News, Tips, Security Lab
Over 100k ChatGPT Accounts Are For Sale on the Darknet
According to a new report, over the past year, over 100k ChatGPT users’ accounts have been compromised using malware to…
How Can Companies Be Secure Against Cyberattacks?
Organizations face an alarming reality in the digital world: data breaches and cyberattacks are becoming more frequent. Cybercriminals find more…
APT28 Attacked Ukrainian and Polish Organizations
Recorded Future, in collaboration with CERT-UA researchers, has unveiled a recent cyber offensive orchestrated by Russian-speaking hackers affiliated with the…
Freaky Leaky SMS: Message Delivery Report Can Be Used to Determine the Location of the Recipient
Researchers have created a side-channel attack called “Freaky Leaky SMS”, which allows finding out the location of the recipient of…
Malware Propagation On Darknet Forums
The forums on the dark web are well-known for being a hub of cybercriminal activity, including an auction system. Here,…
Information Security Experts Told About The Linux Malware Symbiote That Is Almost Undetectable
BlackBerry and Intezer specialists spoke about the new Symbiote Linux malware that infects all running processes on compromised systems, steals credentials and provides backdoor access to its operators. Let me…
Joint Operation: SSNDOB Personal Data Darknet Market Seized
What SSNDOB Was Before Its Servers Were Seized The US Department of Justice, Internal Revenue Service, and Federal Bureau of Investigation have joined forces with law enforcement authorities in Latvia…
Beware: New SpaceX Bitcoin Giveaway Scam
Crooks Make Elon Musk a Bait for Wannabe Cryptotraders Scammers again use SpaceX as a bait in fraudulent schemes. The statements of Elon Musk, CEO of the company, have been…
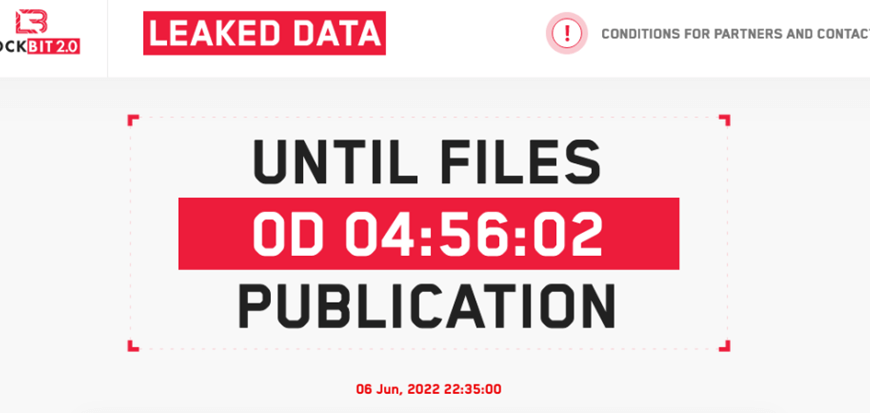
LockBit 2.0 Promises to Leak Mandiant Data
LockBit 2.0 announcement: real thing or vengeful trolling? On June 6, on its portal on the dark web, LockBit 2.0, a ransomware operator, has announced the exposure of data allegedly…
Microsoft Is in No Hurry to Fix the Follina Vulnerability, Which Has Become a Real Disaster
Hackers are actively exploiting the critical 0-day Follina vulnerability, which Microsoft is in no hurry to fix. Researchers warn that European governments and municipalities in the US have been targeted…
Top Types of Spoofing Attacks
Spoofing 1 is a kind of cybercrime in which attackers…
Facts to Remember About Trojan Malware
In this article, we will consider one of the vilest, most unpleasant, seemingly harmless, malware. We will present you here all about Trojan2 A Trojan virus is a type of…
Attackers Exploit MSDT Follina Bug to Drop RAT
Security specialists caution users about the exploitation of the recently disclosed Follina Bug found in all supported versions of Windows. Threat actors have actively utilized this vulnerability to install payloads…
New Cuba Ransomware Variant Involves Double-Extortion Scheme
What’s new in April Variant of Cuba Ransomware The Cuba ransomware family has got itself a new specimen. The new version of Cuba revealed itself in late April 2022 and…
The Heuristic Virus & Analysis: Everything You Need To Know
This article targets individuals who have received a computer notification indicating the presence of a heuristic virus in their system. What exactly is this “heuristic virus”, and is it a…
Evil Corp Switched to Using LockBit Malware to Avoid Sanctions
The Evil Corp group switched to using the LockBit ransomware to avoid sanctions imposed earlier by the Office of Foreign Assets Control of the US Department of the Treasury (OFAC).…
Warning Signs Of DDoS Attack: Symptoms
DDoS attacks can sometimes have devastating effects on various internet users. This particular type of cyber threat can put on hold different internal operations, create negative relationships with customers, and…