Today there is an arms race between cybercriminals and antimalware manufacturers. While some release a fix for an existing threat, others must develop new loopholes. Recently, cybersecurity experts noticed that many malware families were using OneNote attachments to infect their victims. Since OneNote is considered a robust application that Microsoft has developed for easy note-taking, hackers couldn’t help but take advantage of it for their nefarious purposes. Next, we will look at some relatively new ways of spreading the known Qakbot banking Trojan.
What is Qbot?
Before moving on to distribution methods, let’s recap QakBot. Qakbot Malware (QuakBot, or QBot) is a banking Trojan designed to steal confidential information from Windows computers. For starters, it is worth mentioning that this type of malware is nothing new, and it appeared in 2007. Since then, it has undergone many changes, primarily aimed at bypassing security features. What has stayed the same, however, is the distribution method. For the most part, it’s email spam. However, after infecting one machine, QakBot can spread to other devices on the network.
Furthermore, it has modular protection. Hence, the operator can fully customize it according to the objectives. For example, it can be network reconnaissance, keylogging, credential theft, botnet deployment, or ransomware. In some cases, botnets under the rule of QakBot were delivering CobaltStrike beacons.
Distribution using OneNote Using Batch & PowerShell
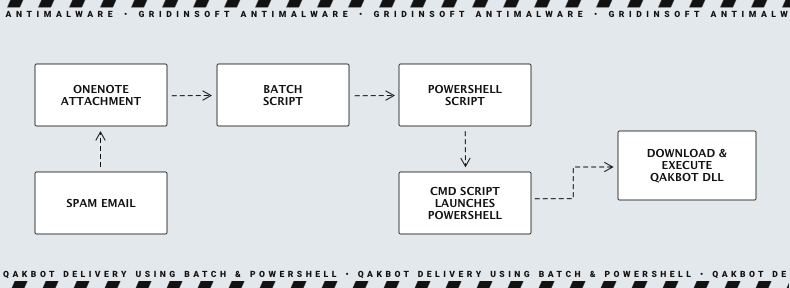
The primary method of spreading Qakbot is through e-mail spamming. Previously, a rogue email contained an MS Office file with a malicious macro hidden inside. However, after Microsoft forcibly disabled the execution of any macros coming from the Internet, Qakbot started attaching the OneNote attachment. Usually, such an email contains something like “RE: DRCP Hire-Success Story…” and attachments are usually masked as legitimate files and named, for example, “Contracts – Copy.one”.
A fake cloud attachment page opens when the victim opens the OneNote attachment. This is done to get the victim to click on the BAT file (let’s call it Open.bat) that is embedded in Contracts – Copy.one. A PowerShell script is started as soon as the user runs this file, which in turn puts a CMD file with the conditional name “i.cmd” into the %temp% folder and runs it. This action is performed in a mode hidden from the user and not displaying any notifications. It then uses a PowerShell script to download a GIF file using the Invoke-Webrequest command. Although this file is saved as a JPG file in %programdata%, it has nothing to do with image files. Instead, it is an executable Qakbot DLL file that Rundll32.exe runs with the “Wind” parameter.
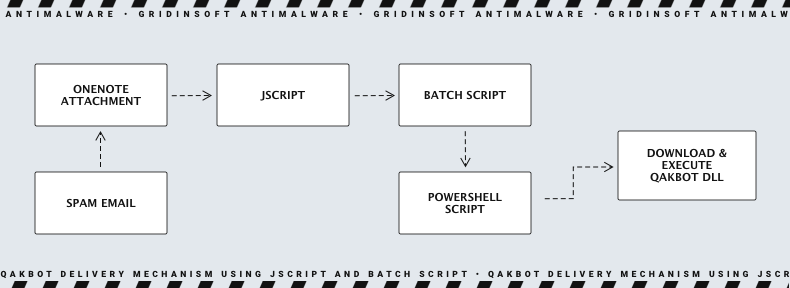
Distribution Via OneNote Using Jscript (.jse) file
Similarly to the previous point, the initial stage of the infection process occurs via phishing emails, which also contain a OneNote attachment. However, unlike the last end, this attachment includes a JSE file. This file also contains a hidden Bat file, usually disguised as an “Open” button. After the user clicks this button, the batch file is launched. PowerShell script downloads the pseudo-gif file into a Temp system folder. This file is also different from what it looks like. It is an executable Qakbot DLL file which performs the routine unfolding process, same as in any other case scenario.
Distribution using html Application (.hta) file
At the end of January 2023, Qakbot operators began experimenting with this new distribution method. It is identical to the previous way, except that instead of a JSE file, OneNote files contain an embedded HTML application (HTA file). When the user clicks “open” on the OneNote page, it drops an embedded .hta file executed by mshta.exe in the background. The script in the HTA file uses the legitimate curl.exe application to load the Qakbot DLL file into the C:\ProgramData folder and then run it. The Qakbot payload is injected into the Windows Auxiliary Technology Manager “AtBroker.exe” to hide its presence.
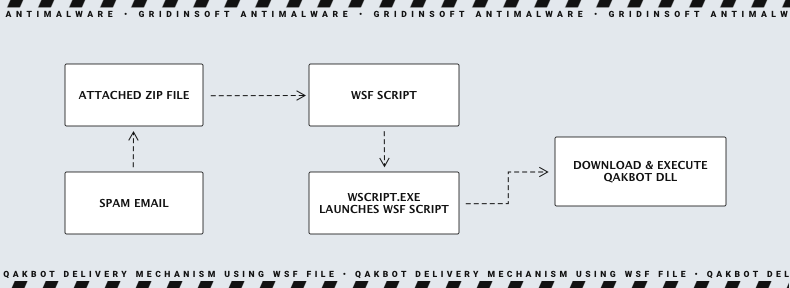
Distribution using Windows Script (.wsf) Files
In this case, the phishing email contains an attachment in the form of a zip file with a random name, e.g., “Shared Document From Cloud 540318.zip”. There may be several files in the archive, including a wsf file. This file contains malicious JScript between digital certificates. Hence when a victim tries to open the .wsf file, it will run code to download the Qakbot DLL file. Usually, it is loaded in the C:\ProgramData directory and run using “Rundll32.exe” with the parameter “Wind”.
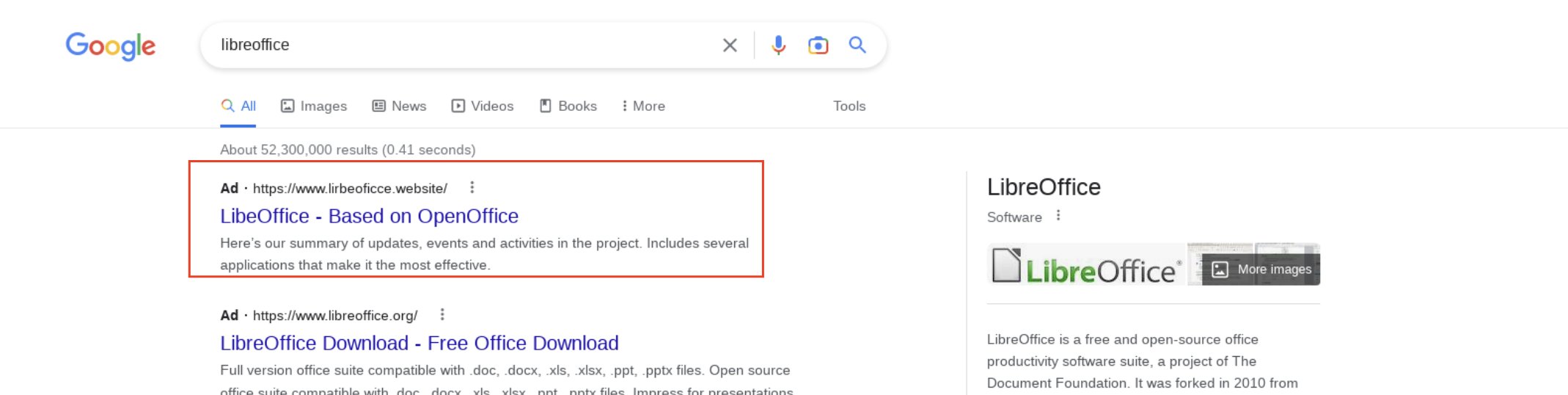
Distribution using Google Ads
Since Microsoft, by default, blocks macros execution in Office files downloaded from the Internet, attackers are finding ever more sophisticated ways to distribute malware. Thus lately, there has been a significant surge in malicious ads that lead to a fake page of a legitimate program. Thus lately, there has been a significant surge in malicious advertising, which leads to a fake page of a legitimate program. However, instead of the legitimate program, the user receives malware. It may usually be a .exe or .msi file, which contains malware and many empty sections to avoid detection by anti-malware engine, as it overwhelms their file size limit.
How to avoid Qakbot Malware infection
To minimize the risk of Qakbot Malware infection, we recommend following cyber hygiene practices and the recommendations below:
- Be careful when dealing with email. Please do not open emails from unknown or unverified senders.
- Avoid downloading pirated software from unverified sites like Torrent/Warez. Most often, pirated software contains unpleasant bonuses in the form of Trojans or ransomware.
- Use strong passwords, update them regularly, and use multifactor authentication wherever possible. Passwords that are too easy can be compromised by brute force. Multifactor authentication can protect passwords if data breaches have compromised them.
- Use a strong security solution on all devices, including PCs, laptops, and mobile devices.
- Include data loss prevention (DLP) solutions on employee systems.
Conclusion
The Qakbot malware provides a prime example of how the threat landscape is changing. Its complex structure, impact, and distribution underscore the importance of maintaining cybersecurity vigilance. Moreover, as discussed at the outset, attackers using Qakbot consistently adapt their methods, using innovative attack vectors such as OneNote and Google Ads attachments to avoid detection, reinforcing the need for proactive and robust security measures.




