Email scam actors constantly try to pick a better disguise for their fraudulent messages. Summer, the time when people commonly plan to take a break from their jobs and travel, gives a wide range of opportunities to scammers. Vacation-related email scams would be on the rise over the next several months – read on to know what to expect from fraudsters.
Vacation-related scams – what are they?
First, let me point out some overall details of these scams. Cybercriminals use topics related to summer vacations to lure out personal information, credentials, or banking information. Since such an activity is typical for most people, the chance to blindly hit someone even without having any additional data is highly probable. That being said, hackers rarely perform blind spamming, preferring to have at least a somewhat relevant pick of targets. Moreover, folks commonly have their attention distorted and vigilance lulled by the overall relaxed mood of pre-vacation days.
In these attacks, crooks generally try to reach their victims on email. Though, nothing stops them from switching to SMS or even phone calls. The key thing here is forcing the victim to follow the link or open the file sent via email or in any other way. This link leads to a phishing site where all action starts. While methods of these attacks are not unique, types of disguise may be quite unusual, which makes them even more difficult to detect.
Examples of Vacation-Related Scams
As I’ve just mentioned, hackers may pick pretty unusual disguises for vacation-related scams. From more common things like posing as a support manager of a booking service, they can switch to whaling attacks and even use compromised business email accounts. Let’s have a look at each one specifically.
1.Your Booking is Cancelled
What can be worse than getting your hotel/apartment rent canceled just before your arrival to the place you are going to stay? That scares and disrupts the entire vacation, so the target will likely haste to respond or follow the instructions. To look more legitimate, scammers may take a disguise of the establishment the victim has the room booked in. After gaining trust, crooks will promptly ask for everything – but most commonly it is money for re-booking another room. They can make up any legend about why it is not possible to pay for the room at the check desk after arrival – and the attacked person will likely eat the bait.
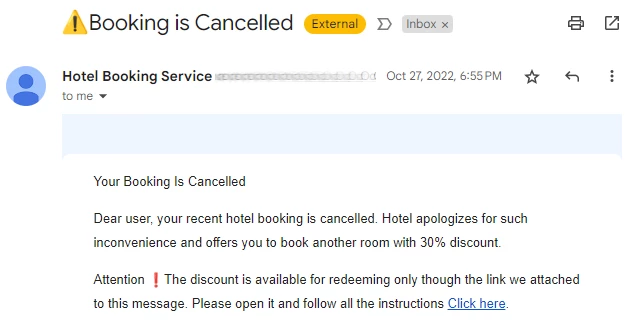
When scammers try to pose as a booking platform, their targets will be different, precisely – your personal information and credentials. To get this information, crooks either put the “sorry card” link to the email bottom, which promises a significant discount. Nonetheless, this link leads to a fraudulent copy of the service’s website, which asks you “to log in to redeem the discount”. Everything you type becomes visible to hackers – so it is the easiest way to say goodbye to your account.
2.Your Flight is Delayed/Cancelled
Probably, an even worse case scenario than the cancellation of a hotel booking is the flight cancellation or delay. Finding where to stay when you are already on the spot is bearable – at least easier to bear than burning a day or two of your vacation. Same as in the case of canceled booking, fraudsters will offer you to buy tickets for a replacement flight through the link. The refund for a previous one is promised in three days – and that is typical for all refunds. But, as you may suppose, neither a refund nor the “replacement flight” will ever happen.
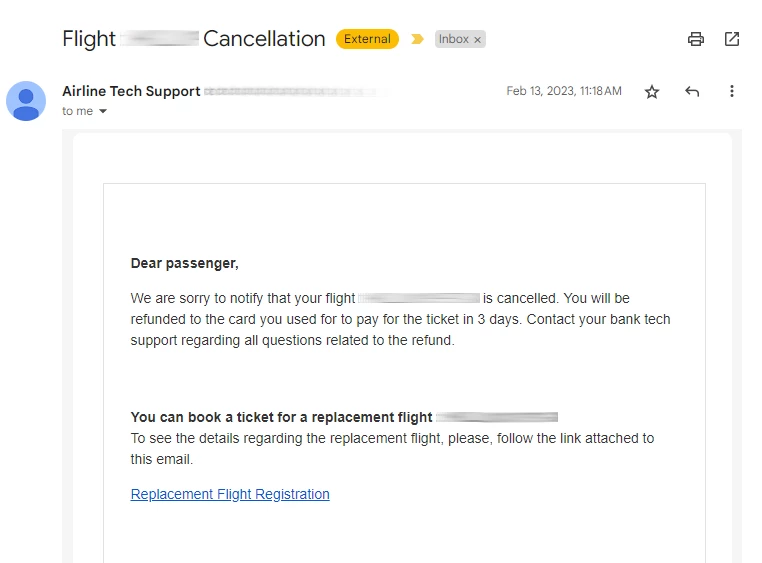
Still, there could be cases when the fraudulent message simply asks you to assign another flight and offers a link to the flight booking page. This page, however, is yet another phishing copy, though it does not try to get your money. Booking a flight always involves sharing quite a bit of information – including real name, passport number, email address, and so forth. In rare cases, both scams may be conjoined – after giving out all the personal details you will see a checkout window. The latter is – you guessed it right – a fraudulent counterfeit of a genuine payment page. It won’t charge you, but will instead collect your banking card info.
3.Confirm Your Vacation Dates (HR Department Scam)
This is a pretty unusual direction of attack, which has increased success chances. Instead of creating urgency around the incoming trip, crooks add importance to the action by disguising themselves as HR dept representatives. In the message, the victim is asked to specify the desired vacation dates in the special form, available by the link. This is a pretty common occurrence in large companies, where HRs try to balance the number of people being on vacation at the same time. Having such a trustworthy disguise, crooks wait for the victim to open the link and log in using their work email. Particularly, hackers hunt for Microsoft emails, as they often contain a wide range of supplementary data. Moreover, these emails are massively used for business purposes, so compromising it opens even more abilities.
Some cases of this email scam offer to download the file “with vacations schedule” and send back the preferred dates. The file – most often a .xlsx table – contains an infected macro that will try to execute as soon as you open the file. This macro downloads and launches malware, most often spyware or backdoor. It will grab whatever sensitive information you have and potentially expose your system to other threats. Attacks via documents with infected macros are exceptionally popular as an initial access vector. If things happen on the corporate PC, hackers will try to infiltrate all systems in the corporation one by one. Data they scraped from previously compromised systems is a great basis for lateral movement.
4.Trip Price Compensation
Isn’t it amazing to receive part of the funds you spent on your trip back? Well, sounds miraculous, and it is – no one provides any compensation for the trips. Dubious emails that offer to follow the link or contact back to retrieve some details may pose as representatives of your company, bank, or booking service you used. In the course of this phishing, crooks try to make you share your personal information, particularly name, email, phone number, and banking details. After retrieving all this stuff, the scoundrels disappear. This type of attack is rare, as it requires scam actors to spend time communicating with victims.
How to Protect Yourself Against Vacation-Related Scams?
Well, phishing and scam email popularity forced the creation of a huge number of different countermeasures. Some fit corporations and some are more effective for home users – let’s check the best approaches from both categories. Vacation-related scams do not differ from other types, thus all this advice remains valid.
Train your employees to detect spam emails. Actually, it is useful for both single users and ones in organizations. There are a few signs hackers can never counterfeit – even when they use a compromised business email. In more common cases, hackers will most likely have an email address different from the one typically used by the organization they mimic. You can find the original address(es) by checking previous emails or visiting the official page.
Use CDR systems. Content Disarm and Reconstruction, or CDR, is a type of auxiliary security system that is designed specifically to prevent malware injection via active content in documents. Wherever the files come from, CDR will analyze them and excise potentially dangerous elements, so you can access a safe document. However, it cannot protect from malicious content available by the link embedded in the message.
Use email protection tools. To counter email-based attacks, security vendors designed add-ons for normal antivirus programs. With it, they can scan the contents of emails, particularly attached files and links, bearing on the normal functionality of the antivirus. This guarantees that nothing will slip through, and contrary to the aforementioned CDR, it secures against phishing links.
Have a reliable anti-malware software inbound. That is, obviously, the step #0 of any actions related to cybersecurity. Even without the email protection functionality, a properly-made antivirus will effectively block malicious macros and prevent phishing page opening. GridinSoft Anti-Malware offers all the needed functionality, and perfectly fits home users – consider trying it out.





