In September 2020, I talked about how the Shlayer malware successfully passed the notarization process and was able to run on any Mac running macOS Catalina and newer. Now there is information that the attackers again deceived the notarization process.
Apple introduced the “notarization process” security mechanism in February of this year: any Mac software distributed outside the App Store must undergo a notarization procedure so that it can run on macOS Catalina and above.
Unfortunately, just like Bouncer (an automated security system that scans Android apps before uploading them to the Google Play Store), Apple’s app notarization process isn’t perfect either. Thus, in total, more than 40 notarized applications infected with the Shlayer Trojan and BundleCore adware have been detected.
Now, researcher Joshua Long of Intego says that he has identified six more malicious applications that have successfully passed the notarization process.
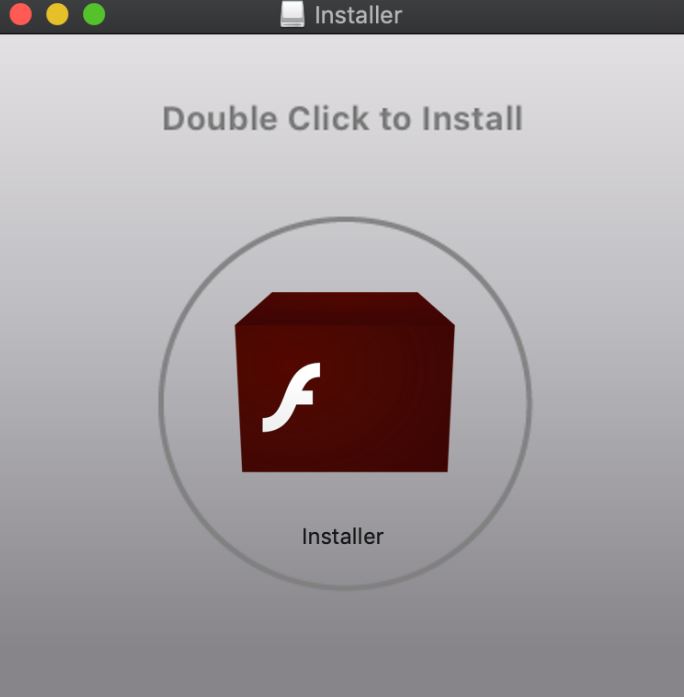
All six found “products” pretended to be Flash installers, but in fact downloaded OSX/MacOffers adware onto victims’ machines, which, in particular, interferes with the operation of the search engine in the user’s browser.
The expert writes that Apple revoked the developer’s certificate for these malwares before Intego specialists had time to finish their investigation. It is unclear how Apple discovered these applications: perhaps the company received a warning from another cybersecurity researcher, or someone from their affected Mac users notified the company of what was happening.
As Adobe, along with other companies, plans to permanently phase out Flash support in late 2020, Long has once again urged users to stop downloading Flash installers, which are usually malicious.




