password attacks, the focus is on finding accounts and selecting different combinations of passwords without using any tools.
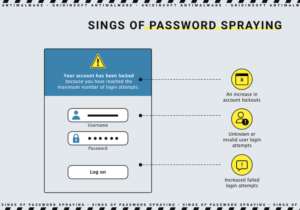
Signs of Password Spraying
You may have been hurt or only at the risk of an attack by a cybercriminal. Then below, we will provide you with a few points through which you will learn them:
- Increasing account blocking.
- Failed and unknown login attempts.
- Increasing Login attempts.
After these signs, you must understand that your account is at risk. Do not neglect this information and read below how to recover yourself from such an attack.
What to Do After Password Spraying Attacks
If you notice something wrong with your account, then immediately use the following steps:
- Change password. The first step is to change the password. Use a more robust and complex password. Make it not easy to crack. Do not risk yourself in this way.
- Contact Cyber Security. Contact your organization’s cybersecurity team. If the willow tree works for the company, you should contact your company’s safety department. You will help them deal with the attack; perhaps not only you have experienced it, inform someone so that no one will get hurt in the future.
- Find out why and find the culprit. Find out why yourself or with the help of security. Next, try to remove the cause of the hack, enter a stronger password, and use two-factor authentication.

How to Prevent Password Spraying Attacks
- Use complex passwords
It is easy to do if you want to. Come up with or learn how to create strong passwords. It is your security. Think about the data that intruders might use for their purposes. - Change passwords periodically
Periodically update your passwords. It can be done once a year or half a year. Try to make your new password different from the previous one. Use symbols and capital letters in it. Make it unique every time, and in any case, do not write it off from anywhere. - Use multifactor authentication
Secure your account with two-factor authentication. When you log into your account, authentication will ask for your phone number or backup email address. It complicates the attacker’s work, as he will need to use more than one user address so that you can warn yourself. - Invest in cybersecurity measures
Never forget about anti-virus software that will protect you in case of an attempt to penetrate your data. Install password managers, anti-virus software, and other data protection software on your device.