How to Remove Trojan:Win32/Agent from Windows 11
If you're seeing Trojan:Win32/Agent detected by your antivirus, don't panic. Your computer…
Heuristic Virus Detection: How AI-Powered Security Catches Unknown Threats
Heuristic virus detection is like having a cybersecurity detective who can spot…
Odyssey Stealer: Russian ‘Love Trump’ Malware Replaces Ledger Live Crypto Wallet App
A new macOS malware campaign is targeting users through social engineering, masquerading…
Noodlophile Stealer: Cybercriminals Hijack AI Hype to Steal Your Data
Just when you thought cybercriminals couldn't get more creative, they've found a…
Octalyn Stealer: How This Threat Steals Passwords, Crypto & Browser Data
Octalyn Stealer is an information-stealing malware that's currently being promoted on GitHub…
MaksStealer (MaxCoffe): The Minecraft Mod That’s Actually Stealing Your Passwords
For Minecraft Gamers: MaxCoffe masquerading as a Minecraft performance enhancer! MaksStealer is…
Almoristics Application: What It Is & How to Remove Virus Miner
Almoristics Application is a devious crypto miner that's causing headaches for countless…
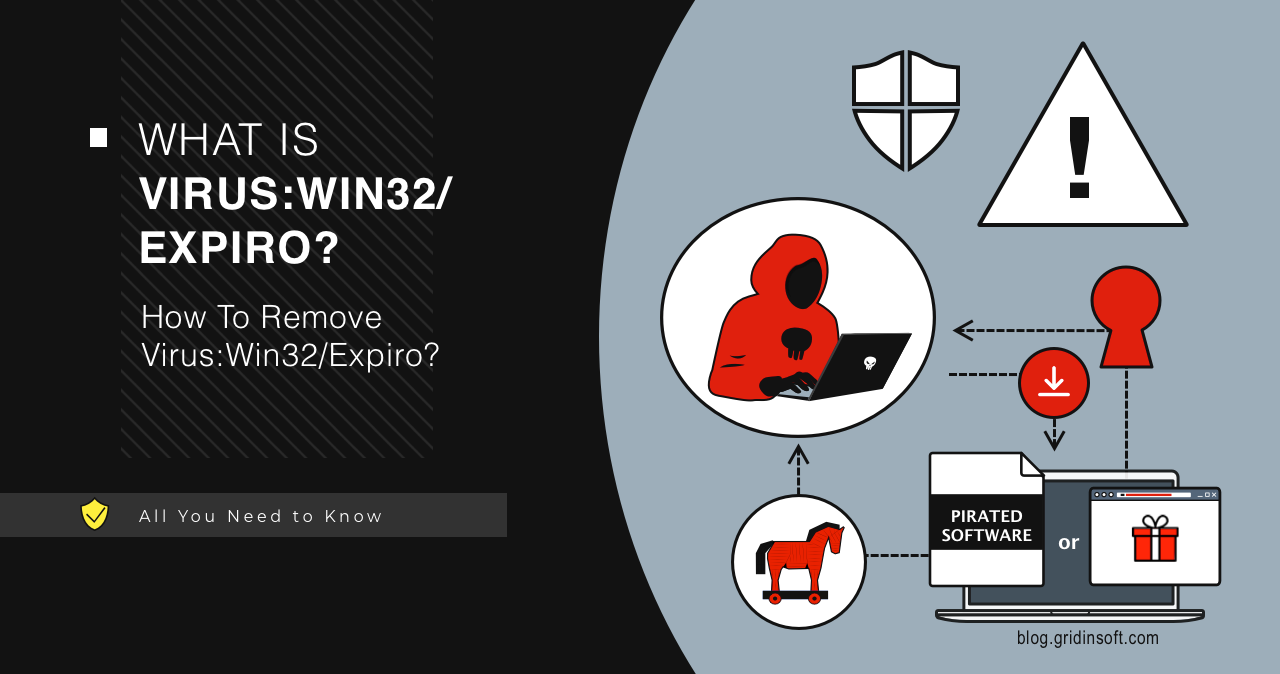
Virus:Win32/Expiro: The Chameleon Backdoor That’s Still Causing Havoc in 2025
Have you ever noticed your computer suddenly running like it's wading through…
How to Remove Trojan:Win32/Yomal!rfn from Windows 11
If you're seeing Trojan:Win32/Yomal!rfn detected by your antivirus, don't panic - but…
Trojan:Win32/Wacatac Removal Guide for Windows 10/11
I think Trojan:Win32/Wacatac, one of the nastiest pieces of malware I've encountered…
Moscovium Ransomware
Moscovium ransomware is a malicious program that locks files on a victim's…
StilachiRAT: The Emerging Crypto-Stealing Malware Threat
$34.6 million in cryptocurrency could be at risk from StilachiRAT, a complex…