Canadian fintech giant Moneris has been claimed to have been hacked by the notorious Medusa ransomware group. It sends shockwaves through the country’s financial sector. The group is known for its aggressive tactics and audacious targets. They have demanded a ransom of $6 million in exchange for stolen data and the prevention of further disruption.
Who are Moneris and Medusa?
Moneris, a joint venture between the Royal Bank of Canada and the Bank of Montreal, is Canada’s largest payment processor. They were handling over 3.5 billion credit and debit card transactions annually. The company serves as a critical intermediary for businesses of all sizes, making its compromise a significant threat to the country’s economic stability. Sure enough, any cybersecurity incidents, as companies prefer to call ransomware attacks, will set the community abuzz.
The Medusa ransomware group is a relatively new cybercrime gang that has gained notoriety for its ruthless strategies. Criminals operate under a ransomware-as-a-service (RaaS) model, providing its hacking tools and expertise to affiliates in exchange for a share of the ransom proceeds. This approach has enabled the group to expand its reach and inflict damage on a wide range of victims.
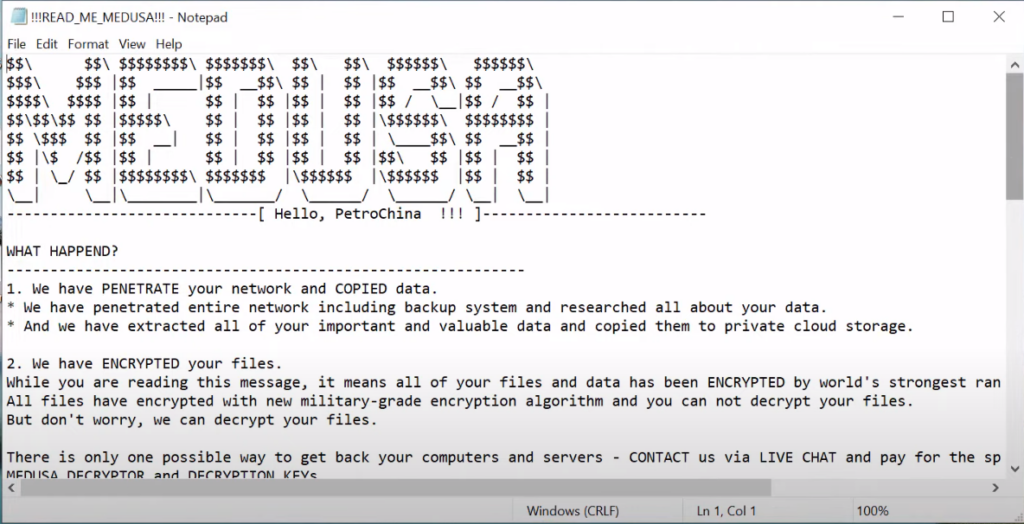
Medusa Ransomware attempt to compromise Moneris
Moneris has confirmed the attempted ransomware attack but has assured its customers that no critical data has been compromised. The company has also stated that it has implemented measures to restore its systems and continue operations.
In response to the Medusa ransomware attack, Moneris has taken steps to mitigate the damage and protect its customers. The company has engaged cybersecurity experts to investigate the incident. It also implemented additional security protocols and communicated regularly with its customers to keep them informed.
The fallout from this breach extends beyond Moneris itself. A disruption in Moneris services lasting 90 minutes in late September caused widespread issues across the country. The company’s extensive contracts with the US military raise additional concerns. Considering the potential compromise of sensitive information related to military equipment and weapons.
Critical Financial Institutions Under Attack
Attack on Moneris seems to be one more element of a chain of attacks on critical financial infrastructure. Just a couple of days ago, another infamous ransomware group – LockBit – successfully hacked ICBS – the biggest commercial bank in the world. Such an interest in financial companies is obvious, though the trend is not less concerning.
Huge money flow, probability of handling sensitive information, having tremendous amounts of statistics – this is what attracts the hackers, and what makes these two breaches so dangerous. Even though attacks are most likely unrelated, crooks may start targeting them much more often. And while Moneris hack is mostly about disruptions of money transactions, hacks of institutional orgs like ICBS puts the global financial system at risk.
How to Protect Against Ransomware?
The incident highlights the growing sophistication and severity of ransomware attacks, targeting not just individual users but also large, well-established corporations like Moneris. The financial and reputational implications of such attacks can be devastating, making it crucial for businesses to invest in robust cybersecurity measures and maintain vigilance against evolving cyber threats. Here are some tips on how to protect against ransomware:
- Regularly backing up your data is crucial for its safety. Create an offline backup of your hard disk-stored files to protect your data. This is a copy of your data saved on a separate device not connected to your computer or network. If ransomware attacks your computer, the backup files will not be affected, and you can restore them without paying a ransom.
- It is important to keep your software up to date as software updates include crucial security patches that protect against ransomware attacks. Most software programs offer the option for automatic updates which will ensure that your software is always updated with the latest security patches.
- Train your employees. Conduct regular cybersecurity awareness training for employees to educate them about ransomware threats and safe online practices.
- Use reliable software. Install reputable antivirus and anti-malware software on your devices. Consider using additional security tools that offer real-time protection against ransomware.
- Be careful with user privileges. Follow the principle of least privilege (PoLP) to restrict user access to the minimum necessary for their roles.





