
What is VPN?
One of the reasons people use VPNs is because they don't trust their ISP. There may well be a suspicion that the provider collects data about its customers and then leaks it for money to third parties. It often happens, especially since even the data that the provider can receive is in great demand. Even the history of visiting sites is enough to target ads by IP addresses. Another option is government censorship, or the ability to access some resources only from certain countries or regions. Let's have a brief explanation of how VPN on the computer allows you to bypass both restrictions.
How Does VPN Work?
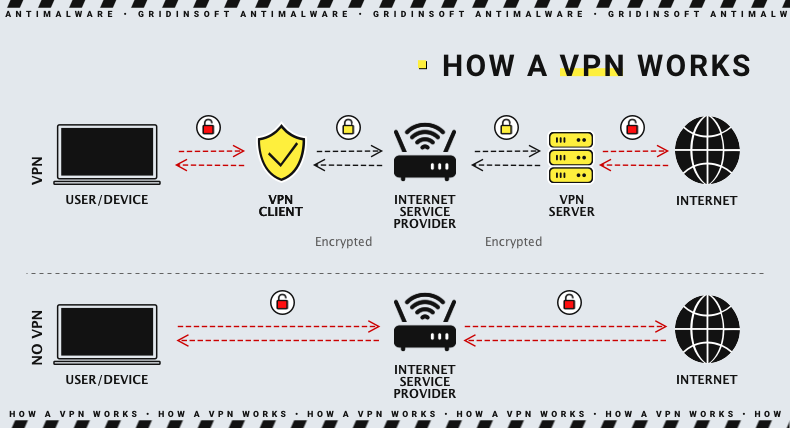
After we figured out a VPN purpose on the computer, let's see how it works. When connecting to a VPN, your browser exchanges public keys with the VPN server and establishes a secure connection with strong encryption. After that, all traffic between the browser and the server is hidden even from your ISP. Then the VPN server, in turn, establishes an encrypted connection with all the sites you intend to visit. Moreover, VPN can present you as a resident of any arbitrary country, assign an IP address, etc.
To have a more detailed understanding of what VPN does to your connection, let’s check out several definitions related to networking. Those are private, public, and local IP addresses. They may look similar but represent two different parts of networking.
Private IP is the IP address given to the Internet router that is used to connect multiple other devices to the Internet. That router may be a network switch or a Wi-Fi router - it will have its private IP address. That address is like the internal IP address that is active and reachable for your home network. When the router sends the queries to the Internet, it uses a public IP.
Public IP addresses are given to your device (or, what is more often, to your network router). It acts as your computer/smartphone identifier to the broad Internet. To decrease the space address use more rationally, NAT was implemented. This technology allowed giving a single public IP address per network instead of giving it to each device. The router remembers the sequence of devices and sites they were connected to and delivers the requests back depending on the local IP of connected devices.
Local IP is the IP given to your device inside of the network. Same to the private IP, it cannot be reached outside the network - until you send the packets specifically to the device. Local IP addresses may have both IPv4 and IPv6 form.
The only thing VPN alters is your public IP address. It is the intermediary between your router and the website you try to connect to. Therefore, the site thinks that you’ve connected it from another place. And you do that - especially if you choose the connection through the VPN server in the other country. That can help you circumvent the network restrictions in your country or ones on certain websites (i.e. the connections ban from the IPs of a certain country). Additionally, connecting to a VPN server is the only thing your provider can record about you. A server to which you will eventually connect will get bogus information about you thanks to the VPN intermediary.
Difference between HTTPS and VPN
Someone may ask: what is the difference between the encryption provided by VPN and HTTPS (Hypertext Transfer Protocol Secure), where SSL certificates are used to exchange secret keys between the browser and the website? The Internet service provider will not be able to read user traffic, will it? Then why use VPN? What is a VPN configuration?
Although the mechanism for creating an encryption tunnel in VPN might be HTTPS is the same, the area of its application in the case of HTTPS is limited to the browser-website channel. Under HTTPS only, you won't hide your attempts to access websites from the ISP. The provider will know which sites you have accessed and be able to track any activity except the encrypted. Moreover, VPN is not only used to secure your outgoing traffic from the provider. With VPN, you can hide and change data about you from the websites you are active on, which is even more important than protection against a hypothetical threat in the face of ISP.
Benefits of VPN
- Protection by secure encryption is only one of the benefits VPN provides. With the help of a virtual private network, you can transfer data and files without fear of them being read by a third party. A brute-force attempt to break the encryption key would let thieves read the data, but it would take them billions of years to break it.
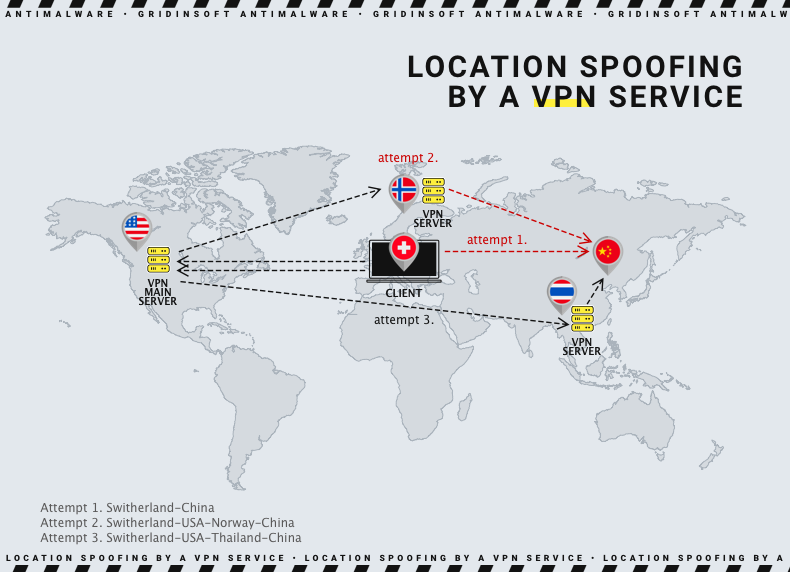
- Another essential feature of the VPN is concealing the user's location and IP address. To a server to which the user connects, the incoming request looks as if it were from another place that is, in fact, randomly or arbitrarily chosen. Besides, VPN services usually auto-clean the logs of their clients' activity. So, this is another level of protection.
- And finally, considering that, besides hiding your actual address, you can choose your apparent location (location spoofing). A VPN can grant you access to content intended only for users from specific regions.
How can VPN help you to circumvent firewalls?
Firewalls are the specific setups or applications that control the Internet access. They may be installed on different levels - local network, ISP or the server. The first may limit the list of sites you can connect to from inside this network and restrict the external connections. An ISP-level firewall controls the list of the websites you can access - such restrictions are generally established according to the legislative changes. Server-level firewalls control the list of IP addresses that can connect to the server - that is done to minimize unwanted traffic.
How can VPN help you break through the firewall? You cannot do much to the firewall on the local network level. VPN supposes the connection through the remote server one level above the Internet service provider. However, the firewall in the local network will not give you a chance even to create a request to the forbidden site. Nonetheless, VPN is very effective against the bans from the provider and the websites you are trying to connect to. When the VPN connection is established, all your ISP sees is the connection to the VPN server. After this connection, the provider cannot forbid the connection to the site since the VPN provider handles all the requests.
The mechanism that allows circumventing IP bans is much easier. Site administrators ban certain IP or the range of IP addresses - usually ones that belong to a certain country. Such a situation happened to Russian sites, which blocked the connection from Ukraine - after a chain of DDoS attacks in March 2022. A VPN connection allows you to change your IP address for the sites you connect - including ones that block your real IP.
IPv4 and IPv6 - what is the difference?
The current Internet addresses are currently running two standards simultaneously. Since both of these standards are about marking the virtual address of your machine in the network, having a hybrid IPv4/IPv6 address is like having two “house numbers”. That paradoxical situation is very atypical for the Internet, where things must be standardized as much as possible. So how did that happen?
IPv4 is the first address format that appeared in 1981. You could have seen those addresses as four numbers, divided by a dot symbol - 203.31.08.99, for example, . It is supposed to be the maximum number of 2^32 (4,294,967,296) devices in the network. Even at the moment of its implementation to ARPANET in 1982, it was clear that this number would be exceeded soon. Even with some tricks that allowed to decrease the speed of address space usage (NAT, for instance), it was hard to stop the growth of the global Internet. Thus, in 1998, IPv6 was proposed as the solution to that problem.
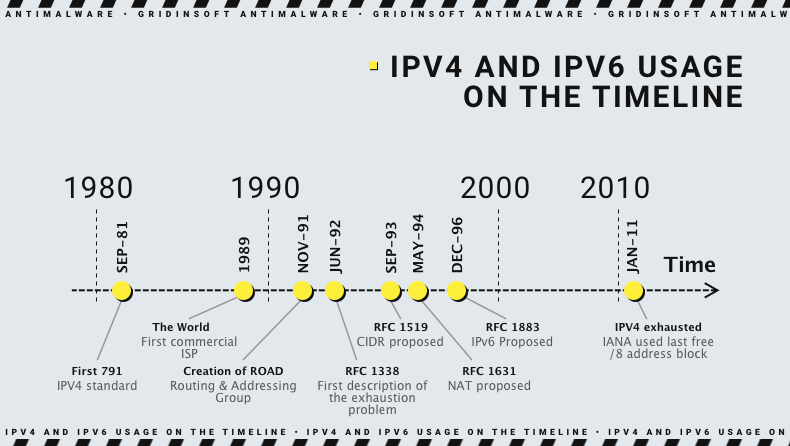
IPv6 has a much bigger address space and the corresponding improvements in the protocol due to the increased address space. The latter buffed from 2^32 to 2^128 - around 3.4×10^38 devices. Despite its development being complete by 1998, it was not used instantly. Thanks to the actions aimed at decreasing the exhaustion of the IPv4 address space, the need for the new space was delayed until the mid-’00s. That also gave a needed time gap to improve the software base and add the IPv6 protocol support to all actual OS versions.
VPN Features
If you have made up your mind to use VPN, look for a service that will feature the whole set of crucial VPN functions:
- IP address encryption: The main point of VPN usage is to hide the user's IP address.
- Protocol encryption: Neither cookies nor search history (or anything like that) should be left unencrypted. Indirect information like that can tell much about the user and make a VPN useless.
- Killswitch: A decent VPN service would sever your connection to any server you were accessing with its mediation in case of a crush of the nexus with the VPN server. The killswitch prevents a "normal" connection from being established at once after the failure of a VPN-server connection.
- Multi-factor authentication Like any other service, VPN uses two-factor authentication to rule out the possibility of cybercriminals compromising your VPN account.
Types of VPN
Here are the main types of VPN technologies. They have much in common but differ in handiness, capacities, and usability.
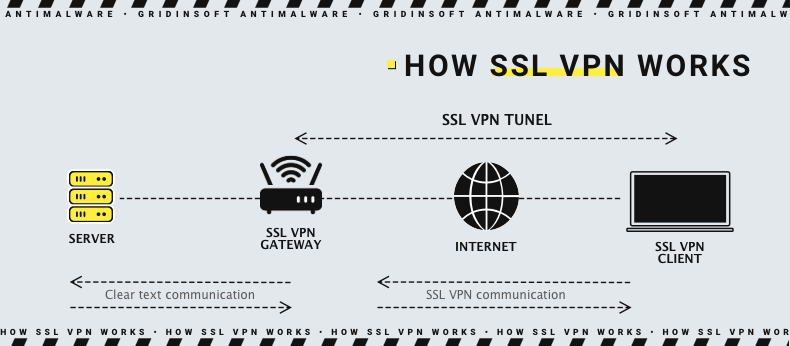
SSL VPN
SSL VPN is often a corporate VPN solution that allows all users to access company files and databases via personal devices. What is needed for this model to work is HTML5 compatible browsers on connecting devices and a VPN encryption applied to the router or a single machine, through which all connections pass.
Site-to-site VPN
A site-to-site VPN is not as flexible as SSL VPN, but it is a good solution for large corporations with many LANs (local area networks) connected within a WAN (wide area network.) Site-to-site VPN will provide secure data transfer throughout the environment.
Client-to-Server VPN
This is the most common and popular VPN type among individuals. The service-providing server is remote, and the user only has to install the software part. As the user connects to the server, the secure connection is established and maintained until the end of the session, keeping all the traffic unreadable to potential interceptors. The user device software allows choosing which region to spoof and other options. The users of desktop computers and mobile devices can benefit from VPN via the right software for their operating systems.
VPN Implementation Methods
You can install a VPN client for yourself as a client, a separate program that you will launch before starting browsing. But this is not the only option. All modern browsers support these add-ons, and VPN service providers have downloadable extensions.
VPN clients for mobile devices are no different from desktop ones, except for their mobile interface.
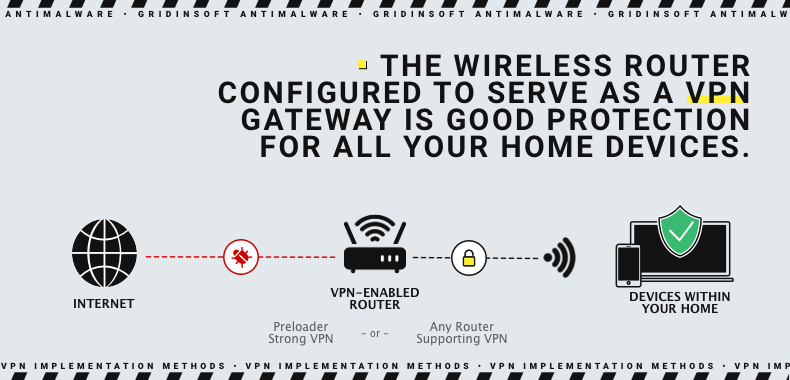
Also, the wireless routers can be configured to connect to a VPN server first before accessing any other resource. Thus, you can protect the traffic of all devices connected to the network through this router.
 As already mentioned here, there are custom solutions for large companies configured specifically for particular workgroups. The main task of such VPNs is to prevent information leakage and eliminate the threat to corporate data from employees connecting to internal networks using their devices.
As already mentioned here, there are custom solutions for large companies configured specifically for particular workgroups. The main task of such VPNs is to prevent information leakage and eliminate the threat to corporate data from employees connecting to internal networks using their devices.
