Google published a large report detailing how they exposed a sophisticated hacking campaign that was discovered back in early 2020. The campaign targeted Android and Windows users, and attackers exploited for attacks four zero-day vulnerabilities.
The researchers say the attacks they discovered were carried out from two exploit servers (one for Android, the other for Windows) and used a watering hole technique.
Both servers exploited vulnerabilities in Google Chrome to gain a foothold on victims’ devices. Next, the attackers deployed the exploit at the OS level in order to gain more control over the infected device.
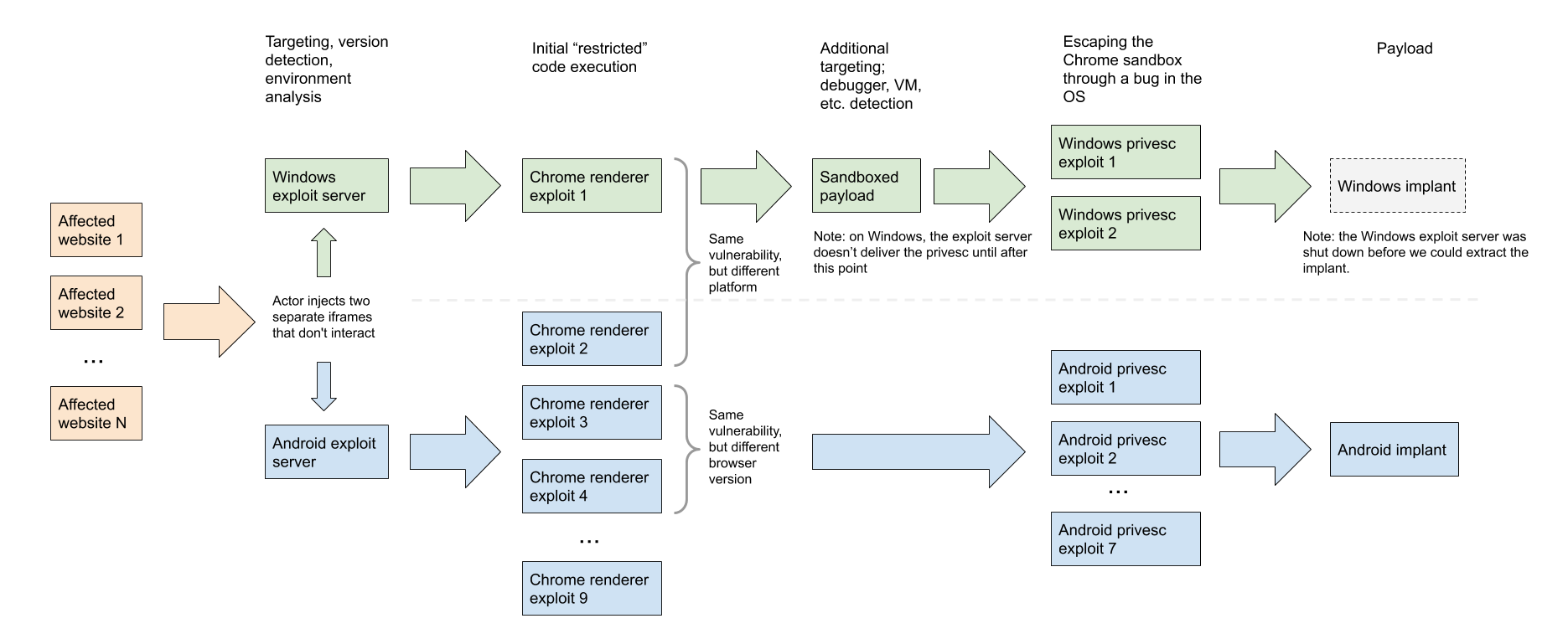
The attacker’s exploit chains presented combinations of zero-day vulnerabilities, as well as other recent issues that the developers have already fixed. So, four errors in Google Chrome were related to the renderer, and one of them at the time of detection was 0-day. In Windows, hackers exploited two zero-day vulnerabilities that allowed them to escape the sandbox.
In addition, the attackers had a “privilege escalation suite” of well-known exploits for known vulnerabilities in Android. At the same time, experts note that the hackers supposedly used 0-day vulnerabilities in Android, they simply did not store exploits for them on the discovered server.
The four above mentioned 0-day bugs are:
- CVE-2020-6418 — Chrome vulnerability in TurboFan (fixed in February 2020);
- CVE-2020-0938 — Windows font vulnerability (fixed in April 2020);
- CVE-2020-1020 — Windows font vulnerability (fixed in April 2020);
- CVE-2020-1027 — Windows CSRSS vulnerability (fixed in April 2020).
Attackers’ exploit chains are described by experts as tools “designed to be more efficient and flexible through their modularity”.
Unfortunately, Google has not yet released any details about the attackers themselves or the victims they targeted.
By the way, as we reported, Gridinsoft becomes Google’s information security partner.




