Trend Micro experts have discovered that hackers are abusing the system anti-cheat driver of the popular game Genshin Impact to disable anti-virus software during ransomware attacks. Mhypro2.sys gives access to the memory of any process and kernel, and is also able to terminate processes with the highest privileges.
Let me remind you that we also wrote that Tencent and Chinese police conducted a joint operation against game cheat developers.
The mhypro2.sys problem has been known since at least 2020, and information security experts have long been appealing to manufacturers of anti-cheat systems in general, since most of these solutions work at the ring 0 level, which can hardly be considered safe.
In the case of mhypro2.sys, the appeals of experts had no effect, the code signing certificate was not revoked, and therefore the program can still be installed on Windows without raising alarm. Worse, since 2020, two PoC exploits are available on GitHub at once and a detailed description of how you can use anti-cheat from user mode to read/write kernel memory with kernel mode privileges, terminate specific processes, and so on.
A recent Trend Micro report states that hackers have been abusing the driver since July 2022 and using it to disable properly configured security solutions.
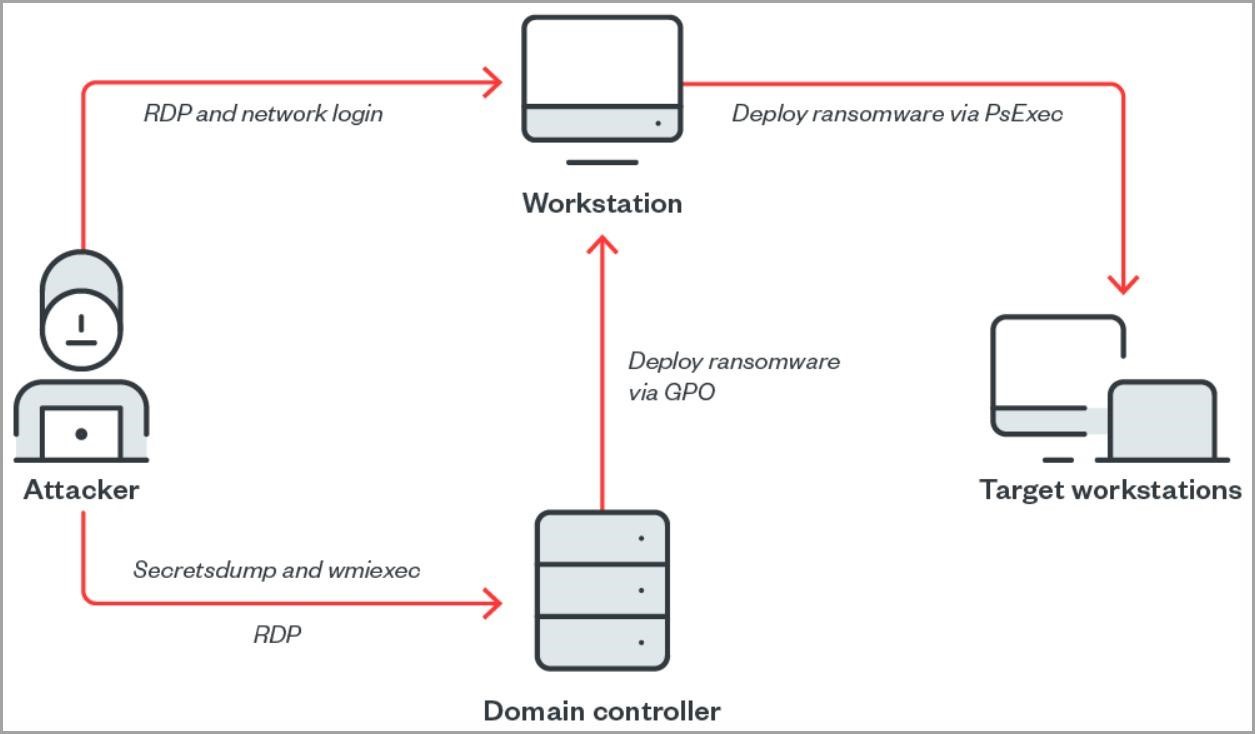
Analysts write that in the example they studied, the attackers used secretsdump and wmiexec against the target machine, and then connected to the domain controller via RDP using stolen administrator credentials.
The first action taken by the hackers on the compromised machine was to transfer mhyprot2.sys to the desktop along with the malicious executable kill_svc.exe that was used to install the driver. The attackers then downloaded the avg.msi file, which in turn downloaded and executed the following four files:
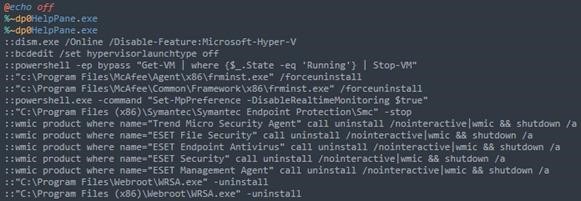
- logon.bat – launches HelpPane.exe, “kills” the antivirus and other services, launches svchost.exe;
- HelpPane.exe – disguises itself as the Microsoft Help and Support executable file, similar to kill_svc.exe, as it installs mhyprot2.sys and “kills” anti-virus services;
- mhyprot2.sys – Genshin Impact anti-cheat driver;
- svchost.exe – An unnamed ransomware payload.
In this incident, the hackers tried three times to encrypt the files on the compromised workstation, but were unsuccessful, but the anti-virus services were successfully disabled. In the end, the attackers simply moved logon.bat to the desktop, running it manually, and it worked.
By the end of the attack, the hackers uploaded the driver, ransomware, and the kill_svc.exe executable to a network share for mass deployment, aiming to infect as many workstations as possible.
Trend Micro warns that hackers may continue to use the anti-cheat module, because even if the vendor does fix the vulnerability, old versions of mhypro2.sys will still be in use, and the module can be integrated into any malware. At the same time, experts note that while code-signing modules that act as device drivers that can be abused are still quite rare.

In response to the publication of this report, well-known information security expert Kevin Beaumont noted on Twitter that administrators can protect against this threat by blocking the hash “0466e90bf0e83b776ca8716e01d35a8a2e5f96d3”, which corresponds to the vulnerable mhypro2.sys driver.

