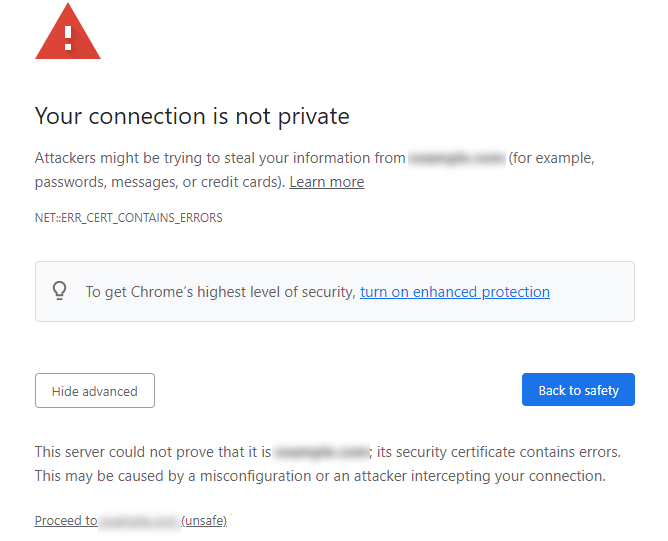
HTTPS and HTTP are constantly around us, but their difference is not really clear. What do they differ with? And why do I see these “Your connection is not secure” pop-ups when the connection is HTTP? In this article, I will explain the HTTPS vs HTTP difference and what connection type you should stick to.
HTTPS vs HTTP
HTTPS and HTTP are two protocols for transferring data between web browsers and servers. The main difference between the two is the level of security and the way data is transmitted. For example, HTTP does not use encryption, so all data is sent or received as is. This makes them vulnerable to being intercepted and read by attackers in Man-in-the-Middle attack. This protocol is suitable for transmitting publicly available information that does not require protection.
On the other hand, HTTPS encrypts the transmitted data, providing protection against malicious users reading it. It also utilizes some features, which I will discuss in more detail. This protocol is the standard for transmitting sensitive information and establishing secure connections. Today, almost all websites use HTTPS.
What Is HTTP?
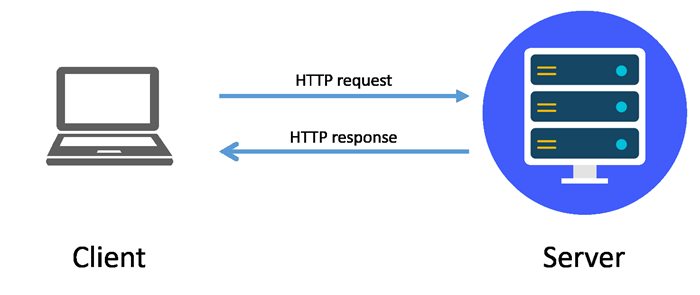
HTTP stands for HyperText Transfer Protocol. It is the foundational protocol the World Wide Web uses to transfer and display information on websites. HTTP operates on a client-server model where the browser (client) requests information, and the web server responds with the requested data. HTTP uses port 80 by default for insecure connections and standardized messages to facilitate communication between clients and servers. These messages include methods such as GET, POST, PUT, and DELETE, as well as status codes such as “200 OK”, “400 Bad Request”, “404 Not Found,” and “500 Internal Server Error”.
The first version of HTTP was released in 1997 and was called HTTP/1.1. Over time, updated versions of HTTP/2 and HTTP/3 have been released to improve performance and reliability. One of HTTP’s greatest strengths is its simplicity, which makes it easy to develop new applications and services that use HTTP as a base protocol.
What is HTTPS?
HTTPS stands for HyperText Transfer Protocol Secure. It is an extension of HTTP designed to provide secure communication over a computer network. HTTPS uses encryption to protect data exchanged between the client and the server. HTTPS uses Transport Layer Security (TLS) or its predecessor, Secure Sockets Layer (SSL), to encrypt the data transmitted between the browser and the server. SSL/TLS certificates contain public and private encryption keys for secure data transfer between browsers and websites. This ensures that even if the data is intercepted, it cannot be read without the decryption key.
When a user requests a website, the server sends a certificate containing a public key verified by the user’s browser. The browser and server establish a secure connection using a TLS handshake. By default, HTTPS uses port 443 for connections. During this handshake, they agree on a shared secret key that will be used to encrypt and decrypt the data.
By encrypting data and verifying a website’s identity, HTTPS provides users with a secure way to share and receive information online without worrying about the security of their data. This security makes HTTPS an essential protocol for online transactions, including online banking and e-commerce.
Why is HTTP Not Safe?
In fact, the HTTP protocol is hardly used today as it is vastly inferior to HTTPS. First, HTTP does not encrypt data between the server and the client, making it a cakewalk for attackers to intercept your transmitted data. Moreover, HTTP’s lack of authentication makes it a prime target for man-in-the-middle attacks.
In addition, HTTP does not authenticate the server to which the client is connecting. This allows attackers to spoof websites and trick users into providing sensitive information. When using HTTP, there is no guarantee that data has not been altered during transmission, making attacks aimed at spoofing or modifying data possible.
How to Verify I’m Using HTTPS?
To verify that you are using HTTPS when browsing a website, look at the URL in your browser’s address bar. It should start with “https://” instead of “http://”. Also, pay attention to the padlock icon in the address bar, usually to the left of the URL. A closed padlock indicates that the connection is secure.
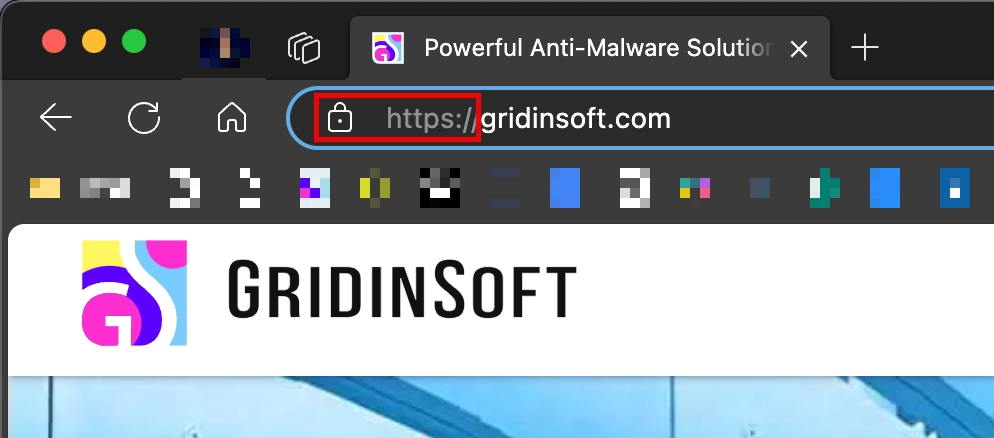
Modern browsers often use additional indicators or visual cues, such as highlighting the address bar in green to show that the site uses HTTPS and has a valid SSL/TLS certificate. You can also click the lock icon for more information about connection security.
How to Boost Online Security?
Improving web browsing safety requires quite a lot of attention, but once you get used to it, the process will become almost unnoticeable. First, be vigilant when surfing the web and use a security solution. Pay attention to the lock icon in the address bar, and do not enter any sensitive data on sites that do not use encryption.
Another tip here is to use a software that can block suspicious and phishing pages. GridinSoft Anti-Malware has a built-in Internet security module to block phishing, scam and other shady pages. Try it out by pressing the banner below!








Thanks for the useful article. SSL nowadays is important