In today’s digital landscape, data breaches have become an alarming reality for organizations and individuals. The increasing reliance on technology and the widespread collection, storage, and exchange of personal information have created opportunities for cybercriminals to exploit vulnerabilities. Among the various types of data breaches, third party data breach has emerged as a particularly concerning threat.
What is Third Party Data Breach?
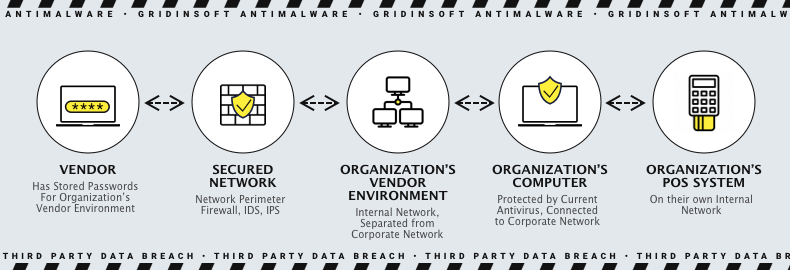
Third party data breach occur when cybercriminals compromise the computer systems of your vendors or business partners and access your sensitive information. It is necessary to note that any vendor in your business network can be vulnerable to such attacks, and studies suggest that approximately 60% of all data breaches are caused by third-party vendors.
Experiencing a security breach can have serious financial consequences for your business, irrespective of the cause. An industry report says the average recovery and remediation cost is more than $7 million. This risk is especially significant for credit card companies, email service providers, and those offering cloud services.
Third-party suppliers, partners, and vendors are crucial to businesses but also vulnerable to cybercriminals. A breach can have severe consequences for everyone involved, not just the industry affected.
Examples of data Breaches Caused by Third-Party Vendors
Cyber attacks like phishing and ransomware have increased during the COVID pandemic as many employees work from home using virtual private network (VPN) connections with varying levels of security. These attacks can result in data breaches, a common occurrence in cybercrime.
To have a better understanding of what types of data can leak, let’s appeal to the examples of third party data breach. Here are some:
- One of the world’s largest electronics companies, General Electric (GE), recently announced that the sensitive information of current and former employees may have been exposed in a data breach at Canon, a third-party company.
- T-Mobile lost control over the personal information of approximately 1 million customers after experiencing a hack on their email provider.
- Health Share of Oregon, an organization that manages healthcare services for Medicaid clients in Oregon, experienced a security breach when an unencrypted laptop was stolen. This resulted in the exposure of personal information belonging to more than 650,000 clients.
- Improperly secured websites and login information storage can lead to security breaches. Recently, a bug on a website called Social Captain allowed unauthorized access to thousands of Instagram usernames and passwords.
These few examples I found are already enough to understand which data categories are endangered. Pretty much everything you share with your contractors – trade secrets, payment information, amounts of supplies and dates of delivery, info about other contractors – all these things may become a subject of the leak. The exact type of information exposed generally depends on the way the third party data breach happened.
Various ways data breaches by third-parties
Organizations must assess and manage the risks associated with third-party relationships and implement appropriate security measures to effectively prevent and respond to these types of breaches:
Supply Chain Attacks
In this attack, hackers exploit a trusted third-party vendor or supplier to gain unauthorized access to an organization’s systems or data. They use weaknesses in the third-party’s infrastructure or software to infiltrate the organization’s network and steal sensitive information.
Cloud Service Provider Breaches
Many organizations trust cloud service providers to store and manage their data. However, if a data breach happens, it could put the data of multiple clients at risk. This kind of breach can happen because of provider infrastructure weaknesses, poorly set up access controls or insider threats.
Outsourcing Partner Breaches
Outsourcing involves hiring a third-party service provider to perform tasks that the company’s employees traditionally did. These tasks can range from back-office support to manufacturing. However, companies need to be careful when outsourcing certain functions or services to external partners because that is a chance of a data breach if the partner’s security measures are inadequate. This can happen if the partner mishandles data, experiences a cyberattack, or has internal security weaknesses.
Payment Processor Breaches
When you purchase with a credit card, a payment processor helps facilitate the transaction between the seller and the bank. They ensure that the seller receives their payment and that everything is processed securely. However, if a payment processor’s security is compromised, it could result in the theft of crucial financial information like personal details or credit card numbers.
Insider Threats
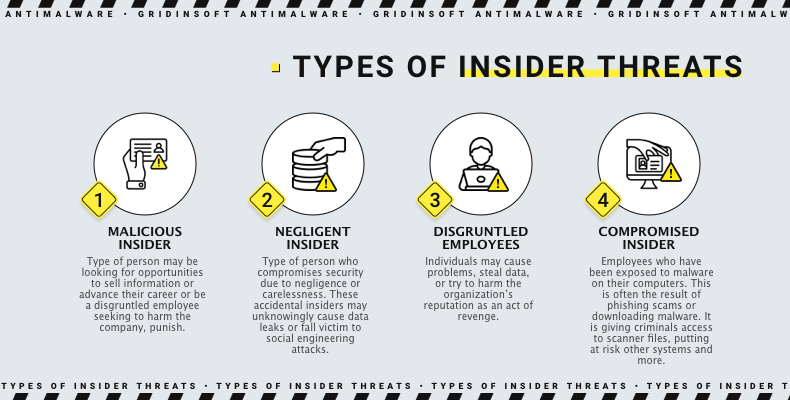
An insider threat occurs when individuals who have permission to access an organization’s network, applications, or databases take harmful actions. These individuals can include former or current employees and third-party entities like partners, contractors, or temporary workers. They may also have gained access through compromised service accounts. In some cases, insiders within third-party organizations may intentionally access or disclose sensitive data without authorization, either for personal gain, malicious intent, or due to coercion.
Preventing Third Party Data Breach
It can be challenging for businesses to hold third-party vendors responsible, mainly if there is no established third-party security policy or program. Ideally, all third-party vendors should adhere to the same strict standards and data security measures that your company has internally.
1. Audit Third-Party Vendors for Compliance
Before bringing on any third-party vendors, discussing risk management requirements with them upfront is important. Some vendors may be close to being audited by partners, so it’s crucial to ensure they are willing to answer questionnaires as part of your due diligence process. If a vendor resists this, they may resist an audit.
Maintaining up-to-date data protection measures is key to building a solid relationship with third-party vendors. Conducting an audit is the best solution to ensure your vendor is following security compliance frameworks and has performed well in previous audits. During the audit, look for any indicators of compromise and assess how well the vendor manages cybersecurity risks.
2. Require Proof of the Third-Party Vendor’s Cybersecurity Program
It’s not enough for the vendor to have an information security program when preventing third-party breaches. They must also demonstrate a commitment to risk management and allocate resources to their vulnerability management program. To ensure this, ask for the vendor’s most recent internal risk assessments, penetration testing results, and compliance frameworks. The vendor must have a strong risk management program, a strategy for mitigating supply chain risks, and a plan for addressing potential data breaches.
3. Adopt a Least-Privileged Model for Data Access
It’s common for third-party data breaches to happen when the provider is given more access than they need to do their job. To improve your network security, enforcing strict access standards for third-party service providers is important. This means giving them the lowest level of access necessary. It’s also crucial to be cautious with sensitive data like Social Security numbers and personal information. By following these least-privileged access standards, you can effectively manage vendor risk and minimize any potential damage from a breach.
4. Adopt the Zero-Trust Network and Data Model
It’s crucial to map, authenticate, and encrypt your network flows to enhance your security ratings. Even if cybercriminals infiltrate a part of your computer system, implementing a zero-trust model prevents them from moving laterally. You can’t trust any entity inside or outside your established network perimeter. To strengthen this framework, it’s essential to enforce multi-factor authentication or biometric identification for all users as part of your cybersecurity protocol.

