Identity theft is a rather unpleasant crime. Cybercriminals can not only empty your wallet but also stalk your digital space and may even use it to commit crimes on your behalf. Since criminals invent new tricks daily, keeping yourself safe is pretty hard. So we’ve set together some essential tips to help prevent identity theft online.
Identity theft prevention
Unfortunately, millions of people fall victim to identity theft every year, whether it’s stolen credit card numbers or fraudulent accounts. It’s big business for identity thieves – resulting in tens of billions of dollars stolen each year. Dealing with this problem can be a long and challenging process, so it’s much better if you take steps to avoid it. Below, we’ll show you how to prevent some potential problems.
Use Two-Factor Authentication
Many people are used to storing personal data in one place. This means that if hackers hack into one online service, they can use the information they find to hack into others. For example, suppose your primary email account is compromised. In that case, a hacker could use it to gain access to other services you use by simply requesting password recovery. However, with two-factor authentication (2FA) enabled, a hacker with access to your password still won’t be able to access your most important accounts. Two-factor authentication adds another step in confirming a push notification on your smartphone.
However, if you use the same password for all of your accounts, two-factor email-based authentication won’t help. In that case, the hacker will have access to the confirmation emails. It’s more effective to use an SMS notification or 2FA app-based solution. You’ll need physical access to your phone to log into your account, making it very difficult for hackers to access it. Such security measures are significant when you use services with access to sensitive records, such as bank account information or medical records. However, it is important to be sure in your 2FA provider and the place you’re using it. There are enough cases when a vulnerable mechanism of two-factor auth led to a data breach.
Guard Your Personal Info
Your personal information can be precious to hackers, so don’t give it to strangers. Be careful of people sending you unusual messages. By accessing a friend’s address book, interested people may contact you on their behalf to get more information about you. Many sites also try to gather as much information about you as possible. The problem is that if someone gains unauthorized access to this information, they can impersonate you. You can mitigate this by trying to provide as little information as possible. Don’t give out additional information; sign up for services using a disposable email address. If the site asks you for the information, you don’t want to disclose, vote with your mouse, or sign up elsewhere.
Control what you post on social media
Sharing your messages and photos with your friends on social media is fun. However, you can share them with identity thieves if you’re not careful. Therefore, it’s essential to protect your social networks correctly. Check your privacy settings occasionally, as social media services like to make changes. Be careful about what you publish on social media. Criminals are very careful and will be happy to look through your posts for anything that scammers can use to steal your credentials or hack your accounts.
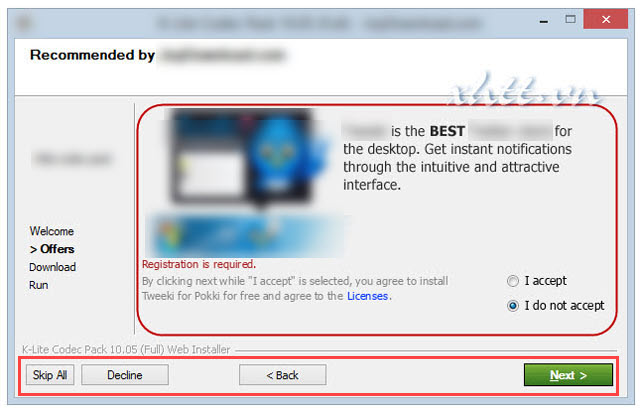
Beware of unwanted downloads
You should also be careful when downloading smartphone apps, especially paying attention to the permissions they ask for. Usually, the system asks what information the new app can access. It’s easiest to click “allow,” but don’t be in a hurry to give the app all the permissions. Also, keep an eye on what you install on your computer, as many software installers trying to bring additional software on your computer will, at best, notify you about it. Malware usually comes from warez versions of hacked applications.
Use a Password Manager
Choosing a password is difficult because sites ask you to enter numbers, symbols, and capital letters everywhere. This is probably why users often choose one password and use it on all sites. However, if someone discovers it, they can take over your entire online life and cause you much trouble. In this case, a password manager comes in handy because it can generate, store and enter long passwords for the services you use on your behalf. If you are tired of trying to remember dozens of long and complex passwords, consider several password managers and choose the one that meets your needs.
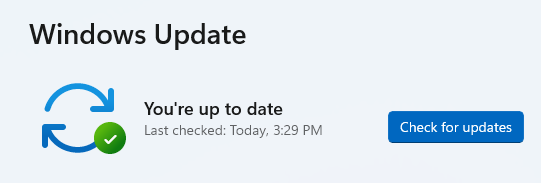
Keep Your Software Updated
Software bugs are found regularly, and these security holes can allow hackers to break into your computer. Keep your OS updated, and use the latest versions of your software. You should also check the privacy settings on your OS and devices. For example, you can adjust email settings to protect your personal or financial information. Since links to images in emails can leak your IP address and other data to hackers, we recommend you disable the automatic display of images in your email client.
Wipe data on the device before disposing of it
Before you recycle or give away your old computer, smartphone, or tablet, immediately erase all data from the hard drive. Used devices often retain outdated data from their previous owners even when they end up in the wrong hands. Next, you should use the device’s built-in data cleansing features, such as a factory reset. That’s enough for a personal device, but if it stores sensitive information, consider using third-party tools to clean it as profoundly as possible.
Use an Antivirus
A successful malware attack is usually the first step in enabling a cybercriminal to execute an identity theft successfully, so you should avoid compromising malware in the first place. Your security software should be able to resist all types of malware. However, such protection only comes with advanced software such as GridinSoft AntiMalware. Usually, free antivirus software is not enough to protect against the many threats that exist on the Internet.
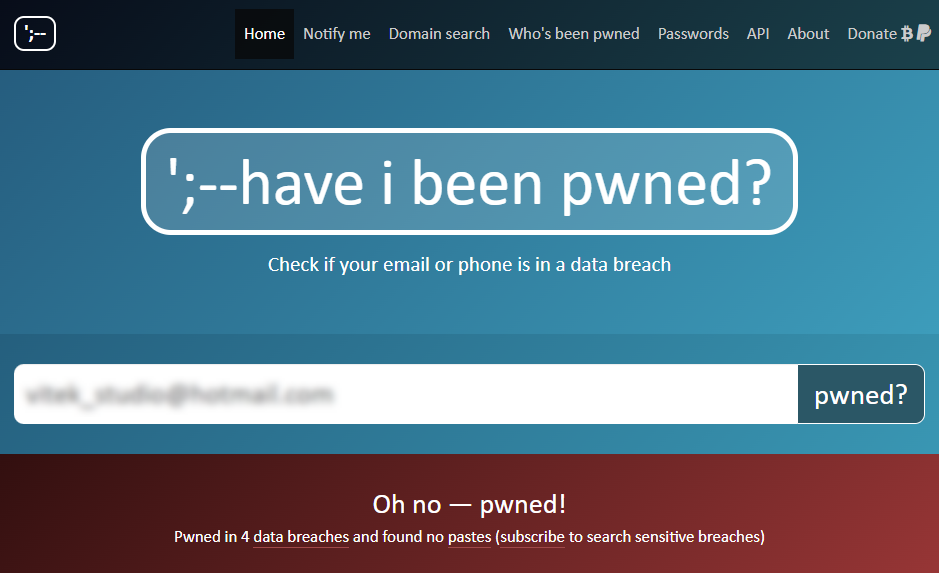
Check for Data Breaches
If you use the Internet, you have multiple accounts on different services. Each new version you create adds another opportunity for an attack if it is not adequately protected. Unfortunately, companies regularly suffer from data breaches, which puts your data at risk of being collected and sold on the Darknet. Even if you’ve done your best to beef up your security, some companies aren’t always as thorough in protecting your personal information. If you suspect your leaked data, you can check it out at haveibeenpwned.com. Just enter your e-mail address to find out if you’ve been hacked.
Beware of using Unsecured Public WiFi
You risk your data using public WiFi networks, such as cafes and airports. Public WiFi networks do not have strong privacy protections, making them popular places for cybercriminals. Passwords to public WiFi networks are available to anyone who asks for them, and hackers are no exception. Because hackers use tools like Wireshark to monitor the online activity of everyone on public networks, they can launch man-in-the-middle attacks, spread malware, and even create malicious WiFi hotspots. The best way to protect yourself on a public network is to use a VPN. A VPN protects your information by encrypting all of your device’s traffic. It also hides your identity on the Internet, allowing you to browse it anonymously. Simply put, a VPN provides an encrypted server and hides your IP address from corporations, government agencies, and potential hackers. It also hides your traffic from the Internet service provider. Encryption adds a layer of security, which is especially relevant for companies that use remote access.
Although the above tips are practical, you cannot protect yourself 100% online or offline. Scammers consistently devise new ways to steal identities but are vigilant. It will keep all risks to a minimum.

![Signs of Identity Theft: How to Prevent It? 1 Signs of Identity Theft: How to Prevent Identity Theft [Short Guide 2022 ]](https://gridinsoft.com/blogs/wp-content/uploads/2022/09/istockphoto-1279316333-612x612-1.jpg)



