Signal creator, renowned cryptographer, hacker, researcher and anarchist Moxie Marlinspike studied the products of the famous Israeli cybercriminalistic company Cellebrite and identified a number of vulnerabilities in their work.
In particular, the bugs allowed him to execute malicious code on a Windows computer that was used to analyze devices.
Let me remind you that Cellebrite are independent cybercriminals who specialize in extracting data from mobile devices (iOS and Android). For example, several years ago, an Israeli firm was named the main candidate for the role of an FBI contractor when law enforcement officers were looking for specialists to hack a terrorist’s iPhone.
Overall, Cellebrite has helped governments and law enforcement agencies around the world in hacking seized mobile phones (mostly through exploiting vulnerabilities that device manufacturers have ignored).
How Marlinspike gained access to Cellebrite equipment is unknown. He ironically says that this happened due to an “incredible coincidence”: he allegedly walked down the street and “saw a small package fall out of the truck” with the Cellebrite logo.
Probably, it was not so difficult to acquire such a set. Back in 2016, Vice Motherboard journalists conducted their own experiment, which showed that anyone can purchase such a set.
In the Signal blog, the expert explains that Cellebrite’s software works by analyzing data from an untrusted source. That is, the software accepts an input that may be incorrectly formatted, and this can provoke information corruption in memory, which will lead to the execution of arbitrary code in the system.
The researcher also discovered that Cellebrite software uses an old open-source code, which Cellebrite developers have not updated for almost ten years (although security updates have been released more than once during this time).
As a result, Marlinspike was able to run arbitrary code on the Cellebrite machine when it parsed a specially prepared file on a scanned device.
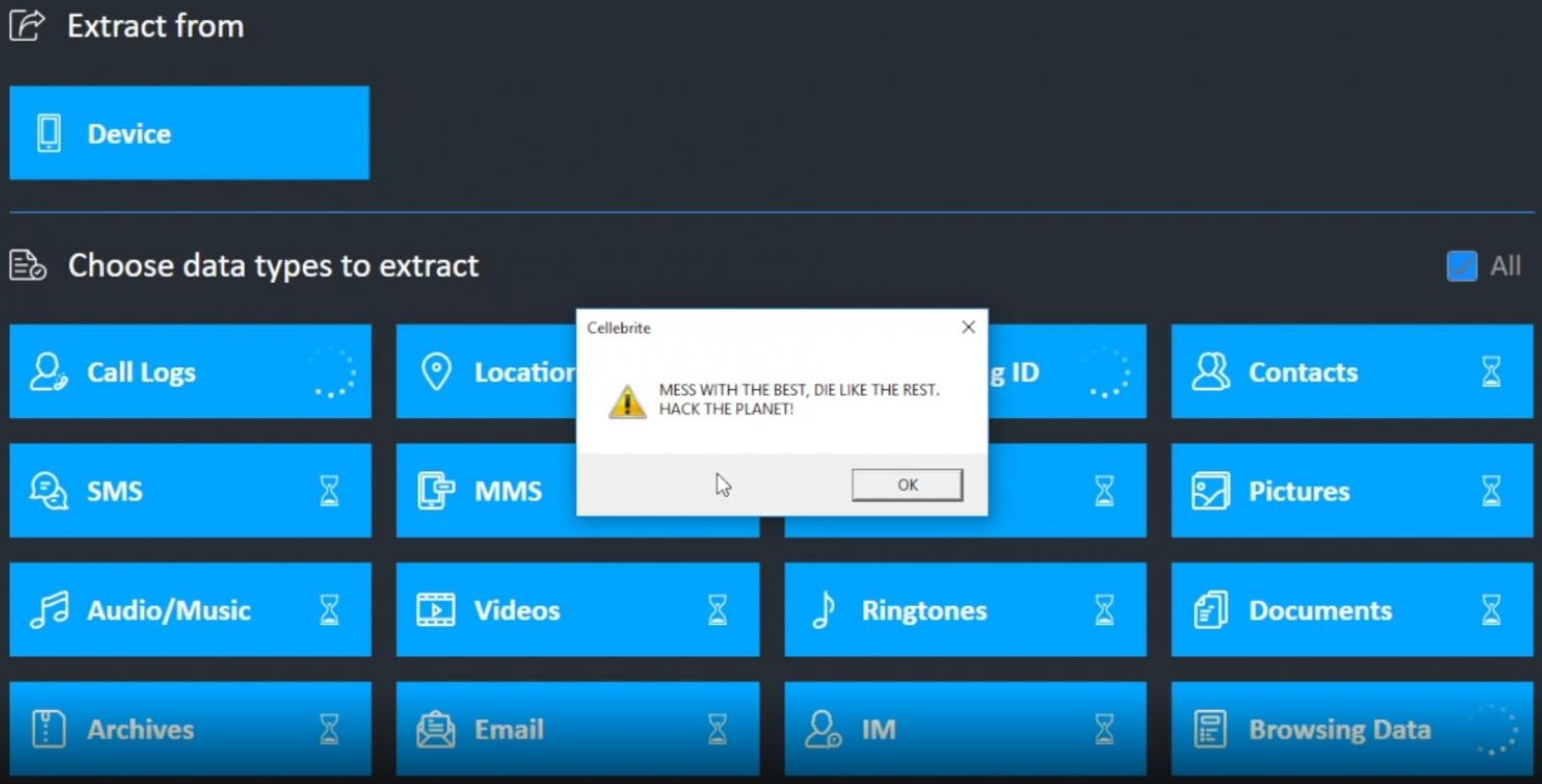
Marlinspike has posted a Proof of Success for a UFED product, his payload uses the Windows MessageBox API:
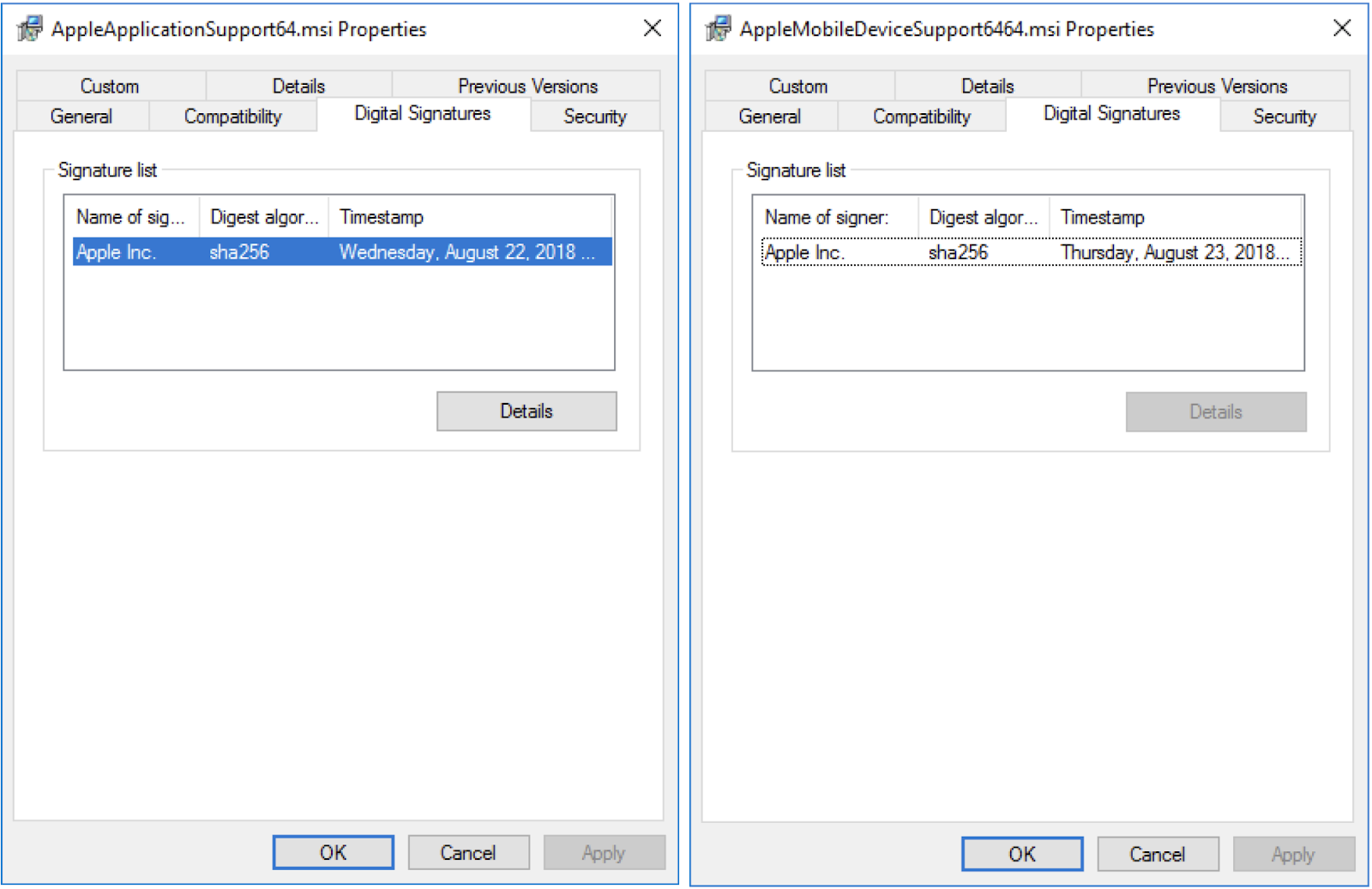
In addition, Marlinspike found digitally signed MSI packages from Apple in the Packet Analyzer installer. They appear to be pulled from the Windows Installer for iTunes 12.9.0.167 and contain DLL files that help Cellebrite software interact with and retrieve data from iOS devices.
Marlinspike summarizes that he will happily provide Cellebrite developers with details of all vulnerabilities if the company responds by doing the same for all vulnerabilities that it uses for its services “now and in the future.”
Cellebrite representatives have already told the media that for the company is very important “the security and integrity of customer data,” and also assured that they “constantly check and update” their software. At the same time, the company did not comment on the problems discovered by the expert in any way, and did not say whether the company had permission to use Apple software.
Let me also remind you that we talked about the researcher showing how to steal a Tesla Model X in a few minutes.