Intel has fixed a serious Reptar vulnerability in various processors for desktops, servers, mobile devices and embedded systems. This has also proven to be a problem for the latest Alder Lake, Raptor Lake, and Sapphire Rapids microarchitectures.
The Reptar vulnerability can be used to escalate privileges, gain access to sensitive information, and cause denial of service. However, at least its fixing does not require intervention at the hardware level, as was in the case of an LVI attack.
Reptar Vulnerability in Intel CPUs Allow for Privileges Escalation
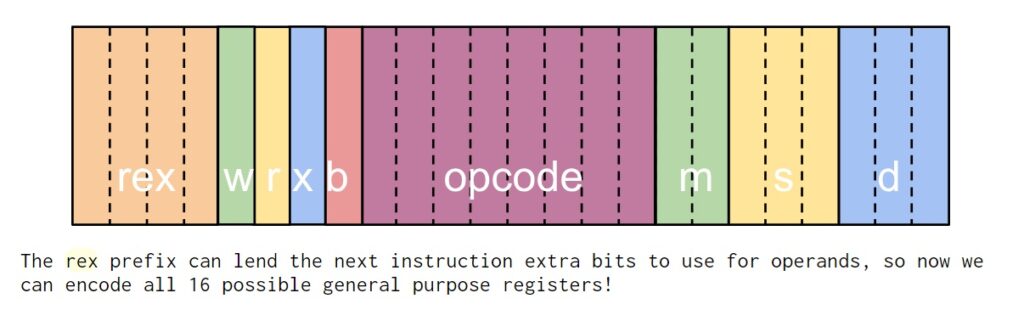
The vulnerability, discovered by Intel engineers themselves, has received the identifier CVE-2023-23583 and is described as an “REX prefix issue”.
Initially, it was believed that the error could be used only to provoke a denial of service. The vulnerability received only a CVSS score of 5.5. Intel initially planned to release a patch for it in March 2024.
However, deeper analysis showed that there was a way to exploit the bug to escalate privileges. And Intel moved the release date of the patch to November 2023. As a result, the vulnerability rating was changed to 8.8 points on the CVSS scale.
Intel does not expect any non-malware software to encounter this problem in the real world. It is expected that redundant REX prefixes will not be present in the code and will not be generated by compilers.
Malicious exploitation of the Reptar issue requires the execution of arbitrary code. Also, as a part of an internal review Intel identified the possibility of privilege escalation in certain scenarios.
Systems with affected processors, including Alder Lake, Raptor Lake and Sapphire Rapids, have already received updated firmware, and these patches do not impact performance.
Other Threats to Intel Processors
The history of Windows processor problems is quite rich. We also wrote about the Snoop attack, which can stop processors. And about the Platypus attack, which could be used by attackers to steal data. And also about problems with Active Management Technology (AMT) and Intel Standard Manageability (ISM).
However, earlier this year the media also wrote about one of the most serious errors in the history of Intel processors. It was CVE-2021-39296 issue (10 out of 10 on the CVSS scale). This vulnerability affected the integrated BMC (Baseboard Management Controller) and OpenBMC firmware on several of the company’s platforms. The issue CVE-2021-39296, as its ID shows, was discovered back in 2021, but was fixed only two years later.
Are processor vulnerabilities that dangerous?
Problems with processors are usually perceived as painful due to the fact that they are everywhere. They are the basis of almost any electronic device. And an exploitable vulnerability in Intel or AMD products can make millions of users around the world dependent on the actions of attackers.
A complete list of Intel processors affected by the CVE-2023-23583 vulnerability, as well as recommendations for resolving it, are available here.