It is important to exercise caution when using messenger mods. There have been reports of spyware disguised as modified versions of Telegram on the Google Play Store. This malware designed to extract sensitive information from compromised Android devices. Despite these risks, many users still blindly trust any app verified and published on Google Play. We have repeatedly warned about the dangers of downloading apps from Google Play. It could result in inadvertently downloading a Trojan, a backdoor, a malicious subscriber, and other harmful software.
Trojanized Telegram Clients Spread on Google Play
Telegram’s Play Store version is identified with the package name "org.telegram.messenger," while the direct APK file downloaded from Telegram’s website is associated with the package name "org.telegram.messenger.web". Malicious packages named “wab,” “wcb,” and “wob” were used by threat actors to trick users into downloading fake Telegram apps. Despite looking like the authentic Telegram app with a localized interface, infected versions contained an additional module. That was missed by Google Play moderators. A few days ago, experts revealed that a malware campaign called BadBazaar was using such rogue Telegram clients to gather chat backups.
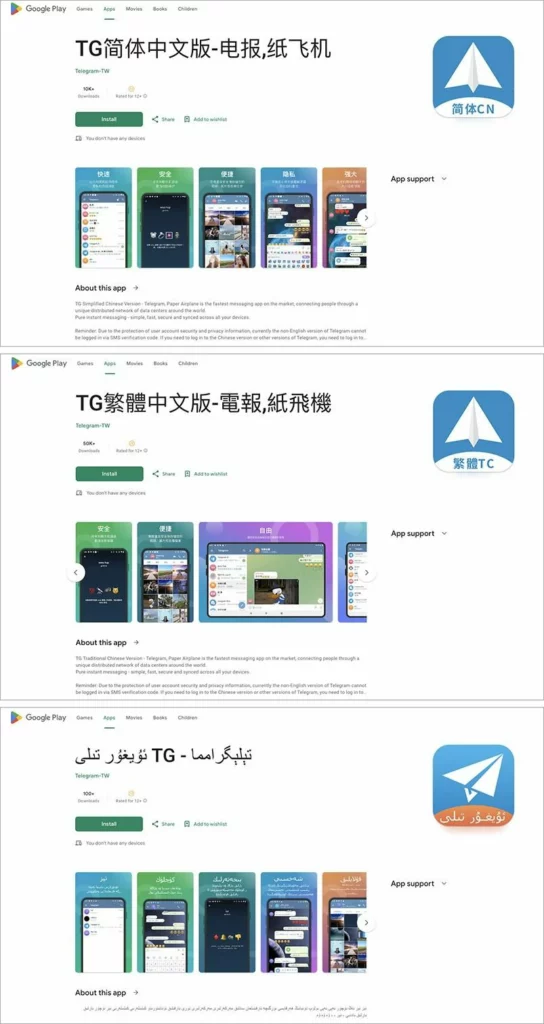
Examples of fake Telegram apps:
Security experts have recently discovered a number of malicious apps on Google Play that claim to be versions of Telegram in Uyghur, Simplified Chinese, and Traditional Chinese languages. These apps have descriptions written in their respective languages and contain images that are very similar to the official Telegram page on Google Play, making it difficult to distinguish them from the genuine app.
The devs of these fake apps promote them as a faster version of a regular client, citing a distributed network of data centers worldwide. They use this as bait to persuade users to download the mods instead of the official Telegram app.
How dangerous are fake Telegram apps?
Millions of users have downloaded apps that were found to have malicious features. Among other things, malicious copies have functionality to capture and transmit sensitive information such as names, user IDs, contacts, phone numbers and chat messages to a server controlled by an unknown actor. Experts who discovered this activity have codenamed it Evil Telegram. Google has since taken down these apps from its platform.
Nonetheless, the poor app moderation problem in Google Play has persisted for almost a decade. You can upload literally whatever you want – even malware – and it may be deleted only after numerous reports saying it is malicious. And there’s still no guarantee that the reports will be processed in a suitable time; some rogue apps remain in GP for months. For that reason, the threat will most probably resurface later, especially considering the growing popularity of Telegram.
How to stay safe?
Here are some important tips to keep yourself safe from infected versions of popular messaging apps and other threats that target Android users:
- As I’ve just said, Google Play isn’t completely immune to malware attacks. However, it’s still a much safer option than other sources, so always download and install apps from official stores.
- Before installing any app, even from official stores, please take a closer look at its page and ensure it’s legitimate. Pay attention to the app’s name and developer. Cybercriminals frequently apply typosquatting or spoofing in order to spread their malware.
- Reading negative user reviews is a good way to identify potential issues with an app. If there’s a problem with an app, someone has likely already written about it. Also try searching for reviews on the web. There are plenty of sites where you can leave your feedback without any censorship from the developer or Google. Using several independent sources will give a more clear view.




