
MedusaLocker Ransomware
At the first sight, MedusaLocker ransomware does not look like something new compared to other ransomware groups. It has a pretty similar behaviour, uses the same distribution channels, and makes almost the same steps after being injected into the corporate network. However, if you check it more closely, you will see that MedusaLocker has a lot of tricks which are contrasting with other ransomware families.
The distribution methods are pretty typical for the majority of corporate-oriented ransomware - email spamming and exploit usage. First one is used the most often, since it has the biggest chance of success. Further steps, however, are contrasting to ones used by other malware. MedusaLocker uses PowerShell vulnerabilities to launch its malicious code, but not in a straight way. With the batch file it contains inside of its payload, this ransomware creates a separate Windows service, and adds certain registry keys to allow running this service in the Safe mode.
After the successful execution of the trick with a batch file and service, MedusaLocker reboots the PC into the safe mode, before taking any data ciphering actions. This step allows the virus to prevent the anti-malware software detection before the ciphering starts. When this action is completed, MedusaLocker goes to the ciphering.
In the case when the user account MedusaLocker ransomware has infected does not have the administrator rights, the virus exploits another security breach - privileges escalation. This trick is done by the additional malware inside of the MedusaLocker virus - TrickBot trojan. This action allows the ransomware to use the administrator permissions and avoid the UAC even on the accounts that are not granted with administrator privileges.
MedusaLocker uses mixed encryption - AES-256+RSA-2048. There is no need to use such a hard cipher, so it is rather a scary factor that forces some users to pay. Just like any other ransomware family, it keeps the decryption keys on the remote server, so there is no way to get it without the payment. However, the target of encryption is quite new - MedusaLocker attempts to cipher all available shared directories, so even the computers that were not under attack can get their files encrypted. The additional extensions this ransomware family adds after the encryption are .encrypted, .bomber, .boroff, .breakingbad, .locker16, .newlock, .nlocker, and .skynet.
Technical details
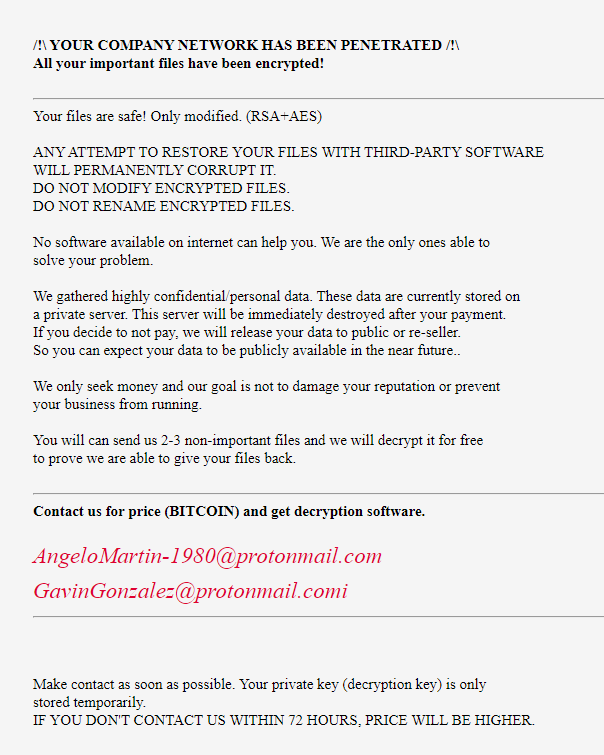
| Note | .hta file with a random name. Contains the information about the fact that your corporate network was attacked. Has a notice that using the third-party software may damage your files. There is also a ransom escalation note in case you don’t pay the initial sum during the first 72 hours after the attack. |
| File pattern | %filename% . %original_extension% . %ransomware_extension% |
| Algorithm | AES+RSA |
| Features | Uses PowerShell vulnerabilities to make itself more sustainable |
| Damage | Deletes backups created with Windows functionality, Volume Shadow Copies, suspends Microsoft Defender |
| Distribution | Email spamming, various vulnerabilities exploiting |
Ransom note of MedusaLocker is next:
Similar to different other ransomware families, MedusaLocker disables all Windows-based recovery options. Backups created with Windows embedded functionality, Volume Shadow Copies and Windows Updates are deleted. Updates are dangerous for this virus, because each major update can turn the Microsoft Defender back, as well as delete the registry entries this malware uses to provide itself the persistent activity.
Fake claims
Some of the corporations who were attacked by MedusaLocker reported that they were charged with an additional ransom, “to keep their corporate data from leaking”. However, despite the fact that those companies refused to pay the additional sum for their data, no leaks were discovered in visible channels. There is no guarantee that fraudsters did not sell this information through the offline channels, but, again - the companies had no impact on their business or other activities.
