The Security Blog From Gridinsoft
RarBG Torrenting Site Is Shut Down, Admins Explain Why
RarBG, one of the most famous torrent tracker websites in the world, decided to voluntarily shut down. Launched in 2007,…
Ransomware Attacks in 2023: What to Expect?
Cybersecurity experts have published a report on worrying ransomware statistics. A survey of 435 cybersecurity professionals identified gaps, misunderstandings, and…
RaidForums Leaked, Data of Almost 500,000 Users Published
RaidForums, the former leader among the underground forums, now suffers the user data leak. Besides being shut down in April…
New MDBotnet Malware Rapidly Expands a DDoS Network
MDBotnet is a new malware strain that appears to be a backbone of a botnet, used in DDoS-as-a-Service attacks. Being…
Ransomware Attacks Decline in 2023 – Is It True?
According to ransomware attacks status statistics, the trend of incidents related to this type of malware will decline in 2023.…
New worm for Android spreads rapidly via WhatsApp
ESET security researcher Lukas Stefanko reported a new malware: he…
Researcher Found Three Bugs Allowing Hacking Amazon Kindle
Researcher Yogev Bar-On from Israeli consulting firm Realmode Labs talked…
Chinese hack group Chimera steals data from air passengers
According to reports of cybersecurity researchers, the Chinese hack group…
Raindrop is another malware detected during the SolarWinds hack
Symantec specialists detected Raindrop malware, which was used during the…
Windows 10 bug causes BSOD when opening a specific path
A bug in Windows 10 causes the OS to crash…
Hackers majorly use Microsoft and DHL brands in phishing attacks
Hackers majorly use the Microsoft and DHL brands in phishing…
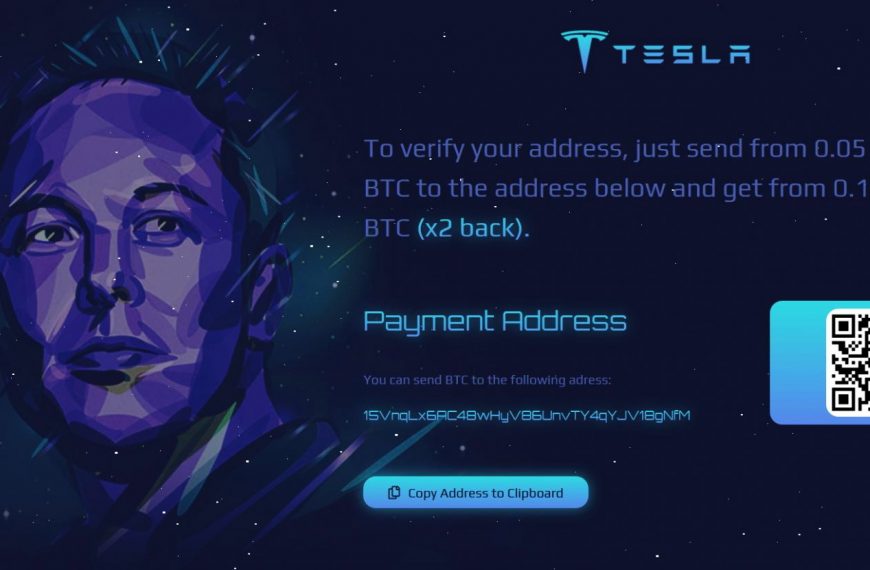
Fake cryptocurrency giveaways on behalf of Elon Musk brought scammers $580,000
The media have repeatedly written that scammers sometimes impersonate famous…
Google experts exposed sophisticated hacking campaign against Windows and Android users
Google published a large report detailing how they exposed a…
Experts discovered SolarLeaks website with data stolen in a recent massive hacker attack
Bleeping Computer reports the discovery of the SolarLeaks website (solarleaks[.]net),…
Extortionists hack into Cellmate men’s chastity belts
Last fall, researchers from Pen Test Partners reported on the…
Nissan source code leaked due to admin: admin credentials
The source code for mobile apps and internal tools for…
Storming of the US Congress poses a serious threat to cybersecurity
Storming of the US Congress in Washington, in addition to…