PUA:Win32/Conduit is a potentially unwanted application that performs suspicious activity with the browser. It changes the homepage and search engine and installs extensions. It is distributed through hacked software or under the “recommended software” guise.
PUA:Win32/Conduit Overview
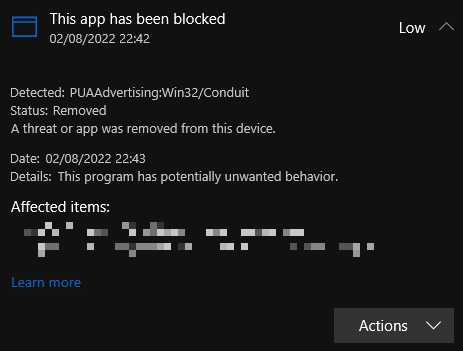
PUA:Win32/Conduit (also goes by PUAAdvertising:Win32/Conduit) is a potentially unwanted application belonging to Conduit Search. One of Conduit’s characteristic features is unwanted activity on the user’s device. It installs additional software and changes current web browser settings without the user’s knowledge, which makes it a typical representative of a browser hijacker. At the same time, it is not easy to remove all this.
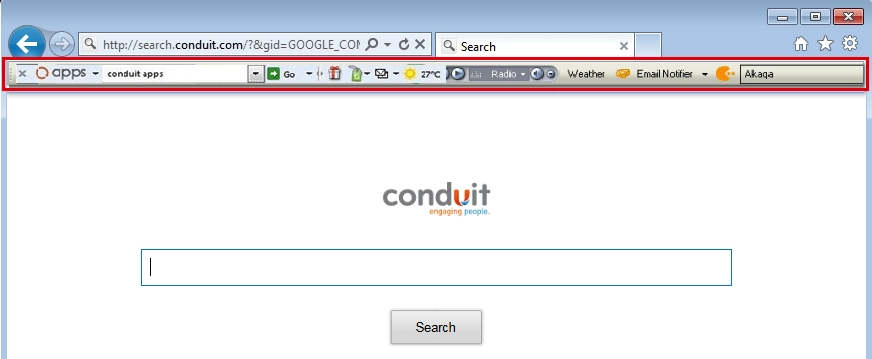
Conduit PUA usually changes the browser’s homepage and search engine to search.conduit[.]com without the user’s consent. It also installs a toolbar in some browsers, which can lead to unsolicited redirects to websites containing adverts or malware. In addition, Conduit often collects information about a user’s online activity, such as the history of websites visited, search queries entered, etc. As a result, this information may be used without the owner’s permission for fraudulent purposes or shared with third parties.
Technical Analysis
Let’s see how this infection behaves, using the example of a sample that masquerades as a ScreenHunter screen capture application.
The malware, represented by %SAMPLEPATH%\19a6fab0b940ce5a1334a9ec80aeae1e1d585a15d9eccc5cbc75ec972edd1269.exe, accepts command line arguments to control its behavior. It links many functions at runtime on Windows: This indicates that the malware dynamically links libraries and functions during runtime, making it harder to detect statically.
Persistence And Privilege Escalation
Next, the malware establishes persistence by creating an undocumented autostart registry key:
HKEY_CURRENT_USER\Software\Wisdom-soft\toolbar
The malware stores files in the Windows startup directory to ensure its execution upon system boot. Attempting to load missing DLLs can be observed, indicating potential evasion techniques or ensuring the malware’s functionality. It dropped the following files to the %USERPROFILE%\AppData\Local\Temp\ folder:
~GLH0002.TMP
GLCAB3D.tmp
GLKAB48.tmp
GLH0007.TMP
GLC46CA.tmp
Conduit creates a process in suspended mode, suggesting code injection techniques for more stealthy execution. This tactic is often used by dropper malware.
Defense Evasion
As for evading detection, it’s standard for unwanted apps – Conduit encodes data using XOR to encode data, potentially to obfuscate its activities and evade detection. It also uses software packing techniques to compress and encrypt its executables, making analysis and detection more difficult.
Unwanted Activity
Installs an Internet Explorer URL search hook. This allows it to monitor and intercept web traffic, potentially capturing user browsing habits or sensitive information. Next, the application installs browser toolbars and helper objects to integrate the malware with the Internet Explorer browser by installing toolbars and browser helper objects. Such modifications can lead to unwanted browser behavior, including redirections, intrusive advertisements, and user data compromise.
Additionally, by modifying registry keys and values that belong to the web browser, Conduit malware adds one more layer of persistence and detection evasion. These tricks allow the unwanted program to keep working even if something deletes the files from autostart values/folders. To achieve this, malicious program plays with the following registry keys:
HKCU\SOFTWARE\MICROSOFT\INTERNET EXPLORER\URLSEARCHHOOKS
HKLM\SOFTWARE\MICROSOFT\INTERNET EXPLORER\TOOLBAR
HKLM\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\BROWSER HELPER OBJECTS
How To Remove PUA:Win32/Conduit?
To remove PUA:Win32/Conduit, it is best to use an advanced solution. GridinSoft Anti-Malware is the best option because, in addition to removing unwanted software, it will reset web browsers in a couple of clicks. Moreover, GridinSoft Anti-Malware will provide your device with proactive protection.





