What is a Phishing Attack?
Phishing is a cyber-attack method that introduces malware to a computer via email. Intruders send users emails containing links under various pretexts. After clicking these links, the malware enters your computer. Thus, cybercriminals deceive the target to get as much data about the user as possible: his card numbers, bank accounts, etc
Types of Phishing Attacks
We have already explored what phishing is and how it manifests itself. Now, let’s delve into the types of phishing so you can better recognize them, understand where they might appear, and grasp their potential dangers to your PC. See the detailed descriptions below:
- Email Phishing: This is the most common form of phishing. Fraudsters send fraudulent emails that seem to come from reputable sources, such as financial institutions or well-known companies, to steal sensitive information like login credentials or credit card numbers. The emails often contain a link that leads to a fake website designed to capture your personal information.
- Phone Phishing: Also known as voice phishing or vishing, this technique involves phone calls to users with the aim of tricking them into divulging personal, financial, or security information. Attackers might impersonate bank officials, tech support, or representatives from other organizations to obtain sensitive information directly over the phone.
- Clone Phishing: In clone phishing, attackers make a copy or “clone” of a previously delivered email from a trusted sender that contained a link or an attachment. The malicious actor changes the link or attached file to a malicious version and resends it under the guise of an update or correction of the original email, often claiming it was re-sent due to a mistake or problem with the previous link.
- Spear Phishing: Unlike the broad nature of standard phishing, spear phishing targets specific individuals or organizations. This type of attack involves personalized messages that are more convincing because they are often based on the victim’s job position, work relationships, or personal interests, gathered from various data sources like social media or compromised accounts.
- Angler Phishing: This type of phishing exploits social media platforms to masquerade as customer support accounts. Fraudsters create fake accounts or hack into existing ones to respond to genuine customer queries. Through this method, they aim to extract personal data or spread malware by encouraging the victim to click on malicious links or give up sensitive information under the pretense of resolving a support issue.
- Smishing and Vishing: Smishing is phishing via SMS messages, where attackers send text messages that lure recipients into revealing personal information or downloading malware. Vishing, as mentioned, is similar but conducted over the phone. Both methods use social engineering to convince the victim to act against their best interests, often creating a sense of urgency or fear.

Examples of Phishing Attacks
Above, we have reviewed the types of phishing. Consider now the examples of how these types of phishing appear in action:
- You receive a letter that will convince you only to click the link in this letter.
- The most common phrase in these emails is “Click here”.
- Emails that come alert that your payment is allegedly not passed, try again, and so on.
- The letter in which you are deceived as if you have not paid taxes and something should.
- The user can go to the fraudsters’ website, although initially entering the address of the bank.
- Replace DNS routers without user permission.
What is Spoofing Attacks?
Spoofing is the substitution of foreign data by a cybercriminal by falsification to use it for their evil intentions unlawfully. It is often done to bypass the control and security system and distribute malware. The most common types of spoofing are IP spoofing, DNS spoofing, and email spoofing.
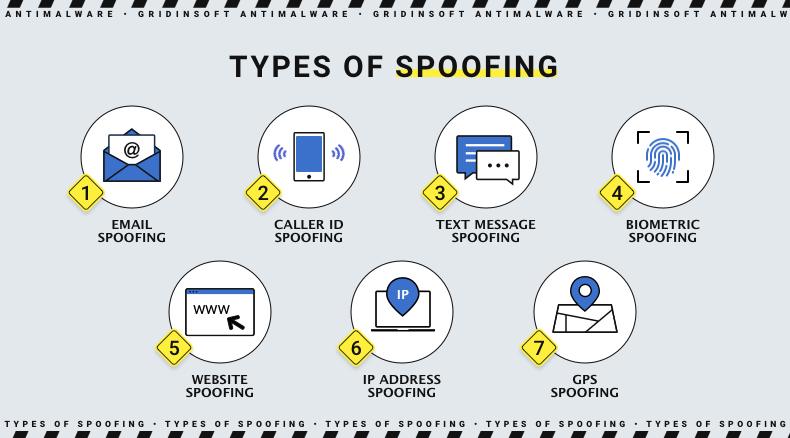
Types of Spoofing Attack
- Email Spoofing. This method involves deception and the forgery of the sender’s address in the letters. This is what the attacker does as a way to spoof the domain, change the sender address, and change the value of the fields “From” and “Reply to”
- Website Spoofing. The attacker creates a fake site that masquerades as legitimate. For the visibility of a realistic site, intruders use legal logos, colors, and fonts. The purpose of this method is to install malware on your computer through such a site.
- Caller ID Spoofing. In this case, the attacker is hiding under a fake phone number. Any outgoing call number is used, but the incoming one will be the one that the intruder wants. That is, it will be difficult to identify the attacker, as he hides his outgoing number.
- IP Spoofing. It is the renumbering IP addresses in packets sent to the attacking server. The sending packet specifies the address that the recipient trusts. As a result, the victim receives the data that the hacker needs. You can completely exclude IP spoofing by comparing the sender’s MAC and IP addresses. However, this type of spoofing can be helpful. For example, hundreds of virtual users with false IP addresses were created to test resource performance.
- DNS Server Spoofing. One way to crack something is to attack by replacing DNS domain names to replace the IP address. DNS (Domain Name Server) spoofing or DNS cache poisoning is a type of cyberattack used by an attacker to direct the victim’s traffic to a malicious website (instead of a legitimate IP address).
Examples of Spoofing Attacks
Each type of spoofing can manifest itself differently. However, for you to understand the general picture of how spoofing works, below we will look at some examples:
- In one case, spoofing is manifested by changing the IP address when the entire site is hacked.
- It may be a website disguised as a bank you know that asks you to log in and sends you a link, but it’s just a scam to get your confidential information.
Difference Between Phishing and Spoofing
Now that we know what phishing and spoofing are, we know of the species and how they manifest themselves in practice, then we can consider what the difference between them is:
- Objective: The purpose of spoofing and phishing is different. The purpose of phishing is to get information about the user. The goal of spoofing is identity theft.
- Nature of Scam: In the case of spoofing – it seems completely harmless and not even fraudsters. It does not extort email addresses or mobile numbers. But phishing is a scam because it steals users’ data.
- Subset: Phishing and spoofing have nothing to do with each other. But there is a similarity. The similarity is that spoofing steals an identity from the Internet before committing fraud.
- Method: The primary spoofing method is the use of malware when phishing uses social engineering.
How to Prevent Phishing and Spoofing Attacks
Of course, there are methods to avoid an attack from the side of spoofing and phishing attacks . Of course, you cannot do anything because you will hurt yourself, but we recommend you take some measures. See below:
Phishing:
Before clicking on the proposed link in the email, move your mouse over it and look at the address you will go to. It should be the same as you were given. If it is different – it is likely to be a hoax. If you receive messages with such a logo – “Do not hesitate”, “Last Chance”, “Hurry”, and the like, then delete them or send them to spam. They pressure you to make a quick decision and immediately click on the link. Open any attachment only through proven and reliable sources. If you have received an email from a particular user, but you are not sure it will be sent to you, you better call him.
Spoofing:
- Check the letter for grammatical and spelling errors.
- Look carefully at the sender’s address
- Encryption and authentication
- Robust verification methods
- Firewall (protects your network, filters traffic with fake IP addresses, blocks access of unauthorized strangers).
You can also apply the same tips that we have considered to prevent phishing. It would help if you were careful in all these aspects. You do not know what you will be exposed to. Put protection on your PC, which will work for your benefit, warn you about perceived threats, and will closely monitor all your online activities.
We invite you to try Gridinsoft Anti-Malware, it is an excellent protection against spoofing, phishing attacks, and other online threats. Moreover, it is also able to get rid of the virus that helps scammers to deceive you.





