Android is an open operating system. This is an advantage and a disadvantage. Cybersecurity technology experts recently discovered a widespread Android malware campaign. And given the scale of this campaign, it looks likely that it has been fully automated.
A few words about Android malware
As we know, the Android operating system is based on the Linux kernel. It was released in 2008, so malicious users had a chance to study it. Despite the misconception that there is no malware on Android, there is much more of it than we think. Actually, among all other mobile OS, Android became a prevalent target for malware creators. Researchers recently found more than 60,000 apps containing adware. While that’s an impressive number, experts say there are far more. Additionally, malware has been thriving for a long time due to a lack of ability to detect it.
Key place where malware is spread is the Google Play Store. Sluggish moderation, together with loyal rules of app uploads, give the crooks almost a carte blanche. Even though there is a security team which checks programs for malware, they physically cannot cope with the sheer volume of uploads to the platform. That is what makes the default – and trusted – applications market for Android such a convenient spot for malware distribution.
How does Android malware work?
According to the analysis, the campaign promotes adware on Android devices for profit. However, the main problem is that attackers can quickly change tactics and redirect users to other types of malware, such as banking Trojans, to steal credentials and financial information or ransomware.
Hidden Android apps
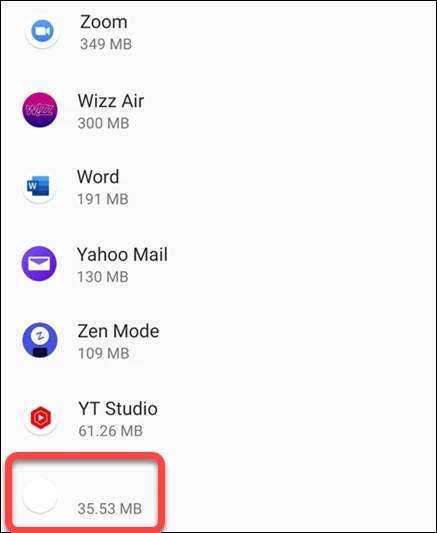
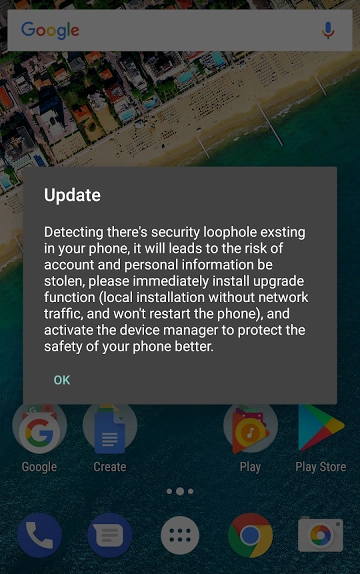
Since API 30, Google has removed the ability to hide app icons on Android once a launcher is registered. So, the malware relies on the user to open the app for the first time. After installation, the app may report a “The app is unavailable in your region. Click “OK” to uninstall”. After clicking “OK,” the app closes but is not uninstalled. Since the malicious application has no icon in the launcher and has a UTF-8 character in the label, it only appears in the list of installed applications. However, it is at the very end by default, so the user is unlikely to pay attention to it. The app registers actions to be called on boot or when the user interacts with the device, and the server can initialize the adware phase at an unknown time interval.
Adware behavior
When the user unlocks the phone, the application gets an adware URL from the server and uses the mobile browser to load the ad. The application uses one of the adware libraries included to render a full-screen WebView of an ad. It serves links, notifications, full-screen videos, open tabs in browsers, and more. During monitoring, researchers noticed the application loading ads from the following domains.
- ehojam[.]com
- publisher-config.unityads.unity3d[.]com
- googleads.g.doubleclick.net
- adc-ad-assets.adtilt[.]com
- wd.adcolony[.]com
- adservice.google[.]com
- gogomeza[.]com
- konkfan[.]com
- httpkafka.unityads.unity3d[.]com
- auction-load.unityads.unity3d[.]com
- kenudo.net
- config.unityads.unity3d[.]com
- pagead2.googlesyndication[.]com
- beahor[.]com
- adc3-launch.adcolony[.]com
Worth noting the domains are not necessarily malware-related.
Redirect
Furthermore, modified versions of official applications may redirect the user to malicious Web sites. For example, when users open a “modded” app and search for something in Google, they may be redirected to a random ad page. Sometimes, these pages pretend to offer the desired mod as a download, but they contain harmful malware. An example user opens hXXp://crackedapk[.]com/appcoins-wallet-mod-apk/download1/website. Immediately they were redirected to hXXp://1esterdayx[.]com/worjt1e6a5efdf4388a83865ddce977639e28e199d821e?q=appcoins%20wallet%20mod%20apk%20v2.9.0.0%20(free%20purchased/premium%20cracked). This website was actually designed to spread malware.
How did Android malware end up on my smartphone?
First, determine how an app can get on a user’s smartphone. There are some ways to install an app on your smartphone:
- Play Store. This method is the safest and most recommended because the download is from an official source.
- Third-party sites and sources. This method allows you to install any app downloaded from any site or obtained elsewhere.
- Zero Day Vulnerability. As the name suggests, this vulnerability was found by attackers, but the developers do not know about it. This is how the Pegasus spyware was spread.
Although all three variants have a chance to download the malicious application, in the first case, the malicious application is likely to be deleted sooner or later. However, in question, apps with adware were not available on Google Play or other official stores. This means the attackers found another way to convince people to install them. Since Android allows you to install any app from any source, attackers disguised the malware as highly sought-after programs. Often these apps cannot be found in official stores or apps that mimic the real ones published on the Play Store. Most often, malicious applications are disguised as:
- Games with unlocked features
- Game cracks
- Cracked utility programs
- YouTube/Instagram without ads
- Free VPN
- Fake videos
- Fake tutorials
- Fake security programs
- Netflix
Since modified applications are a hot commodity, there are entire websites devoted to these applications. Usually, these are the original applications with unlocked functionality or with a lot of game currency. In addition, these sites may contain applications that are visually similar to the real thing. Of course, the download pages may have fake positive reviews and high ratings.
Safety recommendations
The best advice for Android users is to install apps from the official app store. Also, pay attention to the permissions that the app asks for. For example, suppose you have installed Flashlight, and it asks for access to your phonebook and geo-location. Thus, there is every reason to believe it is malware. Don’t download or install any hacked apps. You can also use our Android scanner to check your device for malware.




