Trojan AgentTesla Analysis
| Online Virus Checker | v.1.0.138.174 |
| DB Version: | 2023-09-11 11:06:31 |
Trojan.Win64.AgentTesla.bot
AgentTesla is a Remote Access Trojan (RAT) built on the .Net framework, primarily utilized to acquire initial access to systems. It's frequently employed within the framework of Malware-As-A-Service (MaaS). Within this illicit business model, individuals referred to as "initial access brokers" (IAB) offer their specialized expertise to criminal groups seeking to exploit corporate networks. As an initial-stage malware, AgentTesla facilitates remote access to a compromised system, subsequently permitting the downloading of more advanced secondary tools, including ransomware.
| Checked | 2023-09-11 11:46:24 |
| MD5 | cb1672efed94a51147efbc4586d98b1d |
| SHA1 | 9ecb2031b69741916bfc31adb5940c112ec54c6b |
| SHA256 | c7de60f7c221c6c5cfcf441c5501de5b1006cbea58a07b8f009b230236de406e |
| SHA512 | e18319b95253b76fbe534ed91f82192b3bd6d7c4330079dc2b69d750819f02806d021435440a1106a85112a052721dd7ab112b9942204c05d74069fae060a609 |
| Imphash | 7bdb343cd21cb591ba504d8130502f43 |
| File Size | 6605824 bytes |
Trojan.Win64.AgentTesla.bot Removal
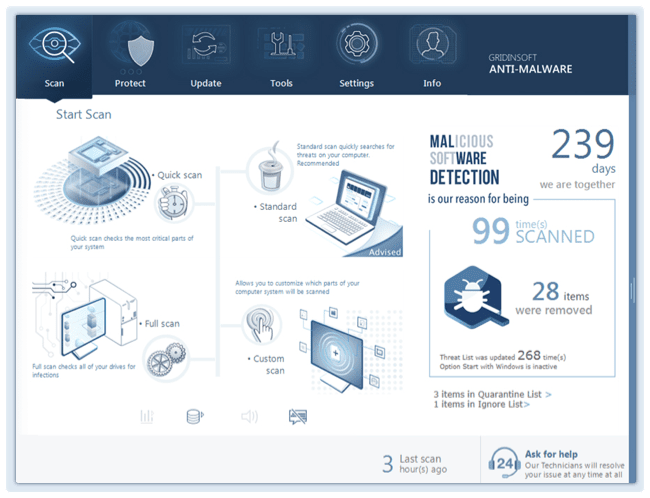
Gridinsoft has the capability to identify and eliminate Trojan.Win64.AgentTesla.bot without requiring further user intervention.
- Start by downloading Gridinsoft Anti-Malware to your computer.
- Double-click on the gsam-en-install.exe file and follow the on-screen instructions to install the program.
- Once the installation of Gridinsoft Anti-Malware is complete, the program will open on the Scan screen.
- Click on the "Standard Scan" button.
- After the scanning process is finished, click on "Clean Now" to remove any detected threats.
- If prompted, restart your system to complete the removal process.
Portable Executable Info
| 1b0b829549a82c1ef20945a5fb04a52e 1667c4ab61865fb99100193d8382e899 2194969696969669 |
|
| Image Base: | 0x140000000 |
| Entry Point: | 0x14006db30 |
| Compilation: | 2023-09-07 07:49:47 |
| Checksum: | 0x0064ff40 (Actual: 0x0065995b) |
| OS Version: | 6.0 |
| PEiD: | PE32+ executable (GUI) x86-64, for MS Windows |
| Sign: | The PE file does not contain a certificate table. |
| Sections: | 8 |
| Imports: | ADVAPI32, ncrypt, KERNEL32, ole32, USER32, api-ms-win-crt-math-l1-1-0, api-ms-win-crt-heap-l1-1-0, api-ms-win-crt-string-l1-1-0, api-ms-win-crt-runtime-l1-1-0, api-ms-win-crt-stdio-l1-1-0, api-ms-win-crt-locale-l1-1-0, |
| Exports: | 1 |
| Resources: | 2 |
Sections
| Name | Virtual Address | Virtual Size | Raw Size | MD5 | Entropy |
|---|---|---|---|---|---|
| .text | 0x00001000 | 0x00076fa8 | 0x00077000 | f459e1c4c5eddc1229df65991633bfdd | 6.60 |
| .managed | 0x00078000 | 0x0031ff58 | 0x00320000 | e635cd1649dc14a10b2e067ac1bc29ba | 5.94 |
| .rdata | 0x00398000 | 0x00236966 | 0x00236a00 | e4f20839fb6f178438fd6ed143e56472 | 6.61 |
| .data | 0x005cf000 | 0x00041618 | 0x00030e00 | 7b6c00ec3253cf23999233a2417134b7 | 3.59 |
| .pdata | 0x00611000 | 0x00038f34 | 0x00039000 | 54c2aeea820113497e9b81860d8dbd7f | 6.46 |
| _RDATA | 0x0064a000 | 0x0000015c | 0x00000200 | 70ba3d18bce9e92ea2a28928bba6da7c | 3.30 |
| .reloc | 0x0064b000 | 0x00014944 | 0x00014a00 | 428fcda99abcc88444fa214e7784585b | 5.46 |
| .rsrc | 0x00660000 | 0x000003b0 | 0x00000400 | b4050856e4f30f8ffa3656f674688cb0 | 2.52 |