Hackers actively use driver signature spoofing, which originates from a loophole in Windows kernel-mode drivers handling mechanism. They heavily bear on open-source utilities that were primarily designed for temporal circumvention of drivers signing, which is a far too big delay when it comes to evaluations. Cybercriminals though do not do any tests, and do hit and run things instead.
Windows Kernel Driver Signature Hacks
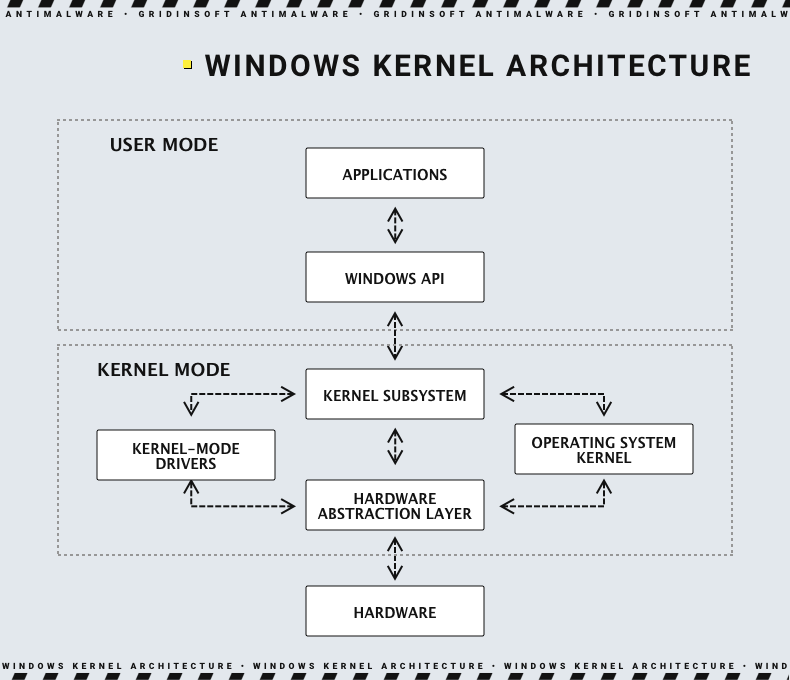
Microsoft has a long history of protecting its operating system from being exploited with malicious drivers. In fact, they have a continuous battle going since early 2007 – the release date of Windows Vista. In this patch, the developers implemented a mechanism that forbids unsigned drivers from running. Kernel-level drivers have access to any possible functionality of both the OS and hardware components. Further, in 2016, Microsoft created a centralised driver signature authority – Developer Portal – which is the only place to sign Windows drivers since Windows 10 1607 release. All this was done to decrease the possibility of malicious use of a signed driver.
This, however, was not suitable for all developers of benevolent software. Similar to pretty much any centralised authority, Developer Portal has a lag between sending the driver, its review, and receiving a signature. As a result, urgent processes like real-world tests or even simple debugging have become impossible. Another industry where cert forging is in use is game cheats, that circumvent anti-cheat engine protection by implementing on the same, kernel level. Once again – the system simply refuses to run the driver once it is not signed. The only way here was creating a detour, and in this case such was a free open-source utilities called HookSignTool and FuckCertVerifyTimeValidity.
How do driver certificate hacktools work?
Both of these programs have pretty much the same mechanism. They exploit one of three rules of backward compatibility for legacy drivers. Microsoft left them to make drivers signed prior to July 29, 2015 possible to use – which is essential for old programs and hardware. Those rules are:
- System was upgraded from an earlier Windows version to Windows 10 1607
- Drivers was signed with an end-entity cert by the cross-signed certificate authority before July 29, 2015
- System has the Secure Boot option disabled in the BIOS.
Actually, utilities aim at exploiting the second rule. They simply spoof the driver signature with the one issued by a legit CA before the date. And while it is useful for software developers that urgently need to test something and have no time to wait for DevPortal’s reaction, it is similarly useful to cybercriminals.
During the first half of 2023, security analysts have noticed numerous examples of these utilities exploitation for signing malware that integrates into the system as kernel-level drivers. Such a deep integration, especially considering the total system acceptance of that driver, grants malicious programs with unlimited capabilities. Such malware is hard to detect with anti-malware software and, what’s even worse, particularly hard to remove without wiping the disk out.
Microsoft Keeps Dozens of Expired Certificates
To operate properly, the mentioned utilities require an expired, but non-revoked certificate installed in the system. HookSignTool offers its own one, FuckCertVerify uses a pack of leaked certs to forge the signature. And these exact certs were detected during recent cyberattacks. Deeper analysis reveals that Windows carries over a hundred exploitable certs that were expired long ago. Among them, analysts name several that were actively used in cyberattacks:
- Open Source Developer, William Zoltan
- Beijing JoinHope Image Technology Ltd.
- Shenzhen Luyoudashi Technology Co., Ltd.
- Jiangsu innovation safety assessment Co., Ltd.
- Baoji zhihengtaiye co.,ltd
- Zhuhai liancheng Technology Co., Ltd.
- Fuqing Yuntan Network Tech Co.,Ltd.
- Beijing Chunbai Technology Development Co., Ltd
- 绍兴易游网络科技有限公司
- 善君 韦
- NHN USA Inc.
- Luca Marcone
- HT Srl
High number of Chinese certs is explained by the fact that the HookSignTool utility is made by Chinese programmers. As it carries certificates for signature forging inside of its installation package, their location is to be expected. Another interesting element there is that hackers who use these utilities appear to be Chinese as well. Such a guess comes from the language code of the malware samples from the attacks that used certificate forging utilities.
How to protect against malware with forged certificates?
Fortunately, there is a particularly easy advice, though some people may hate its very essence. Update your Windows – new patches have the certificates that appear in these attacks marked as untrusted. Microsoft cooperates with cybersecurity researchers and vendors, and any certs used in such circumstances are reported instantly. Well, delivering updates can take some time, but be sure to check your Update tab, if you want to avoid such an unpleasant thing to run on your PC.
The problem here is the fact that antivirus system can have problems with detecting such a threat. Classic antivirus programs, that does not have behaviour analysis features, will simply miss an item that has been legitimized in such a way. For that reason, an advanced solution is a must-have. For corporations, those are EDR/XDR solutions, which have behaviour analysis as their primary source of information. Home users can try GridinSoft Anti-Malware to detect and remove malicious programs even before they’re active.