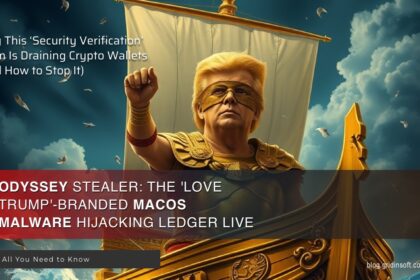
Odyssey Stealer: Russian ‘Love Trump’ Malware Replaces Ledger Live Crypto Wallet App
A new macOS malware campaign is targeting users through social engineering, masquerading…
Critical Vulnerability Uncovered in Apple iOS and macOS Exploited
The Cybersecurity and Infrastructure Security Agency has identified a security flaw in…
RustBucket Malware Attacks MacOS More Effectively
New update of RustBucket Malware introduced several changes. Now the malware is…
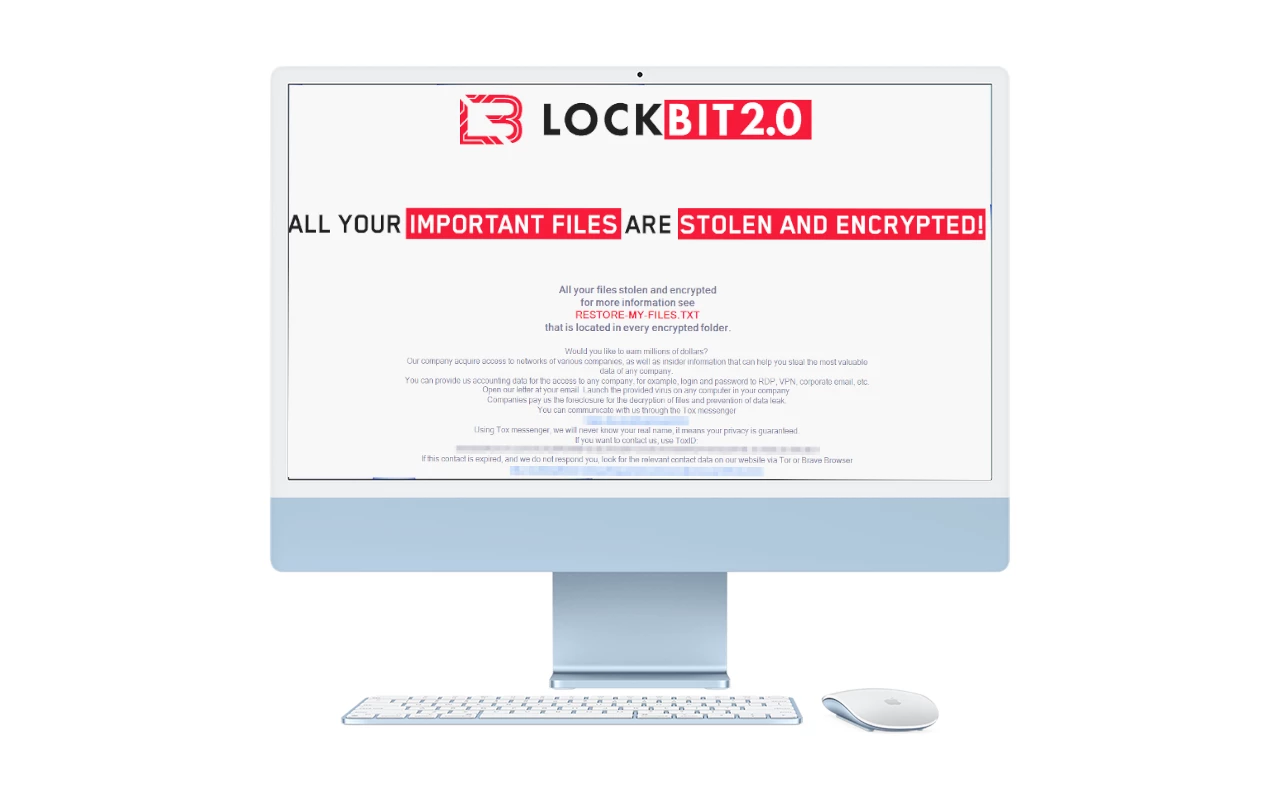
LockBit Releases World’s First macOS Ransomware
LockBit, an infamous ransomware gang that became a major threat actor over…
Lazarus Hackers Attack MacOS Users by impersonating Crypto[.]com
Sentinel One has discovered that the North Korean hacker group Lazarus is…
CloudMensis Malware Attacks MacOS Users
ESET experts have discovered the CloudMensis malware, which is used to create…
Privacy Access Tokens to Replace CAPTCHA Real Soon
CAPTCHA, a well-known test for website visitors to prove they are humans,…
Apple paid $100,000 for macOS camera and microphone hack
Information security researcher Ryan Pickren told how he received a large reward…
Critical vulnerability in Office fixed, but macOS update is delayed
As part of the January Patch Tuesday, Microsoft engineers fixed a critical…
Vulnerability in macOS Leads to Data Leakage
Microsoft said that attackers could use a macOS vulnerability to bypass Transparency,…
Telegram for macOS did not delete self-destructing videos
Telegram developers have fixed a bug due to which self-destructing audio and…
Attackers again deceived Apple’s notarization process
In September 2020, I talked about how the Shlayer malware successfully passed…


![Lazarus Hackers Attack MacOS Users by impersonating Crypto[.]com 10 Lazarus attack macOS users](https://gridinsoft.com/blogs/wp-content/uploads/2022/09/Lazarus-attack-macOS-users.jpg)