The Security Blog From Gridinsoft
Attackers Can Use GitHub Codespaces to Host and Deliver Malware
Trend Micro reports that the GitHub Codespaces cloud development environment, available to the public use since November 2022, can be…
Google Search Malvertising: Fake Ads of Free Programs in Google Ads
Google Search malvertising is an unpleasant phenomenon of malicious advertisements in search engine results. Ads up there are called to…
Russian Cybercriminals Seek Access to OpenAI ChatGPT
Check Point analysts have noticed that Russian-speaking hacker forums are actively discussing access to bypass geo-blocking, due to which the…
Goose Goose Duck Game Servers Are DDoS-Attacked Every Day
The free social detective Goose Goose Duck, which recently broke the Among Us record for the number of users simultaneously…
Exploits for Vulnerabilities in Three Popular WordPress Plugins Appeared on the Network
Three popular WordPress plugins, with tens of thousands of active installations, at once turned out to have critical SQL injection…
Operators of phishing campaigns increased number of emails allegedly from delivery services
Check Point Research reports that in November, the number of phishing emails written on behalf of delivery services increased by 440% compared to October. The sharpest growth was noted in…
Linus Torvalds doubts that Linux will run on Apple M1
Recently on the Real World Technologies forum Linus Torvalds was asked what he thinks of Apple’s new M1 laptops. Torvalds then vague replied, “I would love to have this [laptop]…
Apocalypse Now: experts presented a new type of cyber-biological attack
On Monday, November 30, specialists from the Ben-Gurion University of Negev (Israel) presented a new type of cyber-biological attack that can bring biological warfare to a new level. The attack,…
Hackers create scam e-commerce sites over hacked WordPress sites
Akamai specialist Larry Cashdollar discovered a hacker group that uses hacked WordPress sites in an interesting way. First, hackers run fraudulent online stores over WordPress sites. Second, they poison XML…
Researcher accidentally found 0-day bug in Windows 7 and Windows Server 2008
French cybersecurity researcher Clément Labro was working on a security tool when he discovered that Windows 7 and Windows Server 2008 R2 were vulnerable to a 0-day local privilege escalation…
NATO experimented with deceptive techniques to combat Russian hackers
During a cyber exercise in Estonia on November 16-20, NATO experts experimented with deceptive techniques – they practiced in catching Russian government-funded hackers using specially placed traps. The exercise, coordinated…
The researcher showed how to steal a Tesla Model X in a few minutes
Information security specialist Lennert Wouters from the Catholic University of Leuven showed how to steal a Tesla Model X. He discovered a bug that allowed hacking and changing the firmware…
LidarPhone attack will make your vacuum cleaner spy on you
A group of scientists from the University of Maryland and the National University of Singapore have demonstrated the LidarPhone attack, which can turn a smart vacuum cleaner into a spy…
Cybercriminals started using Google services more often in phishing campaigns
Security researchers have reported an increase in cyberattacks using Google services in phishing campaigns, as a tool to bypass security and steal credentials, credit cards, and other personal information. The…
Though 2020 is ending, the list of worst passwords is still topes “123456”
The end of the year is approaching, and the developers of the password manager NordPass have once again published a list of the most popular and weak passwords of 2020.…
Chrome 87 Fixed NAT Slipstream Vulnerability and Disabled FTP Support
Google engineers introduced Chrome 87, in which was disabled FTP support. The new version of the browser is already available for users of Windows, Mac, Linux, Chrome OS, Android and…
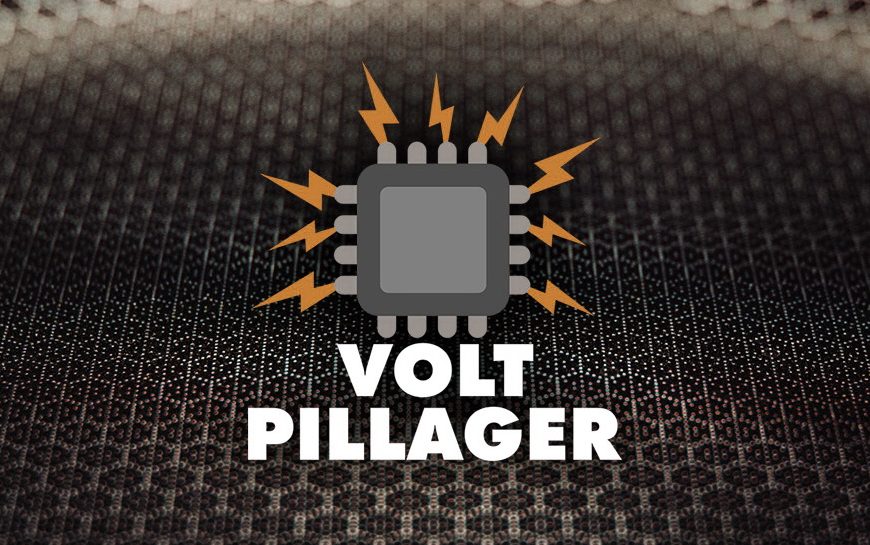
VoltPillager attack compromises Intel SGX
A group of researchers from the University of Birmingham have demonstrated the VoltPillager attack, which can violate the confidentiality and integrity of data in Intel SGX enclaves. To implement this,…