Bleeping Computer reporters drew attention to an interesting case that occurred as part of the bug bounty of the Monero program on HackerOne. Bughunter stole a Monero vulnerability exploit discovered by another person and received a reward.
The publication notes that bug hunting is not just a good cause that benefits the community, but also a multimillion dollar industry. As a result, some may try to abuse platforms such as HackerOne and Bugcrowd, designed to foster ethics, trust and accountability among information security professionals, for their own financial gain.
Last weekend, cybersecurity specialist Guido Vranken discovered that an Everton Melo had used a copy of an exploit he had created to report a vulnerability in the Monero bug bounty program on HackerOne. The vulnerability Vranken found in the libzmq 4.1 series back in 2019 was a critical clipboard overflow bug (CVE-2019-6250). The researcher notified the developers about it in January 2019.
“Lol someone literally copied and pasted my libzmq + analysis exploit in the [HackerOne] bug bounty and took the money”, — Vranken wrote on Twitter.
Although HackerOne engineers have previously detected and closed plagiarized reports, there is always the possibility of accidental employee error. Currently, the Monero developers have already reported that they cannot return the amount already paid to the plagiarist:
“This report was stolen (!!) from the original Guido Vranken vulnerability report without any mention of his merits. We overlooked the fact that the report was redrawn from there, as we focused on reproducing the problem and fixing it. This is incredible meanness. Please don’t do this. We contacted Guido to pay him a fee, and unfortunately we cannot withdraw the fee from Everton Melo.”
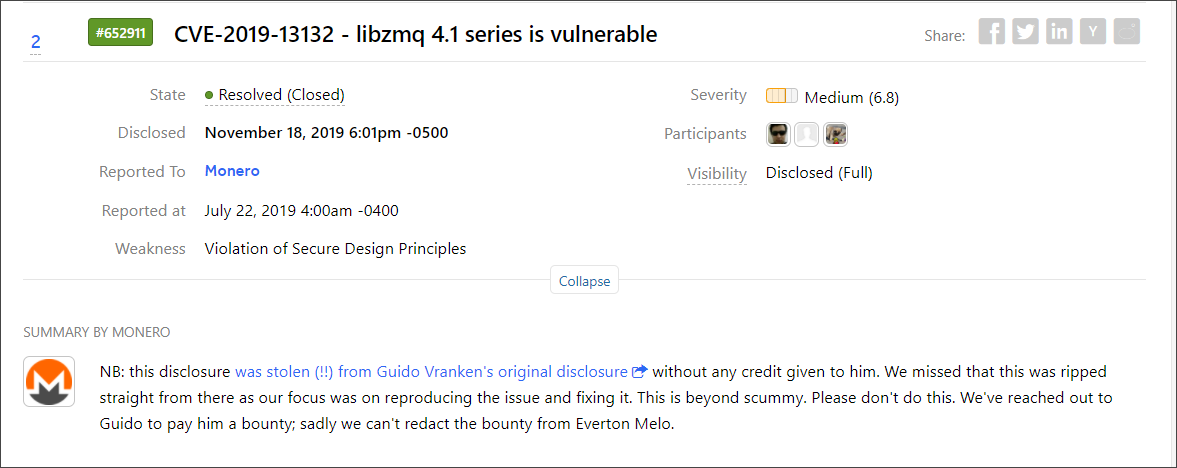
Interestingly, upon closer examination of the report, the developers determined that the 4.1 series, apparently, is not affected by the CVE-2019-6250 problem, but it is definitely vulnerable to the CVE-2019-13132 issue, and therefore it was decided that Melo still has the right for a reward. For the same reason, the title of the report on HackerOne was changed to CVE-2019-13132 instead of CVE-2019-6250.
Let me remind you that Google recruits a team of experts to find bugs in Android applications.