On Monday, November 30, specialists from the Ben-Gurion University of Negev (Israel) presented a new type of cyber-biological attack that can bring biological warfare to a new level.
The attack, presented by the researchers, allows biotechnologists working with DNA to inadvertently create dangerous viruses and toxins.
The researchers described how an attacker can spoof DNA sequencing chains using malware on a biotechnologist’s computer. In particular, vulnerabilities in the Screening Guidelines for Suppliers of Synthetic Double-stranded DNA and Harmonized Screening Protocol 2.0 allow “to bypass the protocols using a common obfuscation procedure.”
According to the US Department of Health and Human Services, specific screening protocols must be followed to identify potentially harmful DNA when sequencing genes during DNA sequencing. However, the researchers were able to bypass these protocols by using obfuscation, as a result of which 16 out of 50 obfuscated DNA samples were not detected using “DNA screening for best match.”
The software used to develop and manage synthetic DNA projects is also vulnerable to man-in-the-browser attacks. With these attacks, attackers can inject arbitrary strands of DNA into gene sequences – what researchers have called an “end-to-end cyber attack.”
To demonstrate the possibility of their attack, the researchers cited a Cas9 protein residue, using malware to convert this sequence into active pathogens.
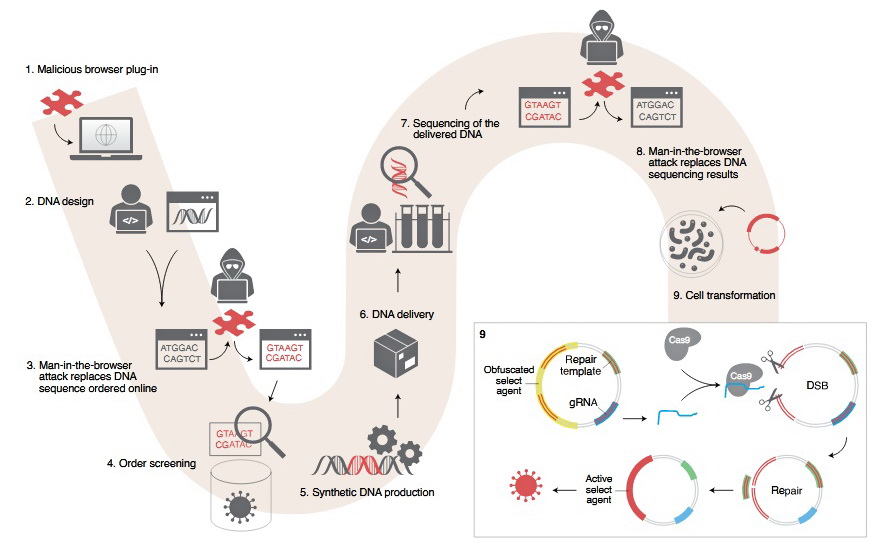
According to the scientists, using the CRISPR protocols, the Cas9 protein can be used to “deobfuscate harmful DNA in host cells.” For the unsuspecting scientist processing the sequence, this could mean the accidental creation of hazardous substances, including synthetic viruses or toxins.
As I mentioned, cybercriminals attacked UCSF, the US leading COVID-19 vaccine developer.