Researchers at NVISO Labs noticed that the Epic Manchego group uses unusual Excel files for attacks, created specifically to bypass defense mechanisms. The fact is that these files are not created through Microsoft Office – the hackers use the .NET library EPPlus.
Typically, this library is used by application developers, for example, to add features such as “Export to Excel” or “Save as Spreadsheet”. The library can be used to create files in a wide variety of formats and supports Excel 2019.
“Hackers seem to be using EPPlus to create spreadsheets in Office Open XML (OOXML) format. The files produced by Epic Manchego are missing some of the VBA code typical of Excel documents compiled in official Microsoft Office”, – experts write.
It turned out that some antivirus products and email scanners consider this part of the VBA code as one of the possible signs of a suspicious Excel file, because, as a rule, this is a storage for malicious code . Therefore, Epic Manchego special files are much less likely to be detected by security solutions (compared to other malicious Excel files).
Of course, this does not mean that Epic Manchego files are completely harmless. Although the files worked correctly, like any other Excel document, experts explain that cybercriminals store malware in them using a custom VBA code format, which is also password protected so that security systems and information security specialists cannot analyze the content.
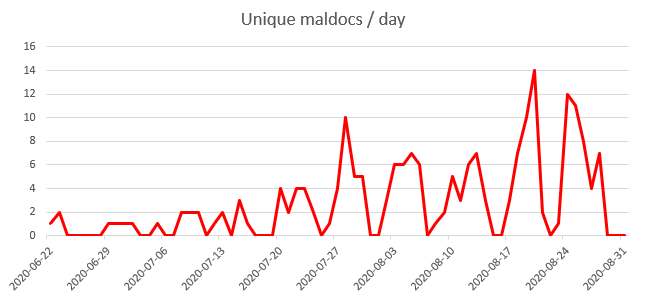
Analysts point out that using EPPlus not only helped, but also hurt Epic Manchego. The fact is that experts were able to detect numerous past grouping operations by simply looking for unusual Excel files. As a result, more than 200 files related to Epic Manchego were discovered, the first of which dates back to June 22 of this year.
As you might guess, such malicious documents contain malware’s macro script. For example, if the victim opens the Excel file and allows execution of the script, the macros will download and install malware on their machine.
Payloads in this case are classic infostealer Trojans such as Azorult, AgentTesla, Formbook, Matiex and njRat, which steal passwords from browsers, mail and FTP clients and send them to Epic Machengo servers.
It is worth noting that, in general, NVISO Labs experts were not surprised that the hack group was using EPPlus for attacks. They write:
“We have been familiar with this .NET library for a long time, as we have been using it for several years to create malicious documents for our red team and pentesters”
Not only Excel users are under attack, I recently wrote that hackers use in attacks malicious plugin for 3Ds Max, and even hackers force users to solve CAPTCHA.




