Trojan:Win32/Suschil!rfn – Easy Ways to Remove It
If you're seeing Trojan:Win32/Suschil!rfn detected by your antivirus, don't panic. Your computer…
How to Remove Trojan:Win32/Agent from Windows 11
If you're seeing Trojan:Win32/Agent detected by your antivirus, don't panic. Your computer…
PUADlManager:Win32/Snackarcin: What Is It and How to Remove?
PUADlManager:Win32/Snackarcin is a detection of Microsoft Defender that flags an unwanted program…
Heuristic Virus Detection: How AI-Powered Security Catches Unknown Threats
Heuristic virus detection is like having a cybersecurity detective who can spot…
Fake Virus Alert – How to Spot and Remove Scareware Pop-ups
Fake virus alerts are deceptive pop-ups designed to scare you into thinking…
Pegasus Email Scam – Fake “Have You Heard About Pegasus” Emails
The Pegasus email scam is one of those annoying blackmail campaigns that…
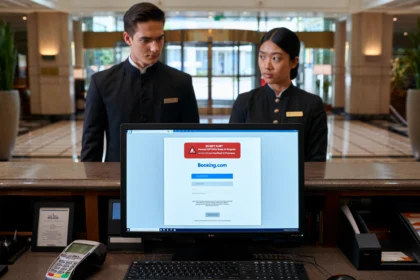
Cybercriminal campaign exploiting Booking.com
Cybercriminals are running a two-pronged attack targeting both travelers and hotel staff…
Trojan:Win32/Leonem – Information Stealer Analysis & Removal Guide
Trojan:Win32/Leonem is an information-stealing threat that targets user credentials and system security.…
Trojan:Win32/Kepavll!rfn Virus Analysis & Removal Guide
Ever had Windows Defender suddenly freak out about some file you're pretty…
Almoristics Application: What It Is & How to Remove Virus Miner
Almoristics Application is a devious crypto miner that's causing headaches for countless…
Truth About 0.31 BTC Xprobit ELON31 Promo Code
The "0.31 BTC Xprobit ELON31 Promo code" promising 0.31 BTC is a…
“Someone Entered Correct Password For Your Account” Email Scam
"Someone Entered Correct Password For Your Account" is a wave of scam…