An anonymous hacker posted about a Plume data breach on the Darknet. The hacker says they have stolen the personal information of millions of users and threaten to release the data unless the company pays them a ransom.
What is Plume?
Plume Design, Inc. develops and sells smart home Wi-Fi mesh networking systems. Its flagship product, the Plume SuperPod, is a mesh Wi-Fi system that uses AI to optimize network performance. Plume also provides software features such as parental controls, network security, and motion sensing. ISPs, cable companies, and telecoms use the company’s technology.
It works as a Software-as-a-Service (SaaS) specializing in smart Wi-Fi solutions, cloud management, and AI-driven security services. Operating in over 45 countries, the company boasts a significant user base, claiming to serve more than 55 million homes and small businesses.
Plume Data Breach Details
Plume, a leading provider of smart WiFi services, finds itself at the center of a potential data breach. The attackers have purportedly posted gigabytes of user data on a prominent data leak forum. The breach, if confirmed, could impact millions of Plume’s customers and staff members. Attackers claim to have successfully infiltrated Plume’s systems, making off with a substantial 20GB of data from the company’s WiFi database. This trove of information reportedly encompasses more than 15 million lines, featuring diverse user profiles, including mobile app users, customers, and even Plume’s internal staff.
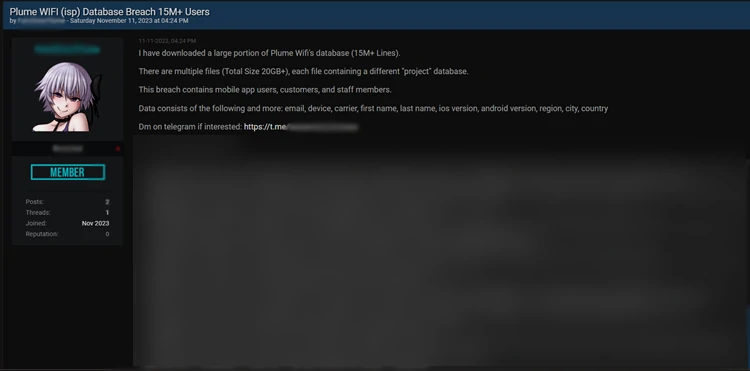
The attackers said the dataset encompasses sensitive information like email addresses, device details, carriers, first and last names, iOS and Android versions, and more. As for the company’s reaction, Plume’s response to the claims has been prompt, acknowledging the alleged breach and initiating an internal investigation. A representative from Plume stated, “We are aware of the claim, and our teams are actively investigating the situation.”
Data Sample Validation
The research team has delved into the data sample provided by the attackers, affirming that the sample aligns with the details outlined in the attackers’ statements. However, the lack of a complete data set from the attackers raises questions about the authenticity of the leaked information. Without a comprehensive dataset, whether the compromised data genuinely belongs to Plume or was sourced from an alternative origin remains uncertain.
Notably, the attackers have taken an unconventional approach by creating an X account and announcing the alleged breach on social media platforms. This departure from traditional covert channels raises some eyebrows within the cybersecurity community. In contrast, attackers typically opt for discreet methods when publicizing their exploits.
Potential Impacts
As Plume’s investigative teams delve deeper into the situation, users are advised to remain vigilant and consider implementing additional security measures. While the company is actively addressing the claims, the potential exposure of sensitive information necessitates a proactive approach from users to safeguard their data.




