News, Tips, Security Lab
Texting Spam: How to Stop Spam Text Messages
What does spam mean in texting? Receiving random text messages from unknown numbers is unsettling. But, unfortunately, spam is more…
Difference Between IPSec and SSL
In the last couple of years, remote work has become integral to the world business landscape. However, to make remote…
Raspberry Robin Worm Uses Fake Malware to Trick Security Researchers
The Raspberry Robin worm uses new tactics to evade detection and seeks to confuse security experts if it runs in…
Hackers Attack Ukrainian Organizations through Malicious Windows 10 Installers
Mandiant experts reported that Ukrainian government agencies are suffering from attacks using malicious Trojanized Windows 10 installers, as victims download…
Huge Ransomware List by Gridinsoft Research – Part #2
We talked a lot about notorious ransomware examples in Part #1 of this series. Still, it was not enough to…
Attackers again deceived Apple’s notarization process
In September 2020, I talked about how the Shlayer malware successfully passed the notarization process and was able to run on any Mac running macOS Catalina and newer. Now there…
New T-RAT malware can be controlled via Telegram
G DATA’s specialists have published a report on the new T-RAT malware, which is being distributed for only $45. The main feature of the malware is that T-RAT allows controlling…
Experts discovered that many mobile browsers are vulnerable to url spoofing
Rapid7 analysts and independent information security expert Rafay Baloch discovered that seven popular mobile browsers are vulnerable to url spoofing. They allow malicious sites to change the URL and display…
Google engineers fixed Chrome 0-day vulnerability that was already under attacks
Google engineers have released an updated version of Google Chrome (86.0.4240.111) and warn that they have fixed in browser 0-day vulnerability that has been already under active attacks. The error…
Bughunter stole a Monero exploit from another cybersecurity specialist and received a reward for it
Bleeping Computer reporters drew attention to an interesting case that occurred as part of the bug bounty of the Monero program on HackerOne. Bughunter stole a Monero vulnerability exploit discovered…
P2P botnet Interplanetary Storm accounts more than 9000 devices
Bitdefender experts gave a detailed description of the work of the P2P botnet Interplanetary Storm (aka IPStorm), which uses infected devices as a proxy. According to researchers, the botnet includes…
Google revealed the most powerful DDoS attack in history
This week, the Google Cloud team talked about a previously unknown DDoS attack that targeted a Google service back in September 2017 and peaked at 2.54 TB/sec, making it the…
Google and Intel experts warn of dangerous Bluetooth bugs in Linux
Google and Intel engineers warn of dangerous Bluetooth bugs that threaten all but the latest Linux kernel versions. The bugs are collectively known as BleedingTooth and are associated with the…
Hackers are increasingly using open source tools for attacks
Speaking at the Virus Bulletin conference, Intezer Labs analysts said that hackers are increasingly using open source tools for attacks, and listed freely available tools that hackers majorly abuse. Such…
Attackers can use Windows Update client to execute malicious code
Hackers can exploit Windows Update client to execute malicious code on the system as part of the Living off the Land (LotL) method. The Windows Server Update Services (WSUS)/Windows Update…
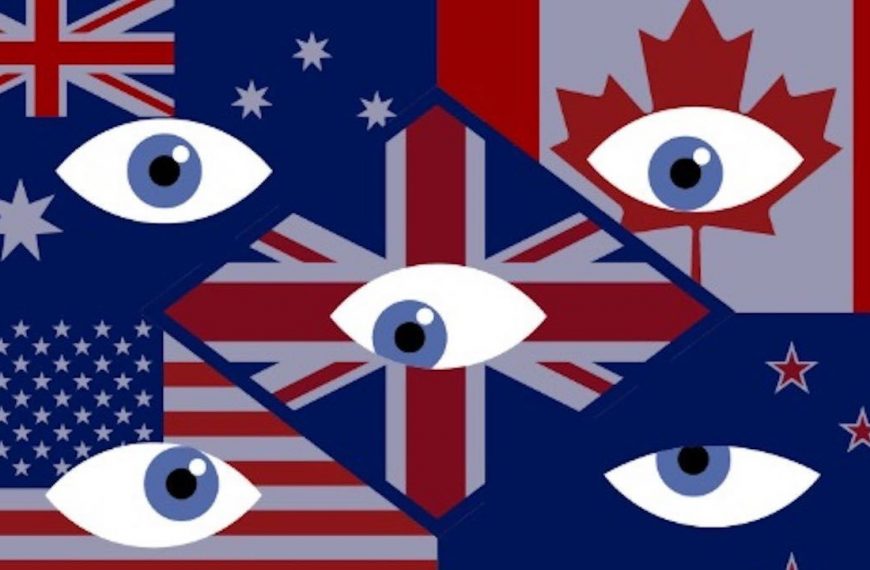
Five Eyes Alliance, India and Japan Call for Backdoors in Software
Countries participating in the Five Eyes Alliance (which brings together intelligence agencies in Australia, Canada, New Zealand, the United States and the United Kingdom), as well as India and Japan,…
MalLocker ransomware easily tricks Russians, pretending to be a screen lock from the police
Microsoft experts talked about the new Android ransomware AndroidOS/MalLocker. (hereinafter simply MalLocker), which easily tricks Russians by pretending to be a screen lock from the police. Android ransomware abuses the…