Trend Micro researchers reported recently that since September 2022, attackers have been actively using a malware obfuscation engine called BatCloak, which allows cybercriminals to effectively hide malicious code from antivirus solutions.
According to experts, with BatCloak attackers can easily download different families of malware and exploits through heavily obfuscated batch files. Of the 784 malware detected by researchers, almost 80% were not detected by any of VirusTotal’s antivirus engines.
Let me remind you that we also wrote that ChatGPT Has Become A New Tool For Cybercriminals In Social Engineering, and also that Russian Hacker Sells Terminator Tool That Is Allegedly Able To Bypass Any Antivirus Programs.
BatCloak is the basis for a batch file building tool called Jlaive that can bypass the Antimalware Scan Interface (AMSI) and compress and encrypt the main payload to increase evasion levels.
The Jlaive tool was published on GitHub and GitLab in September 2022 by a developer under the pseudonym ch2sh as “EXE to BAT crypter“. It has since been copied, modified and ported to other programming languages.
The final payload is a “three-layer loader” – a C# loader, a PowerShell loader, and a batch loader. The latter serves as the starting point for decoding and unpacking each stage, and ultimately launching the hidden virus.
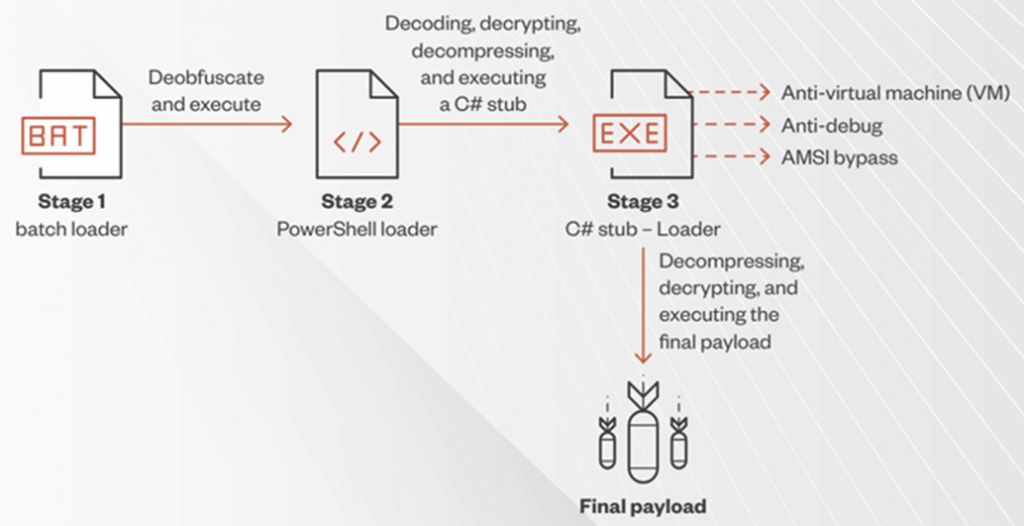
BatCloak attack chain
BatCloak has received many updates and adaptations since it first appeared in the wild (ITW). Its latest version is called ScrubCrypt and was isolated by Fortinet experts during an investigation into a cryptojacking operation by the 8220 gang.
In addition, ScrubCrypt is designed to be compatible with various well-known malware families such as Amadey, AsyncRAT, DarkCrystal RAT, Pure Miner, Quasar RAT, RedLine Stealer, Remcos RAT, SmokeLoader, VenomRAT, and Warzone RAT.




