
Advanced Persistent Threat
What is an Advanced Persistent Threat (APT)?
An Advanced Persistent Threat (APT) is a prolonged, targeted cyberattack carried out by well-resourced attackers, often nation-states or state-sponsored groups, who gain and maintain unauthorized access to a network for an extended period. These sophisticated threat actors deploy multiple attack vectors, advanced evasion techniques, and custom malware to access and extract sensitive information while avoiding detection.
According to Microsoft Security, APTs are typically directed at organizations with valuable information, such as national defense agencies, manufacturing companies, and financial institutions. Rather than quick "smash and grab" operations, these attacks emphasize stealth and persistence to maximize long-term intelligence gathering.
Key Characteristics of Advanced Persistent Threats
Core characteristics that distinguish APTs from conventional cyber threats
Advanced Persistent Threats are widely regarded as the most formidable cyber hazards, demanding significant resources for detection and prevention. These attacks are distinguished by several key characteristics:
- Advanced Techniques: APTs employ sophisticated tools, often including zero-day exploits and custom malware designed specifically for the target.
- Persistent Access: Unlike conventional attacks, APTs establish and maintain long-term access to compromised systems, sometimes for years.
- Skilled Adversaries: These attacks are conducted by well-funded, highly skilled threat actors, often with nation-state support.
- Targeted Approach: APTs focus on specific organizations with valuable data rather than opportunistically attacking random targets.
- Stealthy Operation: Attackers prioritize remaining undetected through sophisticated evasion techniques and careful operational security.
- Data-Focused: The primary objective is typically intellectual property theft, espionage, or data exfiltration rather than immediate financial gain.
- Multi-Phase Execution: APTs follow a methodical process involving reconnaissance, initial compromise, persistence, lateral movement, and data exfiltration.
APTs distinguish themselves from ordinary cyberattacks through their sophisticated nature, resembling special operations rather than common automated assaults. These campaigns rely on a multitude of tools, both malicious software deployed by attackers and legitimate programs present in the targeted system. Unlike automated ransomware attacks, APTs are executed with precision and patience, emphasizing persistence and long-term presence within the infected environment.
Advanced Persistent Threat (APT) Attack Lifecycle
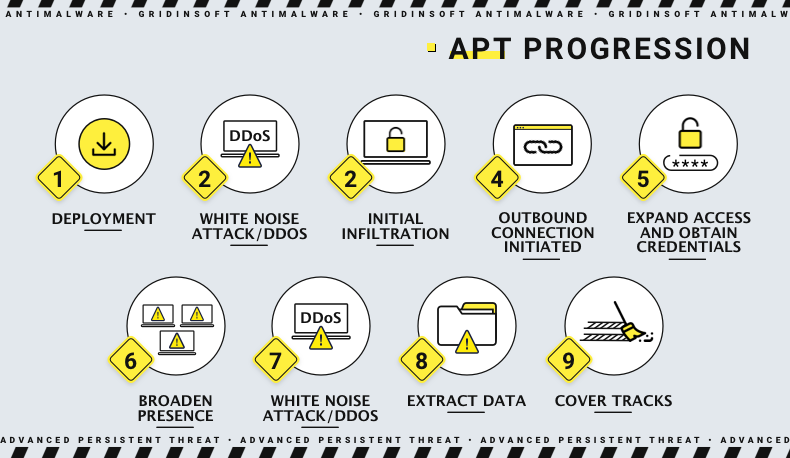
The lifecycle of an advanced persistent threat campaign
APT attacks typically progress through three main stages: infiltration, expansion, and data exfiltration. Throughout the attack, threat actors aim to inject malware, establish persistence across the environment, and ultimately extract valuable data. Each stage involves specific techniques and tools, though the final payload often includes backdoors, remote-access trojans, spyware, or combinations of these. To illustrate these concepts, we'll reference a real-world case from early 2026 where North Korean hackers targeted the Russian diplomatic sector using Konni RAT.
Stage 1: Malware Infiltration
The initial compromise phase involves gaining a foothold in the target network through various methods. According to Microsoft Threat Intelligence, modern APT infiltration techniques include:
- Spear Phishing: Highly targeted emails with malicious attachments or links, tailored to specific individuals within the organization
- Supply Chain Attacks: Compromising trusted third-party software to distribute malware to targets
- Exploitation of Public-Facing Applications: Leveraging vulnerabilities in web applications, VPNs, or other external services
- Valid Accounts: Using stolen credentials to access systems legitimately
- Watering Hole Attacks: Compromising websites frequently visited by the target organization's employees
In the Konni RAT attack case study, North Korean threat actors executed a textbook spear-phishing operation. They disguised an email to the Russian embassy in Indonesia as a New Year's greeting with an attached malicious file. The attackers cleverly spoofed the email address to resemble "@mid.ru" – slightly different from the legitimate "@mid.rf" but similar enough to deceive recipients, especially during pre-holiday periods when vigilance might be reduced.
Infiltration Sequence
The infiltration process typically follows a sequence designed to evade detection:
- Initial access vector delivers initial payload (like a dropper or downloader)
- Payload connects to command and control (C2) infrastructure
- Secondary, more sophisticated malware is downloaded and executed
- Anti-detection measures are implemented (disabling security tools, clearing logs)
- Persistence mechanisms are established to maintain access
In the Konni APT attack, the malicious attachment (a .zip archive) contained a script that connected to the threat actors' command server and downloaded the remote-access trojan installer. While embassy staff viewed a seemingly innocent congratulatory image, the actual malicious activity occurred silently in the background. This multi-step approach is deliberately designed to obfuscate security logs and eliminate evidence of the intrusion.
Stage 2: Malware Expansion
Once attackers establish their initial foothold, they move laterally through the network to expand their control and access additional resources. Compromising a single computer is rarely the end goal, even if it's a domain controller. If the initial access point has limited privileges, attackers will attempt to escalate privileges to execute malware with administrative rights.
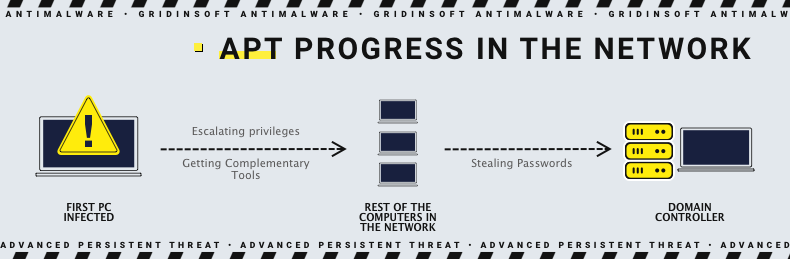
APT lateral movement progression in a corporate network environment
Privilege escalation is a critical phase that typically requires exploiting vulnerabilities. Well-prepared threat actors will have researched the target environment to identify specific exploitable weaknesses. After obtaining elevated privileges, attackers can:
- Create additional administrator accounts on other devices
- Move laterally to access more valuable systems
- Deploy additional tools across the network
- Access and compromise authentication systems (like domain controllers)
- Establish multiple persistence mechanisms
The motivation for expanding malware presence across the network is straightforward: the more systems are compromised, the more data can be accessed and extracted. This reality underscores the importance of network segmentation, enhanced protection for critical systems, and continuous monitoring. Even sophisticated APT actors may resort to more detectable tools like brute force utilities when subtle approaches fail, particularly after disabling security controls on individual systems.
Stage 3: Data Exfiltration
The term "persistent" in Advanced Persistent Threats refers to the attackers' determination to maintain long-term access to the compromised environment. The ultimate objective of most APTs is to gather valuable data over time. However, exfiltrating large volumes of data poses detection challenges, as even with disabled security solutions, network administrators might notice unusual outbound traffic patterns.
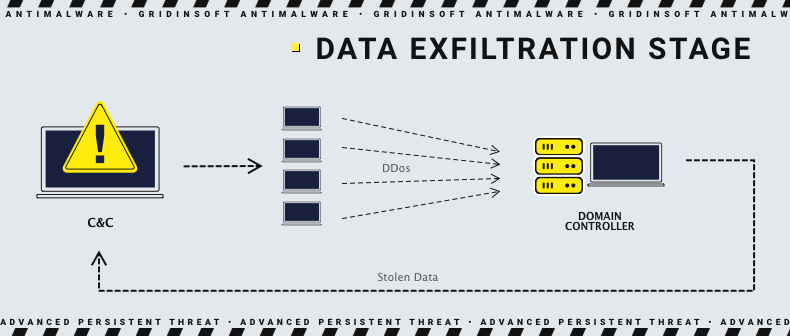
The final stage of an APT attack: Data exfiltration
To maintain stealth during the data exfiltration phase, APT operators employ various techniques:
- Data Obfuscation: Encrypting, compressing, or otherwise disguising stolen information
- Traffic Manipulation: Creating "noise" through DDoS attacks or generating numerous meaningless commands to mask the actual data transfer
- Protocol Abuse: Using legitimate protocols like DNS, HTTPS, or WebSockets to tunnel data
- Scheduled Exfiltration: Transferring data during periods of normal high network activity
- Staged Extraction: Moving data to internal collection points before external exfiltration
While maintaining stealth is typically prioritized, in certain scenarios, APT operators may conduct more overt exfiltration if they believe the value of the acquired information justifies the risk of detection. In some cases, threat actors may deploy ransomware as a final act, either to monetize their access or to destroy evidence of their activities.
Exploring the Most Notorious APT Groups
As the threat landscape evolves, certain Advanced Persistent Threat (APT) groups stand out for their sophistication, persistence, and strategic targeting. These groups, often associated with nation-states or well-organized cybercriminal entities, employ advanced techniques to compromise and infiltrate high-profile targets. Understanding these notorious APT groups is crucial for organizations seeking to enhance their cybersecurity defenses.
APT29 (Cozy Bear)
APT29, commonly known as Cozy Bear, is a sophisticated threat group attributed to Russia's Foreign Intelligence Service (SVR). Operating since at least 2008, APT29 has consistently targeted government networks in Europe, NATO member countries, research institutes, and think tanks. The group gained international attention for compromising the Democratic National Committee in the summer of 2015.
In April 2021, the United States and the United Kingdom officially attributed the SolarWinds supply chain compromise to the SVR, explicitly referencing APT29 along with its other known designations. Industry reporting has also used alternative names such as UNC2452, NOBELIUM, StellarParticle, Dark Halo, and SolarStorm in connection with this campaign.
Key characteristics of APT29 include:
- Targets: Government organizations, political groups, think tanks, and defense and geopolitical research institutions
- Global Operations: Activities observed across multiple countries including Germany, South Korea, Uzbekistan, and the United States
- Advanced Capabilities: Evolving cryptographic protection and sophisticated anti-detection techniques
- Malware Toolkit: Includes components with similarities to MiniDuke, CosmicDuke, and OnionDuke
According to Microsoft Threat Intelligence Center, APT29 demonstrates exceptional operational security, sophisticated malware development capabilities, and adaptive tactics that evolve to counter detection measures.
APT28 (Fancy Bear)
APT28, also known as Fancy Bear, is a highly sophisticated cyber espionage group believed to have ties to Russia's General Staff Main Intelligence Directorate (GRU), specifically the 85th Main Special Service Center (GTsSS) military unit 26165. Operating since at least 2004, APT28 has played a significant role in various cyber operations aligned with Russian strategic interests.
APT28 gained global attention for its involvement in high-profile cyber operations:
- 2016 U.S. Presidential Election: Compromised the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee
- 2018 Indictments: Five GRU Unit 26165 officers associated with APT28 were indicted by U.S. authorities for cyber operations conducted between 2014 and 2018
- Olympic Games Targeting: Conducted operations against anti-doping agencies following Russian doping scandals
Key features of APT28's operations include:
- Targeted Espionage: Focuses on entities in the U.S., Europe, and former Soviet Union countries, including governments, militaries, defense organizations, and media entities
- Information Operations: Increasingly engages in strategic information operations, including the theft and strategic leaking of internal data to support political narratives
- Technical Sophistication: Employs custom malware frameworks and zero-day exploits
APT28 is known by numerous aliases including FANCY BEAR, STRONTIUM, Sofacy, Sednit, and TsarTeam.
APT34 (OilRig)
APT34, also known as OilRig, is a suspected Iranian threat group engaged in cyberespionage activities targeting the Middle East and international entities since at least 2014. The group's operations span various sectors, including financial, government, energy, chemical, and telecommunications. APT34 is known for its strategic and systematic targeting, often employing supply chain attacks to exploit trust relationships between organizations.
APT34 specializes in the collection of sensitive intelligence within the Middle East. Key characteristics include:
- Targeted Sectors: Government agencies, critical infrastructure, telecommunications, and regional entities
- Attack Techniques: Spear phishing campaigns and custom malware tools
- Resource Sophistication: Operations suggest access to significant resources and technical capabilities
The group's tactics include social engineering, exploiting human vulnerabilities, and occasional use of recently patched vulnerabilities during the delivery phase of their attacks.
APT34 is known by various aliases including Cobalt Gypsy, Helix Kitten, and IRN2.
APT41
APT41 is a unique threat group that blurs the line between state-sponsored espionage and financially motivated cybercrime. Assessed by researchers as a Chinese state-sponsored espionage group that also conducts financially motivated operations, APT41 has been active since at least 2012. The group targets a wide range of industries, including healthcare, telecommunications, technology, and the video game sector across at least 14 countries.
APT41 is known by various aliases including BARIUM, WICKED PANDA, and BARIUM, with activities that overlap with public reporting on groups like Winnti Group.
The group employs a diverse toolkit including:
- BLACK COFFEE: Multi-purpose tool for reverse shells, enumeration, and command-and-control communications
- China Chopper: Widely used web shell providing persistent access
- Cobalt Strike: Commercial penetration testing tool repurposed for malicious activities
- Gh0st RAT: Remote Access Trojan for comprehensive system control
- Mimikatz: Credential theft utility for obtaining plaintext Windows account information
- PlugX: Modular Remote Access Trojan
- ShadowPad: Sophisticated modular backdoor used in command-and-control communications
APT41's dual nature as both an espionage actor and financially motivated group makes it particularly notable in the threat landscape.
APT24 (PittyTiger)
APT24, also known as PittyTiger, is associated with Chinese state-sponsored cyber activities. This group has been linked to various cyber-espionage campaigns targeting Southeast Asian governments, military entities, and organizations in the technology and healthcare sectors. APT24 is known for using custom malware and employing tactics such as spear-phishing to gain unauthorized access.
The group has targeted a diverse range of industries, including government, healthcare, construction and engineering, mining, nonprofit, and telecommunications.
Associated Malware: PITTYTIGER, ENFAL, TAIDOOR
APT22 (Barista)
Attributed to Chinese state-sponsored actors, APT22 (Barista) has been involved in cyber-espionage campaigns targeting organizations in Japan and other East Asian countries. This group is known for leveraging spear-phishing emails with malicious attachments to compromise its targets. APT22's primary objectives include gathering intelligence and sensitive information from strategic sectors.
APT21 (Zhenbao)
APT21, also known as Zhenbao, is associated with Chinese state-sponsored cyber activities. This APT group has been involved in targeted attacks against organizations in the aerospace, defense, and technology sectors. APT21 is characterized by its use of advanced malware and techniques for persistent access, emphasizing long-term information gathering and espionage operations.
APT20 (Twivy)
Aliases: Crawling Taurus, TH3Bug, VIOLIN PANDA
APT20 has been linked to a series of sophisticated watering hole attacks that represent an evolution in APT tactics. Unlike many APT campaigns that heavily rely on spear phishing, APT20 is known for compromising legitimate websites frequently visited by their intended targets. This approach involves installing malware on popular websites, increasing the likelihood of infecting visitors.
The group has demonstrated a particular focus on specific communities, including the targeting of Uyghur websites, indicating interest in particular regions and demographics. APT20's preference for watering hole attacks showcases the evolving nature of initial access techniques in the APT landscape, where attackers continuously adapt their methods to improve success rates.
APT18 (Wekby)
Attributed to Chinese state-sponsored actors, APT18 (Wekby) has been involved in cyber-espionage campaigns targeting organizations in the United States and other countries. APT18 is known for leveraging various attack vectors, including spear-phishing and the exploitation of software vulnerabilities. This group focuses on stealing intellectual property and sensitive data for strategic and economic purposes.
APT43 (Mandiant)
Tracked by Mandiant since 2018, APT43 is a North Korean-sponsored threat group with collection priorities aligned with North Korea's Reconnaissance General Bureau (RGB), the country's primary foreign intelligence service. What makes APT43 particularly interesting is its dual mission of conducting both espionage and cybercrime activities.
Unlike many state-sponsored groups, APT43 actively engages in cybercrime operations, including cryptocurrency theft and laundering. This activity appears designed to fund operational infrastructure while reducing fiscal pressure on the North Korean central government, which faces international sanctions.
Key characteristics of APT43 include:
- Regional Focus: Primary targeting of South Korea, Japan, Europe, and the United States
- Health Sector Interest: Notable shift to health-related targets in 2021, likely supporting pandemic response efforts
- Social Engineering: Creation of sophisticated spoofed personas for targeted operations
- Cryptocurrency Operations: Specialized in cryptocurrency theft and laundering through various services
- Collaboration: Evidence of coordination with other North Korean cyber operators
According to Mandiant's analysis, APT43's focus on foreign policy and nuclear security issues directly supports North Korea's strategic and nuclear ambitions, while its adaptability demonstrates the regime's ability to rapidly shift priorities based on changing national needs.
APT Defense Strategies
Defending against Advanced Persistent Threats requires a comprehensive, multi-layered security approach. While no strategy can guarantee prevention of every sophisticated intrusion, implementing appropriate controls can significantly constrain even the most determined attackers. The following sections outline critical defense strategies against APTs.
Mitigating the Human Factor
Human error remains a significant security vulnerability that cannot be completely eliminated. According to Microsoft Security, while cybersecurity awareness training is essential, it must be complemented by defensive measures that minimize potential damage resulting from inevitable human mistakes.
- Email Security Education: Train employees to recognize social engineering attempts, phishing emails, and suspicious attachments
- Macro and Script Controls: Restrict execution of MS Office macros and Visual Basic scripts without administrator approval
- Application Management: Implement regular patching cycles, control application installation, and monitor information-gathering software
- Network Segmentation: Isolate critical systems and sensitive data to contain potential breaches
- Principle of Least Privilege: Limit user and system privileges to only what's necessary for job functions
- Multi-Factor Authentication: Require additional verification beyond passwords for access to sensitive systems
Technical Countermeasures Against APTs
Beyond human-centered strategies, several technical measures specifically target APT tactics, techniques, and procedures:
Application Whitelisting
Implementing application whitelisting can prevent unauthorized programs from executing within your environment. This control restricts execution to only approved applications, significantly limiting an attacker's ability to deploy and run malicious tools.
Network Access Controls
Network access controls limit connections to authorized IP addresses and services. Consider implementing:
- IP Whitelisting: Granting access only to designated IP addresses within the corporate network
- Zero Trust Architecture: Requiring verification for all access requests, regardless of source
- Micro-segmentation: Creating secure zones in data centers and cloud environments
Advanced Monitoring and Detection
Implement comprehensive monitoring systems capable of identifying anomalous behavior:
- Traffic Analysis: Monitor network traffic for unusual patterns or destinations
- Web Application Firewalls: Protect vulnerable servers from SQL injection and other web-based attacks
- Endpoint Detection and Response (EDR): Deploy solutions that monitor endpoint activities for suspicious behaviors
- Security Information and Event Management (SIEM): Collect and analyze security data across your environment
- User and Entity Behavior Analytics (UEBA): Establish baselines of normal behavior to identify anomalies
By combining these human-centered and technical strategies, organizations can build a robust defense against advanced persistent threats, even if they cannot eliminate the risk entirely. Remember that defense against APTs is not a one-time implementation but rather an ongoing process requiring continuous assessment, improvement, and adaptation to evolving threats.
Frequently Asked Questions
- Web application vulnerabilities and watering hole attacks
- Zero-day exploits against unpatched systems
- Insider threats and credential compromise
- Cloud misconfiguration exploitation
- Trusted relationship abuse (third-party access)
- Social engineering beyond email (voice phishing, physical access)
