According to security researchers, the Clop ransomware group has been looking for a way to exploit a vulnerability in MOVEit Transfer since 2021. Hackers say hundreds of companies have been compromised in recent attacks, with Irish airline Aer Lingus, British Airways, the BBC and British pharmacy chain Boots already confirmed the hack.
What is MOVEit 0-day breach?
A 0-day vulnerability (CVE-2023-34362) in the MOVEit Transfer file transfer management solution became known in late May. All versions of MOVEit Transfer were affected by the problem, and it was reported that attacks on them began as early as May 27, 2023.
The bug itself was a SQL injection that leads to remote code execution. For example, exploitation of a vulnerability can lead to privilege escalation and give third parties unauthorized access to the MOVEit Transfer environment. Attackers used the vulnerability to deploy custom web shells on affected servers, allowing them to list files stored on the server, download files, and steal Azure Blob Storage account credentials and secrets, including the AzureBlobStorageAccount, AzureBlobKey, and AzureBlobContainer settings.
The week before, Microsoft analysts linked these attacks to the Clop ransomware hack group (aka Lace Tempest, TA505, FIN11, or DEV-0950). Among other things, this group is known for the fact that Clop ransomware operators leaked data from two universities.
Old vulnerability
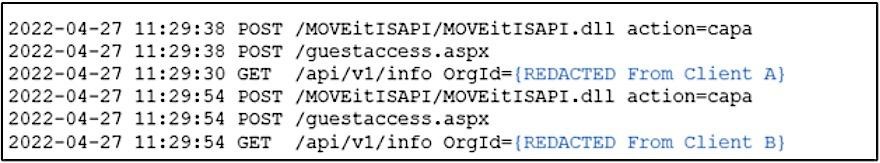
As experts from the information security company Kroll now report, it seems that hackers have been looking for ways to exploit the mentioned zero-day vulnerability long before the start of mass attacks, and more precisely since 2021.
They also discovered that attackers were testing different ways to collect and steal sensitive data from compromised MOVEit Transfer servers back in April 2022.
Automated malicious activity increased markedly on May 15, 2023, right before the start of massive attacks on the 0-day vulnerability.
Victim data collection
Since similar activity was performed manually in 2021, experts believe that the attackers knew about the bug for a long time, but were preparing the necessary tools to automate mass attacks.
Victims of the attack
Hackers told reporters this past weekend that the vulnerability allowed them to break into MOVEit Transfer servers owned by “hundreds of companies.” Although after that the media urged not to take the word of the hackers, unfortunately, some victims have already confirmed the fact of compromise.
Zellis, a UK-based payroll and HR solution provider whose customers include Sky, Harrods, Jaguar, Land Rover, Dyson and Credit Suisse, was one of the first to confirm the breach and leak of customer data.
Some major Zellis customers have already made official statements about the hack. Among them: government agencies in Nova Scotia (including the Health Authority, which uses MOVEit to exchange confidential and classified information), the University of Rochester, British Airways and the BBC, which reported the theft of employees’ personal information and that there were other Zellis customers among the victims – Irish airline Aer Lingus and the British pharmacy chain Boots.
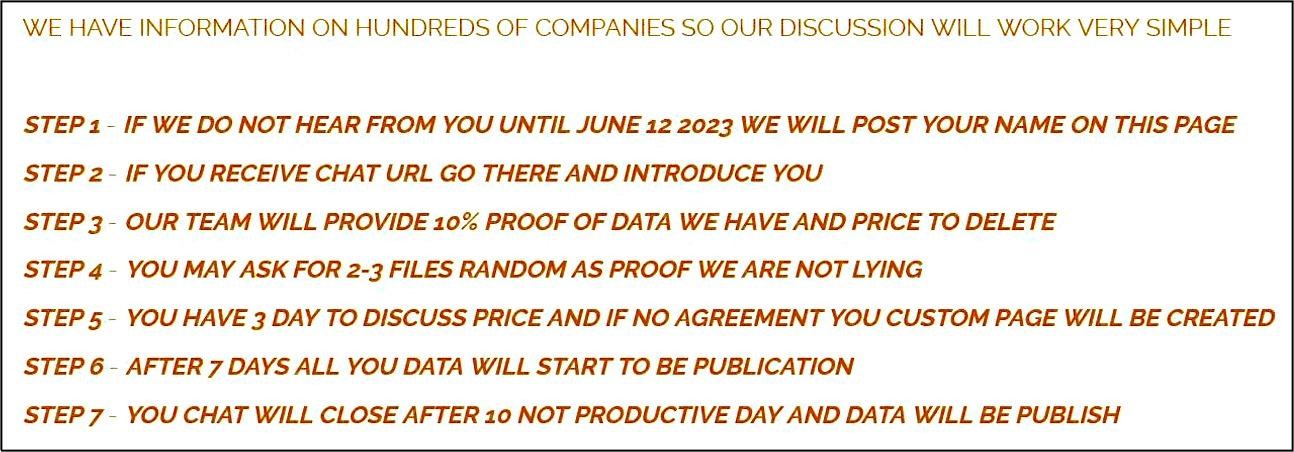
Currently, Clop has not yet begun to publish information stolen from companies. On their dark web site, the attackers gave the victims until June 12, stating that if the companies do not contact them and start negotiations on the payment of a ransom by that time, data leaks will follow.