Microsoft has released its monthly security update, addressing 142 vulnerabilities across its product suite and software. One of these vulnerabilities is already being exploited in the wild. The vulnerabilities were fixed as part of Microsoft’s monthly bug fix release, widely known as “Patch Tuesday”.
Microsoft Fixed 3 Critical Flaws in Patch Tuesday
In the most recent Patch Tuesday, on July 10, 2024, Microsoft released fixes for 142 security issues in its product suite and software. Among them are 6 flaws of different severity – CVE-2024-38023, CVE-2024-38060, CVE-2024-38080 and RCE bugs CVE-2024-38074, CVE-2024-38076, and CVE-2024-38077. The latter three have a CVSS score of 9.8 and allow an attacker to send specially crafted network packets that could trigger remote code execution in the Windows Remote Desktop Licensing service. Moreover, the last vulnerability does not require authentication, making it particularly dangerous.
Notably, this is the largest list of fixes in recent months, nearly matching the April patch release where Microsoft fixed 150 vulnerabilities. The patches address vulnerabilities affecting multiple segments of Microsoft products. These include Windows, Office, Azure, .NET, Visual Studio, SQL Server, and Windows Hyper-V. In particular, one of the vulnerabilities is already being actively exploited in real-world attacks.
CVE-2024-38074, 38076, and 38077 Details
Despite all of the RCE flaws being rated at CVSS 9.8, some of them require authenticated access or specific privileges to exploit. For instance, a vulnerability in Microsoft SharePoint Server requires site owner rights to execute arbitrary code. One of the most significant vulnerabilities is an issue in Windows Hyper-V, which allows attackers to gain system privileges. To understand the severity of these vulnerabilities, let’s delve into the details.
CVE-2024-38023 vulnerability allows attackers with site owner rights in Microsoft SharePoint Server to execute arbitrary code on the server. An attacker with the necessary privileges can use specially crafted commands to execute code in the context of SharePoint Server. This vulnerability is particularly dangerous because it can lead to complete control over the server and leakage of confidential information.
Another remote code execution vulnerability (CVE-2024-38060) stems from the flaw in Microsoft Windows codec library. It allows an attacker to upload a specially crafted TIFF file, which, when processed by the system, will trigger arbitrary code execution. However, to exploit this vulnerability, the attacker must have access to the system, making it less dangerous than remote attacks, but still posing a significant risk.
The third vulnerability, CVE-2024-38080, is already actively exploited in real-world attacks. Attackers can use this vulnerability to escalate privileges in Windows Hyper-V, gaining access to system-level privileges. This can lead to complete control over virtualized environments, posing a serious threat to the security and integrity of the systems.
How to Stay Safe?
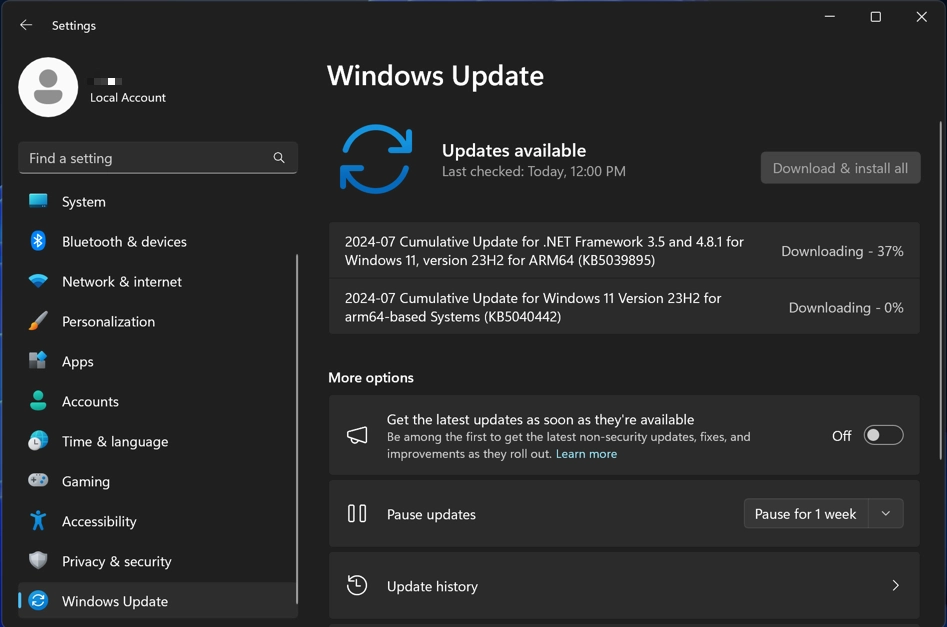
Vulnerabilities are an inherent part of software — past, present, and future. The only effective method to mitigate their risks is timely patching. To minimize these risks, Microsoft strongly recommends promptly installing the latest updates that address these vulnerabilities. And, well, despite the fact that Redmond tries its best to fix all the known flaws in time, there may be slip-throughs, even ones that exist for over a year.
Another layer of protection against exploitation is a zero-trust anti-malware solution. Not much are available for home users, but vulnerability exploitation typically targets systems from corporate networks to begin with. A sturdy solution that will do a thorough check to every action from any software, which is the essence of zero trust policy, is what has the best efficiency against such attacks.




