What’s the Idea Behind Password Managers?
In the cybersecurity world, everyone knows that passwords are real. It’s only in the movies hackers can effortlessly detour or hack passwords. A strong password provides decent data protection.
Since an average internet user nowadays has many accounts on different online services, remembering passwords becomes a serious nuisance. Using services other than social media or email becomes inseparable from a boring “forgot password” procedure.
To stop these work process disruptions and at the same time improve data security, people invented password managers. Are they secure, and should you use them? That’s what this post is about.
Is it Safe to use Password Managers?
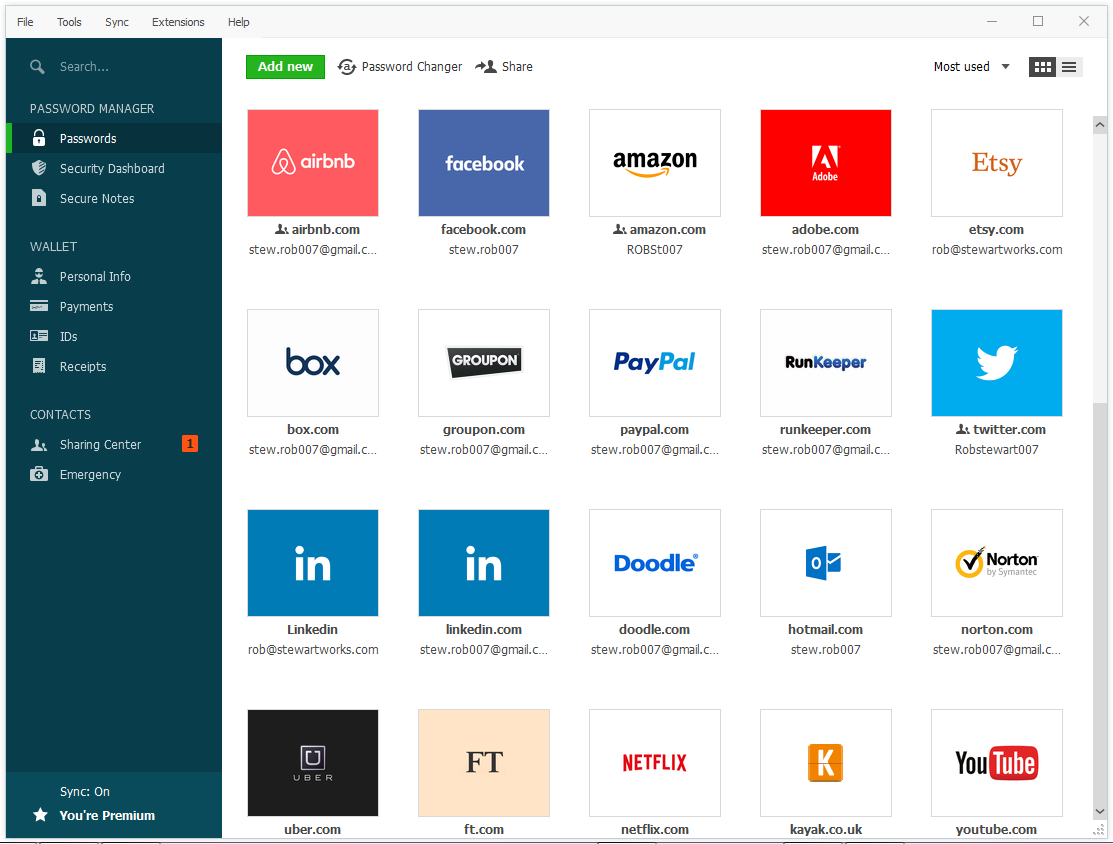
The programs in question store passwords from different accounts and automatically fill them into the respective websites’ log-in forms. They also generate strong passwords for each account, saving the user the trouble of doing it. Thus, clients keep all their extremely strong passwords in one box and benefit from forms auto-filling. That does not sound secure at all, you might say, and you would be surely right. If not for certain security measures in password managers, the disputed services would rather jeopardize passwords than manage them wisely. Having all keys collected together without proper protection would make them easy prey.
However, there are high-end programs among password managers that feature security mechanisms making digital fortresses out of them. That doesn’t mean that all safety issues are solved, that is not so (we’ll talk about that further,) but in most cases, a password manager can be helpful and handy.
Security Features
- The first thing that must be said is that password managers use the so-called zero-knowledge architecture. That means no person except you know your passwords stored in the password manager’s vault. The manager doesn’t “know” them either because all the passwords are encrypted and protected by the master password, which is not stored in the vault. You know it, and it belongs to you.
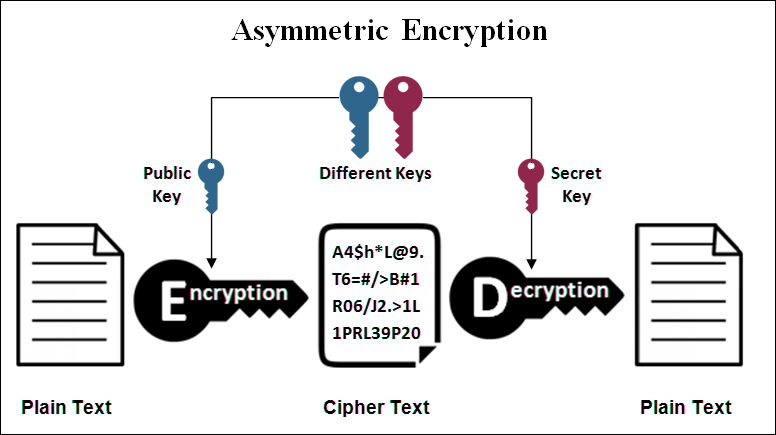
- By the way, the vault is cloud storage. Any connection between your PC and the cloud is encrypted. It is called end-to-end encryption. We have described how such encryption works in our post on SSL certificates. The principle for establishing secure connections is the same – a combination of asymmetric and symmetric encryption. Briefly speaking, should hackers even get the data stored on password manager’s cloud servers, they won’t be able to do anything with it.
- Surely, password managers will audit your credentials, change them regularly, warn you about any weaknesses in your password-login combinations, and so on.
- Logging into the manager program can be accompanied by two-factor authentication to make it as secure as possible. 2FA means you will confirm your identity via another device as you log in and enter your master password.
- Although data breaches are unlikely and pointless since there is end-to-end encryption, some password manager manufacturers monitor the Internet to detect any leakages or breaches if they happen, to inform users about them ASAP.
If you make up your mind to purchase a password manager, make sure the program you have chosen supports the features mentioned above.
Can Password Manager Still be Hacked?
Master Password – the Key to the Kingdom
Theoretically, a password manager hack is possible, although extremely unlikely. Moreover, the target of such an attack will definitely not be the cipher used in the vault itself. Attackers will need your master password, the code that will open the chest with the rest of your keys from different accounts. Most likely, hackers will seek a vulnerability in your habits and use social engineering. By the way, they may try to get your password out of you, posing as the developers of your password manager.
Making Your Master Password Strong
Therefore, we will still have to briefly say here that for a password to be strong, it must be composed of numbers, letters of both cases, and special characters. And, of course, it must be a long sequence of characters (at least twelve.) In addition, the password should not be based on some word with meaning because criminals often go for spear attacks. Those are personalized attacks; when they know something about the victim. Accordingly, neither names nor anyone’s dates of birth should appear in the password. Understandably, no one shouldF be given the key from the password manager. By the way, consider reading the guide to creating strong passwords on our blog.
What About Malware
But that’s not all, because we should not forget about malicious programs. If we just assumed that hackers might be trying to crack your password using brute force, then we need to know that they can go the easier way. They can infect your device with spyware! Moreover, we don’t mean spyware that collects some data in the background while you are browsing the network. No, now we are talking about the most dangerous programs, which are sometimes also classified as spyware, namely keyloggers and screen loggers. The first ones capture keystrokes, while the second ones send everything that happens on your screen somewhere to the attackers’ server. If you use a virtual keyboard, the keylogger is not dangerous for you, but there is still no way against the screen logger.
Both these programs can be hidden from human eyes with the help of a rootkit – another powerful hacker tool. Such programs on your computer would indicate that it has been at risk all this time.
Security Solutions
However, to prevent malware from penetrating your device, and to remove it, should it infect your machine, there are antiviruses, such as GridinSoft Anti-Malware. It is a great program that has three types of protection. On-run protection, deep scanning, and browsing protection are also very important. The first function destroys the infection on approach. The second one, scan, will help you find well-hidden malware. The last feature mentioned is blocking and warning about malicious sites.
Unquestionable Benefits of Password Managers
Although we can never rule out the above-mentioned threats, they are unlikely to happen. If we discard them, we will have to admit that password managers possess some unquestionable benefits for the user. At least in comparison with the password policy of an average Internet user.
- Increased security! Undoubtedly, the machine generates strong passwords better than humans, and the program makes them unrelated to any meaning. Also, manager software stores your credentials flawlessly, keeping them protected with the highest level of security. A 256-bit AES encryption is no joke; we can count it unbreakable, at least for today.
- Password managers matchless ease browsing and Internet activities. On the one hand, your data becomes more protected. On the other hand, all this password-related fuss leaves you with a boring dream. You don’t need to invent passwords. Note them somewhere, just in case, forget them later, and reset them to access your account.
- Password managers are an effective countermeasure against phishing and, more specifically, website spoofing. A well-made fake website can catch even an experienced user off guard. Imagine you run onto a typo-squatting webpage that looks just like a website you intended to visit. You haven’t noticed your typo, and as the site fully loads, you see the familiar appearance of the sign-in form. There is a high chance that the user here would notice no pitfall, let alone if tired, and input the login and the password right into the password-stealing form prepared by malefactors. However, a problem for a human is not a problem for a machine at all. You will notice if your password manager suddenly refuses to fill out the credentials form automatically. And it won’t, of course, if the website address is different, even if it is a one-character difference.