Oneetx.exe is a malicious process, related to Amadey dropper malware. It can be spectated in the Task Manager, with seemingly nothing suspicious about it – if you don’t know what it stands for. Let me show you how it appears and how you can remove it.
What is Oneetx.exe process?
Oneetx.exe is a disguised name chosen by Amadey dropper developers to hide their malware among other processes. Windows tracks all processes running in the system and displays what it found in Task Manager. Obviously, obfuscated names like sv39103.exe will attract attention and raise suspicion. That is the reason why hackers opt for some ordinary names. Their often choice is system processes or ones related to popular software packages, like Photoshop or crypto mining software. This case, however, is different.
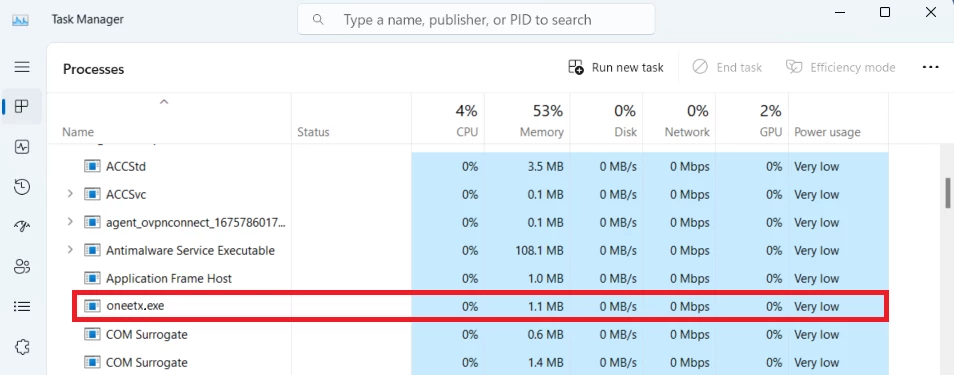
It appears that oneetx.exe does not belong to any program. Moreover, Google contains clear clues that this process belongs to malware that has acted as a backbone of the Russian botnet since 2018. The most obvious guess is, of course, Emotet malware. It is known for having possibly the most extensive networks on the planet. However, in this case, the short research showed the relation of oneetx.exe to the Amadey dropper.
What is Amadey?
Amadey is a dropper (a.k.a downloader) malware, that has only one purpose – deliver other malware to the infected system. It often acts as a precursor, that makes sure the system is not in a banned region and is not a debug environment. It can deliver a wide range of threats – from the aforementioned Emotet to RedLine stealer and even STOP/Djvu ransomware. Even after delivering the payload, it remains active, waiting for other commands from hackers.
Aimed at long-term stay in the system, Amadey does its best in hiding from users and anti-malware software. Choosing an unremarkable name is only a small part of the way it disguises itself. First of all, each of its samples is repacked in a specific way, making it harder for antiviruses to detect. Amadey typically arrives within phishing emails with attached Office documents. Upon execution, malware moves its files from the original directory to the other folder, depending on the antivirus software present in the system. All these actions make it a pretty tough nut for “classic” antiviruses.
IoC Amadey Dropper
- Trojan.Win32.Amadey.tr: 76fb588c54b8aa2ebc269ea3b845a40077f18aef9b071cd4a675b5bacb56e479
- Trojan.Win32.Amadey.tr: 7b4dc90b59760320253596a753556de932a32fd1967726b7321a0095760f7bcf
- Trojan.Win32.Amadey.tr: 6f31b1b2b0f080c1569d5dfb2840244be2c8ef84824b0fecf686c6e42def3aa7
- Trojan.Win32.Amadey.tr: 8dec86d0a0c4034b6d688a0610742694517e0d31939c53db11b898c0ba7315c0
- Trojan.U.Amadey.tr: 2cdda26cc29f1ab91873bf2de8af2627aa7fa73002cb490f2f1ab73ff824ebf8
- Trojan.Win32.Amadey.tr: 4e3b1632008b15ff18717ee30e1209c4328f618232f85db9c1e4a8a418de02d8
- Trojan.Win32.Amadey.tr: 1f435b3a62304733dce1b9caf24cfac768db739127e8ec31d466455628ec0922
- Trojan.Win32.Amadey.tr: 5ec0957697ef3692607bc8a8d00bdad0ff86c129ead5fb698c035f4d6b47c69c
- Trojan.Win32.Amadey.bot: d9131553ec5337523055e425db82038f4250fa60ea581bcc6921716477c652ce
- Trojan.Win32.Amadey.bot: 362d8f8fcc698554a750a5dfb1e261eb3b5442fb4bfe4746c8ba9431ec944305
How to remove Oneetx.exe?
You will likely fail to remove Oneetx.exe from your system manually. It performs a row of actions for persistence provision, which forces the user to locate and remove all the changes it does to the system before touching the files. For that reason, I’d recommend using GridinSoft Anti-Malware – a program that specialises in removing threats like Amadey dropper.

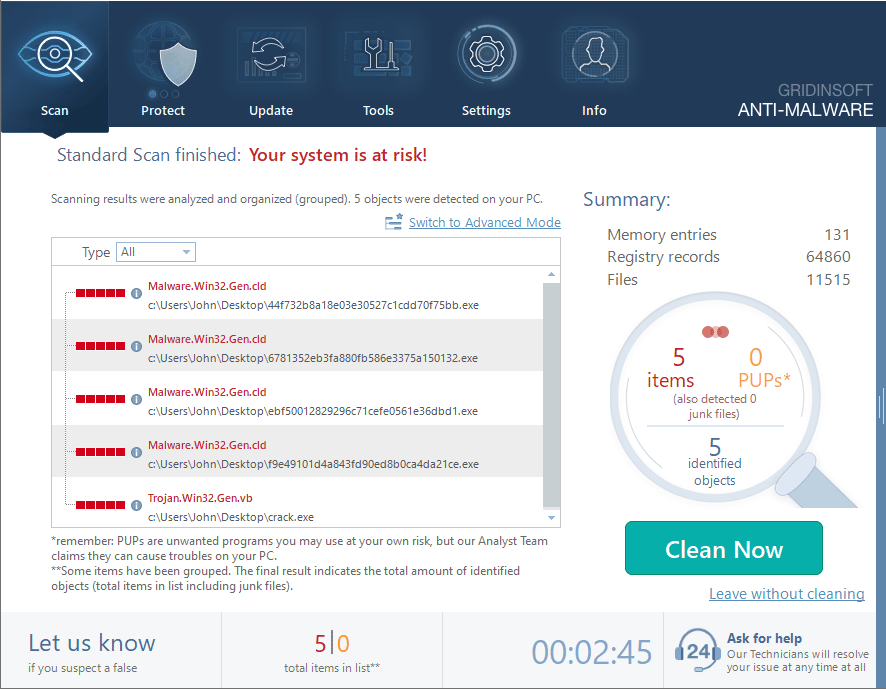
Download and install Anti-Malware by clicking the button below. After the installation, run a Full scan: this will check all the volumes present in the system, including hidden folders and system files. Scanning will take around 15 minutes.
After the scan, you will see the list of detected malicious and unwanted elements. It is possible to adjust the actions that the antimalware program does to each element: click "Advanced mode" and see the options in the drop-down menus. You can also see extended information about each detection - malware type, effects and potential source of infection.
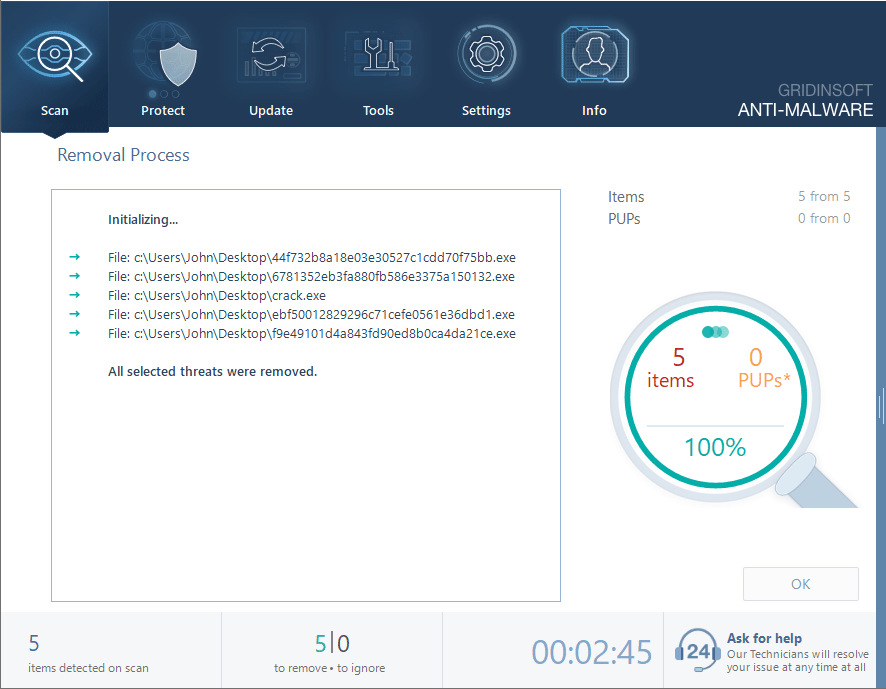
Click "Clean Now" to start the removal process. Important: removal process may take several minutes when there are a lot of detections. Do not interrupt this process, and you will get your system as clean as new.
The program will not only help you with removing this malware, but also prevent any further infections. Its detection system makes it effective even against the newest tricks – regardless of the way they’re packed. However, anti-malware software should be your last line of defense. To stay secure, it is better to avoid any muddy waters at all. In the case of Amadey malware, the key is to be vigilant when you deal with email messages. Read our detailed analysis of modern spam emails and the way to recognise them.