Most Often, Malware to Bypass Protection Impersonates Skype, Adobe Acrobat and VLC
VirusTotal analysts presented a report on the methods that malware operators use to bypass protection and increase the effectiveness of social engineering. The study showed that attackers are increasingly imitating…
ParseThru Vulnerability Threatens Go-Based Applications
Researchers have discovered a vulnerability called ParseThru — the bug affects Go-based products and can be abused to gain unauthorized access to cloud applications. Experts from the Israeli company Oxeye,…
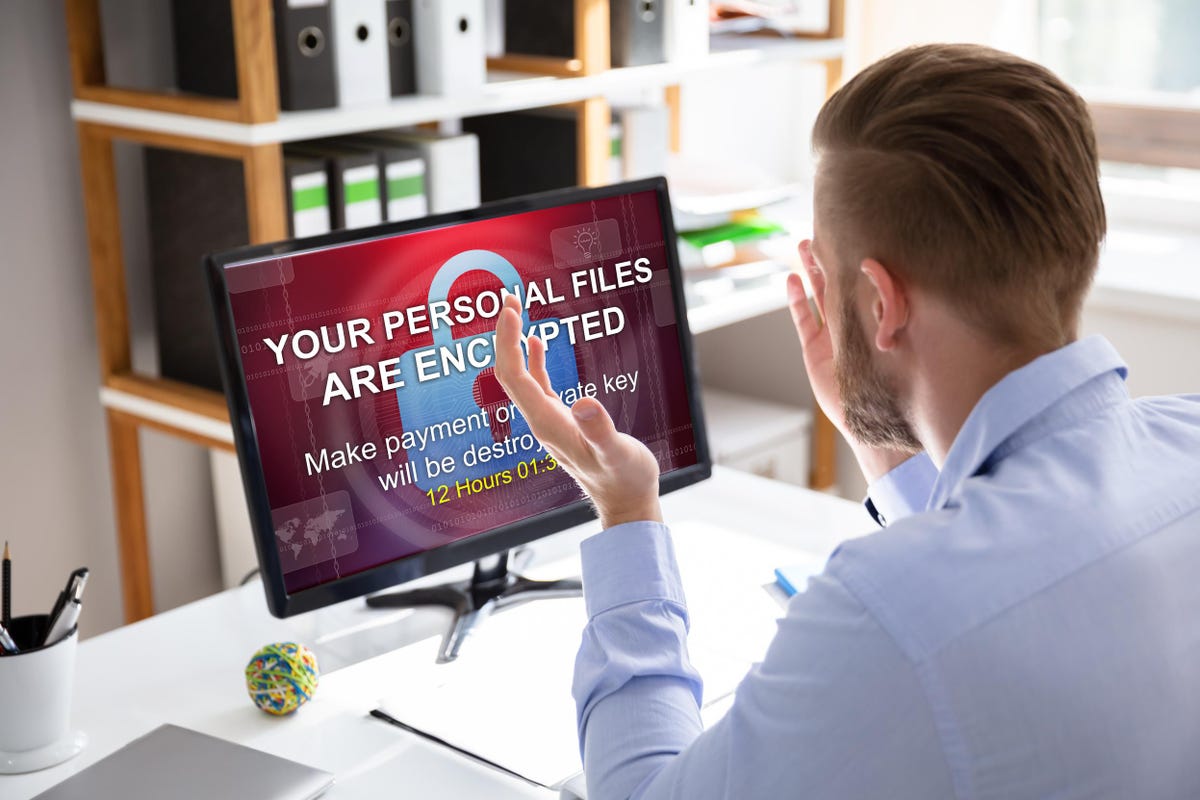
BlackCat Says It Attacked Creos Luxembourg, European Gas Pipeline Operator
The operators of the BlackCat ransomware (aka ALPHV) claimed responsibility for hacking Creos Luxembourg, which operates a gas pipeline and electricity grid in central Europe. Encevo, which owns Creos Luxembourg…
Djvu Ransomware Spreads via Discord, Carrying RedLine Stealer
An infamous STOP/Djvu ransomware adopted a new spreading tactic. According to the report of Avast Threat Labs, a malware intelligence group, ransomware distributors opted for Discord as a place to…
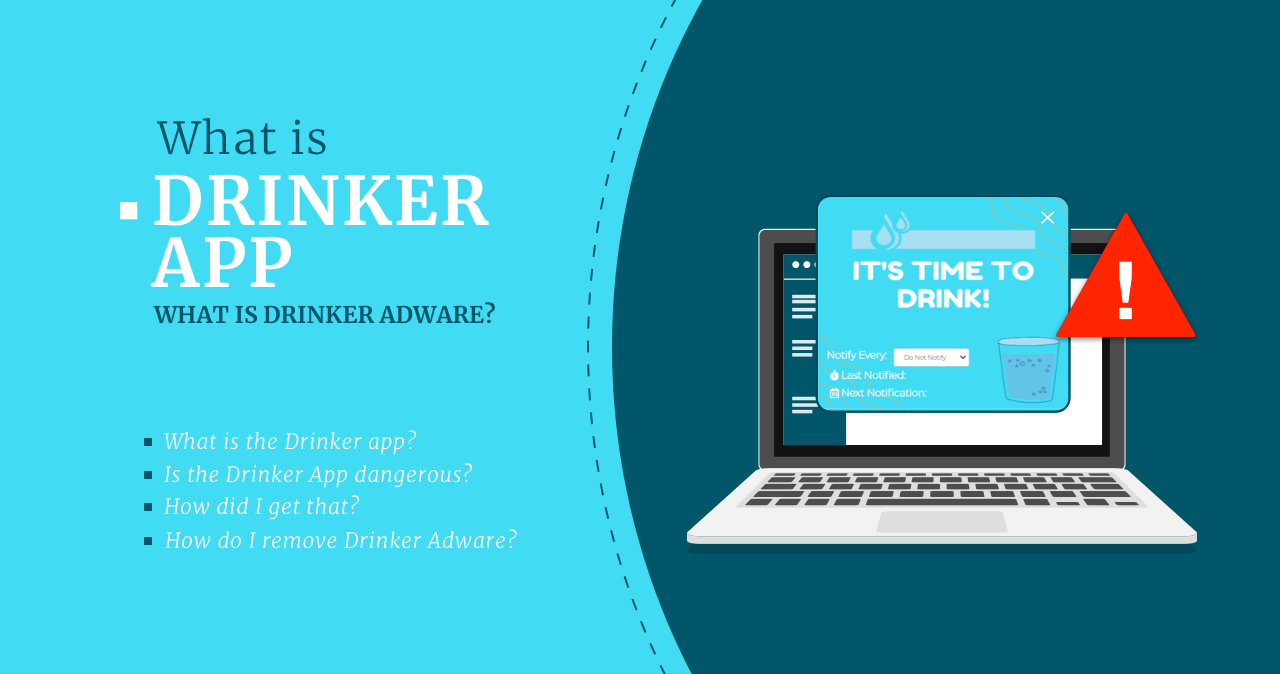
Drinker App – what is Drinker Adware?
The Drinker app is another example of a malicious program that disguises itself as a useful utility for your PC. Another two - Healthy and Strength - popped up almost…
Microsoft Links Raspberry Robin Worm to Evil Corp
Microsoft analysts have noticed that the access broker, which the company tracks as DEV-0206, is using the Raspberry Robin Windows worm to deploy the malware loader on networks where traces…
10 Reasons to Choose GridinSoft Trojan Killer
We used to think of anti-malware software as a program that features all kinds of supplementary services. VPN plan, disk encryption tool, guest mode and parental control - all of…
Healthy App (HealthySoftware) – What is Healthy?
Healthy App seems to be the companion of the other unwanted app - Strength Adware. The dubious application gets into users’ PCs to show them tons of advertisements. Let’s check…
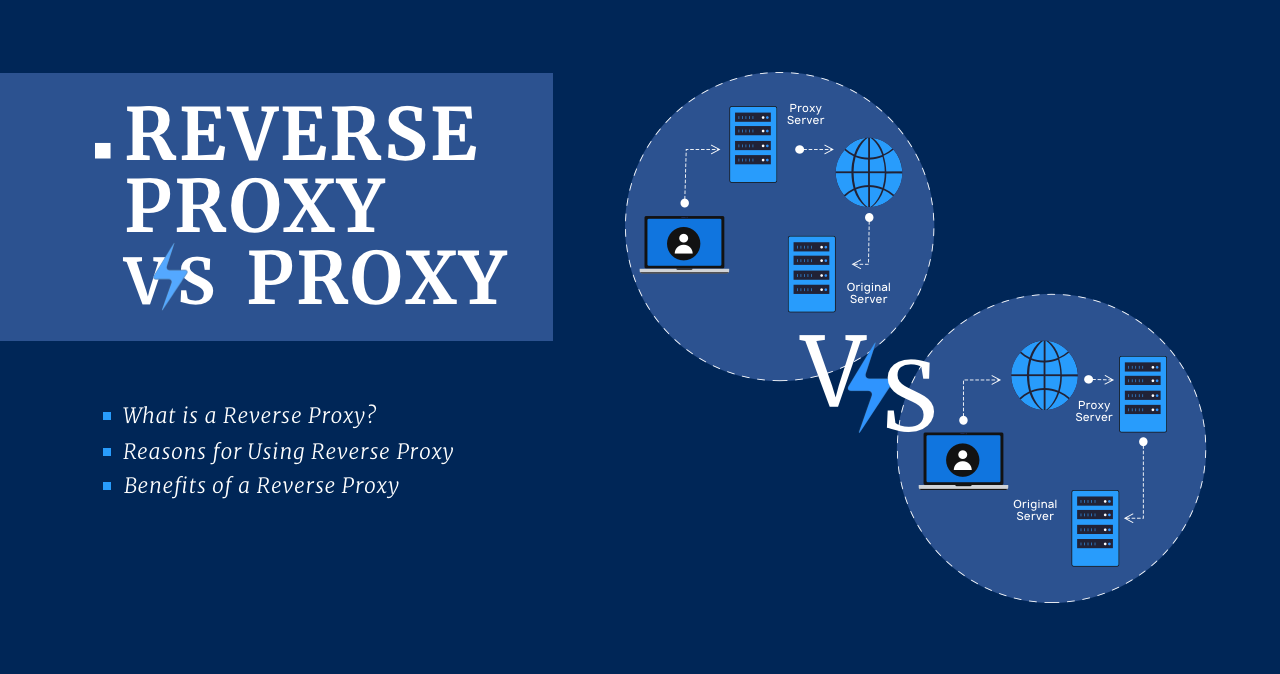
Reverse Proxy vs Proxy
What is a Reverse Proxy? A reverse proxy is the same server but is in front of a web server. Depending on its configuration, it allows or refuses the external…
Strength Adware – What Is Strength App?
Strength Adware, a new advertising malware, began appearing on users’ devices. It is still not clear how it manages to get into the system, but its effects are not pleasant.…
The Austrian Company DSIRF Was Linked to the Knotweed Hack Group and the Subzero Malware
Microsoft has been told that the Knotweed hack group is linked to the Austrian spyware vendor DSIRF, which also often acts as a cyber mercenary. Researchers have determined that Knotweed…
Experts Find Similarities Between LockBit and BlackMatter
Cybersecurity researchers have confirmed similarities between the latest iteration of LockBit ransomware and BlackMatter. A new version of LockBit 3.0 (LockBit Black) was released in June 2022, along with a…