Penetration Testing: Stages and Methods
What is penetration testing? Penetration testing is a method by which the…
Around 2000 People Arrested by Interpol for Internet Scams
Operation "First Light" The war on cybercrime goes on. As its next…
VPN, Proxy, or Tor: Differences, Meaning
You've probably heard the words VPN, Proxy, and Tor. You may even…
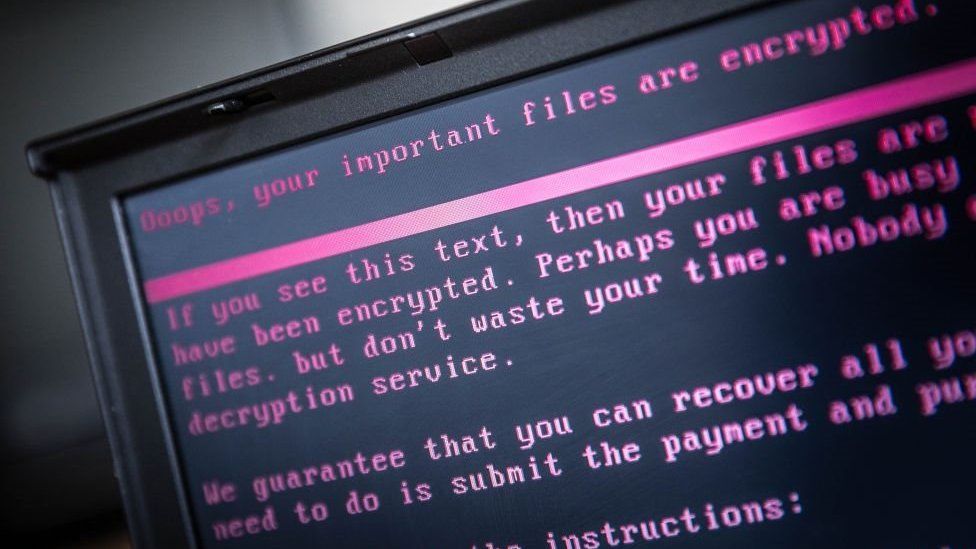
BlackCat ransomware gang publishes leaked data on the clear web site
BlackCat/ALPHV group recently announced on its victim shaming and extortion website that…
War in Ukraine triggered a Stream of amateurish ransomware
Russia has provoked hackers around the world to focus their attacks on…
The US Will Introduce A Cyber Army Into Its Military Units
By 2030 the US plans to double the size of its military…
Iranian Spear-Phishing Operation Targets US And Israeli High Executives
In a wake of rising tensions between Israel and Iran, researchers from…
TOP DNS Attacks Types
What is a DNS (Domain Name Server) Attack? A DNS attack is…
BlackCat Ransomware Attacks Italian University
An Italian university was hit by BlackCat this week. The hackers demand…
Difference Between Phishing and Pharming
Intruders try to keep up with the development in the digital world.…
Smishing And Vishing: Differences To Know About Phishing Attacks
You can say it has become much easier for various criminals to…
IPv4 vs IPv6: What’s the Difference?
What is IPv4 and IPv6? IP addresses allow computers and devices to…