Among numerous other files, PDFs are considered one of the most convenient to use for read-only documents. They prevent editing the content, yet retain the ability to carry interactive content. But is it totally safe? Can a PDF have a virus? Let’s find out.
Background of PDF Virus
First things first, so let’s see the definitions – just to be sure we have the same things. Under PDF viruses, people most commonly mean any kind of malicious payload embedded into a PDF file. Viruses as a malware type were one of the most massive ones in the mid-00s, which made their name a common noun for any malware. In years to come, viruses were pushed out from a scene with more advanced and self-sufficient malware. Spyware, stealers, dropper malware, and sometimes even ransomware – that’s what’s expected from infected PDFs.
Using legitimate files as a carrier to malicious things is more common for infection continuation rather than initial access. Hackers tend to use PDF (along with JPEG and PNG images) as a disguise for a data package needed to send new guidance to the malware. For users, the file will look like something legit or a nonsense item they got by mistake. Still, nothing stops hackers from using PDF files to spread viruses directly. Let’s check out the main causes of such an occasion.
PDF Virus: Technical details
I pointed out that PDFs can be used for malware distribution. However, they differ from, say, MS Office documents armed with infected macros. Key attack surfaces in PDF documents are related to JavaScript applets and reader applications. While JS is a pretty classic story, vulnerable readers are less common. These days, people tend to use web browsers as PDF readers – and OS use this setting by default. However, some users prefer stand-alone applications, which receive fewer updates, and may contain security vulnerabilities.
JScript
JavaScript, or JScript/JS for short, is a script programming language used massively in web applications and (obviously) scripting. It is overall used in cyberattacks as a way to leak information about the users or redirect them to another page. But having things that reside in the computer’s memory, it is possible to prepare a completely different treat.
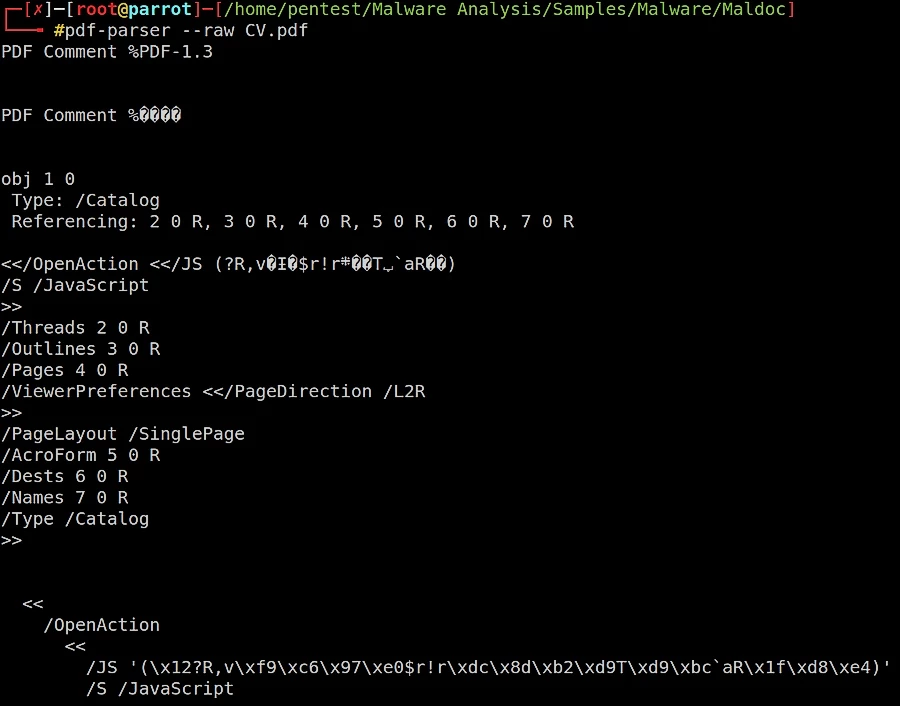
Hackers embed a malicious JS script into the PDF file. By design, JS is attachable to PDF files to make their contents dynamic. That may be used when these documents are displaying the current instructions, but the latter depends on the weekday or other circumstances. However, a malicious instance of the JavaScript applet will run as soon as you open the file. If there is no antimalware software running in your system, the script will flawlessly run and download whatever the hacker asked it to.
Vulnerabilities in the reader application
PDF readers, as I mentioned before, are used less often these days. That actually works against them – seeing less popularity, developers tend to spend less time and effort on making them better. And they have enough things to change, as with time more and more vulnerabilities are getting uncovered.
The content needed to trigger the exploit and give the hackers what they need is commonly embedded in the document’s editable elements. They require your device to run the code that displays the corresponding information. Normally, the code executed in the document should remain in the specific execution environment, called the sandbox. Bypassing it, however, is not a big deal, and hackers are always ready to do that trick and start acting in a live system. Actually, the very essence of the exploitation is quite similar to JScript’s case: a part that stores the active content gets a malicious filling.
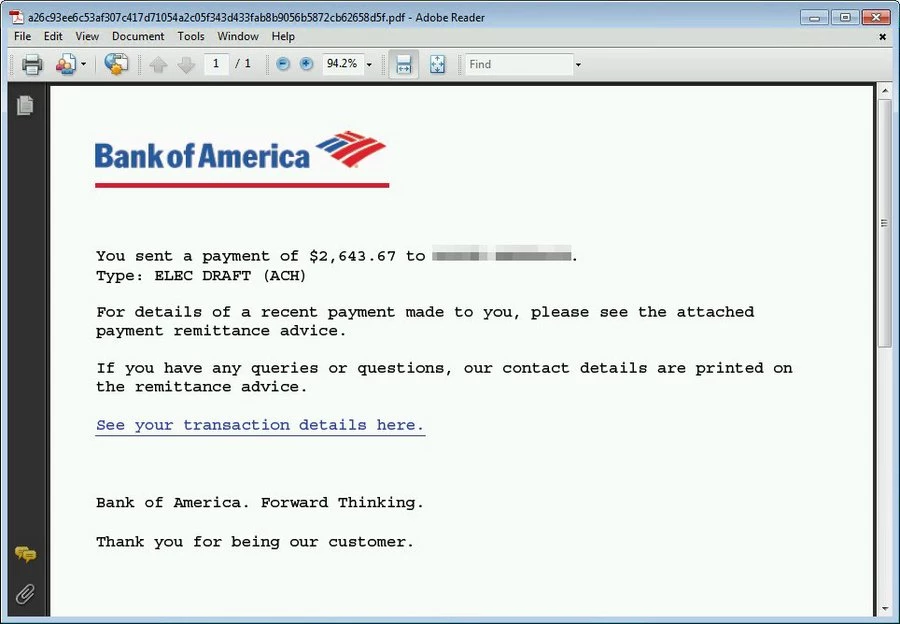
Malicious links in the text
Same as the previous two things, malicious links are also related to the active content. However, instead of relying on code execution, links try to trick the victim into sharing sensitive data. It is a classic example of phishing – but embedded into a PDF file instead of an email message. The key problem (for hackers) here is the fact it does not work automatically – the victim should click the link to make it run. Though after opening the link, it will most likely see a malicious copy of a login page of a website related to the PDF topic.
Risks of PDF Viruses
The risks related to PDF viruses mostly rely on what exactly is happening. When a malicious JScript runs, it most likely contacts the command server to retrieve the payload – i.e. act as a downloader. As an outcome, any kind of malicious program is possible. However, the most common types of malware, in that case, are spyware or stealers. Ransomware, vandal malware, APTs and other things are possible though, but there are no documented cases of these threats being spread in that way.
Vulnerabilities in the reader can be used to both deploy the initial payload and boost the existing one. Same as with JScript applets, they can be the source for any malware – everything depends on the choice of hackers. When it comes to boosting the already running payload, everything depends heavily on the type of a used exploit. Privileges escalation breaches may be used to make malware run; arbitrary code execution vulnerabilities can initiate the connection to a command server to get additional instructions.
Phishing threats are less likely to be related to malware infection. The key thing most phishing operations aim at is the victim’s personal information. The aforementioned malicious link will try to resemble a website you know, and will likely ask you to type login credentials or certain info about yourself. The reasons to follow the instructions will be mentioned in the PDF body.
How to avoid infected PDF files?
Preventive, and the most effective way to avoid facing malicious PDF files is to avoid interacting with questionable things at all. PDFs that contain viruses are unlikely to appear on official websites, genuine emails, and stuff like that. Strange emails sent by a stranger rather than a company, that ask you to open the attached file or a link to a third-party website – that is what you should look for and avoid. For both individuals and companies, being aware of what attacks to expect is essential.
Obviously, it may not be an easy task when you have to deal with dozens and hundreds of emails each day. That case requires a counteraction of another kind – reactive. If you cannot prevent a malicious file from making its way to your system, then it is vital to be able to stop one when it appears. There are several types of software solutions that suit that case.
Content Disarm and Reconstruction (or CDR) will fit organizations that have extensive networks. CDR solutions control the launched files and excise the active content which can be malicious. They may apply that blindly to all files, as well as have a detection system that distinguishes good from bad.
Anti-malware software is a more all-encompassing solution that can effectively detect and stop the execution of malicious code. PDF, however, is a bit troublesome, as some antivirus software considers it safe and ignores it completely. GridinSoft Anti-Malware is a different story – it offers a top protection rate against any kind of threats – even cunning things like a PDF virus.





