
Avaddon Ransomware
At the moment of its launch, Avaddon chose a new (for that time) model of action - so-called ransomware-as-a-service (RaaS). This model is aimed primarily at corporations since it supposes a pretty big ransom amount, as well as data stealing. However, key features of the RaaS model are other - ransomware is spread not directly by its developers, but by the affiliated persons, who have a certain commission for each successful injection.
Such a form not only increases the efficiency of ransomware injection but also makes the cyber police work harder. When there are a lot of distributors who have no relation to the originator of the virus, it is pretty hard to reach the top of this scheme. Even if the FBI or any other executive authority catches a lot of ransomware distributors, the developers of that malware have a lot of time to remove all proofs of their activity. However, Avaddon used the RaaS model, not from the start - it applied such a distribution scheme only in June 2020.
| Note | readme.html, readme.txt |
| File pattern | .avdn or random 10-characters like AbC23deF14 |
| Encryption algorithm | AES-256 |
| Features | One of the first “old” ransomware families who applied RaaS model. Attacked several world-known companies. |
| Ransom amount | $500, $1000 in Bitcoins |
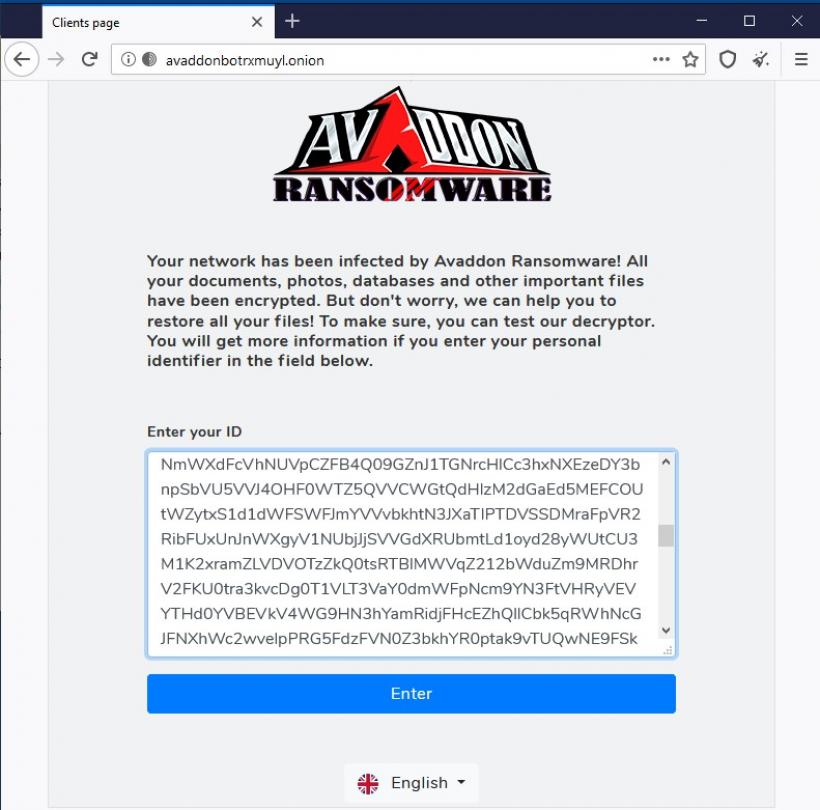
| Contact | avaddonbotrxmuyl.onion |
| Damage |
|
| Distribution | Email spam, RDP vulnerabilities exploiting |
| Facts | Does not encrypt files on the systems with a Russian default locale. |
Decryption service:
Injection
The actual way of injection and infecting the corporation has some details in common with other families. Like several other ransomware variants, that aim at large corporations, it is spread through malicious email spam and phishing. It is contrasting with Dharma ransomware - another example of the corporation-oriented virus, that is spread “manually” - through the vulnerability of RDP ports.
Avaddon ransomware also carries several other viruses - spyware and hacktool - to get some valuable information from the hacked corporation network. Then, cybercriminals begin to extort money not only for files decryption but also for keeping the corporate data unpublished. The total ransom amount reaches an average of $40,000. As practice shows, companies usually pay the offered sum to keep their secrets.
The encryption algorithm used by Avaddon ransomware is AES-256. This cipher is pretty strong to avoid hacking it in a regular way, but ransomware also manages to keep the decryption key on the remote server
Encryption
The encryption process has six steps:
- Imports hardcoded master public RSA-2048 and master AES-CBC-256 keys.
- Generates a session AES-CBC-256 key.
- Adds IV to the master AES-CBC-256 key.
- Uses the master AES-CBC-256 key to encrypt the data about the user with Base64 encoding and adds to the ransom note.
- Encrypts the user’s files with the generated session AES-CBC-256 key.
- Adds the session AES-CBC-256 key encrypted with RSA-2048 key to the end of every encrypted file.
- The public master RSA-2048 and AES-CBC-256 keys are hardcoded.
Avaddon ignores some important Windows folders during the encryption process:
C:\Perflogs
System volume information
C:\Users\Public
C:\Users\{User}\AppData\Local\Temp
C:\Program Files (x86)
C:\Users\{User}\AppData
C:\ProgramData
C:\Windows
However, the ransomware is determined to encrypt Exchange and SQL servers, so it doesn’t skip the next paths:
C:\Program Files\Microsoft\Exchange Server
C:\Program Files (x86)\Microsoft\Exchange Server
C:\Program Files\Microsoft SQL Server
C:\Program Files (x86)\Microsoft SQL Server
Avaddon also skips files with the following extensions:
exe, bin, sys, ini, dll, dat, drv, rdp, prf, swp, lnk.
Interesting facts about Avaddon
An interesting element that says a lot about the origins of that ransomware is the fact that Avaddon ransomware will not work in the system which has one of the languages from the Commonwealth of Independent Countries. This formation consists of ex-USSR countries, so it is quite easy to suppose that Avaddon is created somewhere in these countries. As soon as ransomware detects that the PC has a Ukrainian keyboard layout, for example, it stops the actions and removes itself completely from the victim’s PC, leaving no footprints of its activity.
One of the most wide-known cases of Avaddon attacks is a cyberattack on French insurance company AXA. Asian Assistance division of the company and its IT Operations department in Thailand, Hong Kong, the Philippines, and Malaysia was under attack. As fraudsters report in their money ransom note, they have stolen over 3TB of confidential data, related to the customers’ medical information - illnesses, pathologies, and various other sensitive things.
As the FBI states in their report, some of the victims who decided to pay the ransom have never got the decryption keys. Such a fraud (non-sending the decryption keys even after the payment) is not something new among ransomware - but the ransom amounts of Avaddon are much bigger.
Shutdown in May 2021
After almost 1,5 years of successful activity, being considered as one of the most prolific ransomware groups, Avaddon developers decided to… shutdown their activity. The true motives of their decision remain uncovered, but the background at the timeline gives several tips. Just a week before, another group of pretty successful crooks - DarkSide ransomware - claimed that they have lost access to their servers and were forced to shutdown their activity.
This happened just after the extremely loud cyberattack on the Colonial Pipeline, that led to the massive shutdown of gas stations in various states of the U.S. East Coast. In some moments, almost 20% of gas stations were shut down because of fuel shortages. However, there are no facts that the Avaddon shutdown is somehow related to DarkSide’s one - only guesswork.
At the moment of shutting down, Avaddon developers released the decryption keys for almost 3000 victims who did not purchase the keys earlier. This number wonders because only 88 companies have reported the Avaddon attack, and most of them were solved to the moment of the shutdown. Now, imagine, how many companies decided to conceal the fact of a ransomware attack and did not report it to law enforcements?
More about Avaddon ransomware:
| 🔗 Three major hack forums banned advertising of ransomware |
| 🔗 Spanish student created free decryptor for Avaddon |
| 🔗 Avaddon ransomware group closes shop, share all 2,934 decryption keys. |
